Colonial Pipeline and Irish Healthcare System Cyberattacks Force Changes In Cybersecurity Protocols
 This week, the Department of Homeland Security (DHS) set forth new guidelines related to cybersecurity procedures in the event of a hack against any of the nation's leading pipeline companies. The announcement comes on the heels of the devastating Colonial Pipeline hack, executed by the DarkSide ransomware gang, that affected nearly half of the East Coast's fuel supply for 11 days. Previously, voluntary guidelines had been provided to leading companies in the fuel industry.
This week, the Department of Homeland Security (DHS) set forth new guidelines related to cybersecurity procedures in the event of a hack against any of the nation's leading pipeline companies. The announcement comes on the heels of the devastating Colonial Pipeline hack, executed by the DarkSide ransomware gang, that affected nearly half of the East Coast's fuel supply for 11 days. Previously, voluntary guidelines had been provided to leading companies in the fuel industry.
This new DHS directive will require pipeline businesses to report any cyber incidents to federal authorities. It also follows a recent disturbing trend of new ransomware attacks, beyond just the Colonial hack, that have highlighted cyber vulnerabilities to critical infrastructure in not just the United States, but internationally as well.
While the Cybersecurity and Infrastructure Security Agency (CISA), a subdivision of DHS, is tasked with providing guidance to the American private sector businesses that handle US infrastructure, there aren't many federal requirements for them to maintain cybersecurity measures.
New Cybersecurity Infrastructure Changes Could Thwart Future Ransomware Attacks
As a result of the newly announced changes, close to 100 pipeline companies are now required to keep a cybersecurity coordinator available at all times, and to begin reporting any and all incidents to CISA within 12 hours.
Additionally, pipeline businesses that fail to comply with the new rules would face escalating fines that start around $7,000.
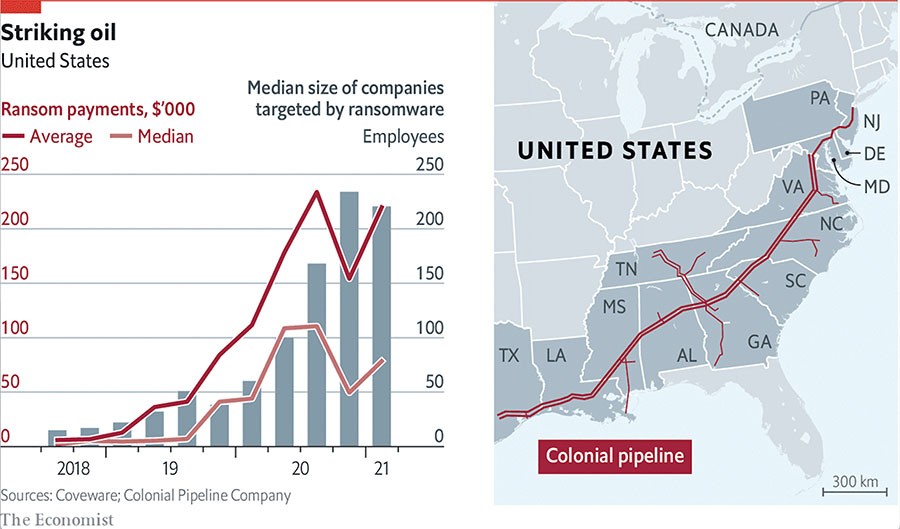
Thwarting ransomware attacks could be greatly beneficial to organizations in the case that they don't have to pay the cybercrooks ransoms to get their operations back online. Such ransom fees can amass to hundreds of thousands of dollars to nearly millions, as the "Striking oil" chart below demonstrates in the payout amounts for various size companies targeted by ransomware.
Across the pond in Ireland, the Irish health care system was also recently hit with a major ransomware attack in mid-May that forced its hospital system to shut down IT networks and and locked many healthcare facilities out of their computers.
The ransomware specifically targeted Ireland's Health Service Executive decided to shut down most IT systems for precautionary reasons.
As a result of this and another previous hack against the Irish healthcare system, cybersecurity is now under a continuous state of review across all state agencies according to Irish prime minister Micheál Martin.
Martin said cyberattacks are a very significant threat to both the state and the private sector and that the government's response would be "steady and methodical".
Martin also claimed that it was possible that patient data had been compromised and that IT staff were assessing the full scope of the event.
"It's a heinous attack, it's a shocking attack on a health service, but fundamentally on the patients and the Irish public," Martin stated.
The attack against the Irish healthcare system is believed to be the work of the 'Wizard Spider' hacking group, from Eastern Europe and was reminiscent of the 2017 WannaCry ransomware attack against the UK's Healthcare system.