Chthonic
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 283 |
| First Seen: | January 21, 2015 |
| Last Seen: | January 24, 2022 |
| OS(es) Affected: | Windows |
Chthonic is a recent variant of the treacherous Zeus Trojan, a well-known banking Trojan. Strains of Chthonic first started to appear in late 2014. Chthonic targets online banking clients and is a new variant of the Zeus Trojan, which is one of the most widespread banking Trojans in history. Chthonic has plagued more than 150 distinct banks and 20 payment platforms, spread over fifteen different countries. Chthonic has been most active in the United Kingdom, the United States, Japan, Spain, Italy and Russia. Chthonic can use the affected computer's webcam, keyboard, and other components to collect online banking passwords and credit card numbers. Chthonic allows third parties to control an infected computer remotely in order to carry out banking transactions without the computer user's knowledge. These are all features that were present in previous banking Trojans. However, what makes Chthonic stand out is the way Chthonic inserts its own code into victims' Web browsers.
When the infected computer's browser visits an online banking website, Chthonic collects the victim's data, including passwords, PINs, login details and other retrievable data. Chthonic is spread using corrupted email attachments. These use threatening DOC and RTF documents that are designed to take advantage of the CVE-2014-1761 vulnerability that is present in Microsoft Office. As soon as the threatening file is downloaded, it installs several threatening components on the victim's computer. These components, all modules of the Chthonic banking Trojan are capable of spying on the victim's computer, log keystrokes, allow remote access to the infected PC, record sound and video using the infected computer's camera and microphone, and a variety of other tasks.
Table of Contents
Why Chthonic is Considered Particularly Threatening
Most reliable, fully updated security programs are capable of dealing with the Zeus Trojan and its many variants. After all, there is a long time that a Trojan infection has been challenging malware researchers. However, there are several interesting aspects of Chthonic that make Chthonic particularly threatening. Chthonic uses several techniques to load its threatening components and infect victims' computers. Chthonic also targets a particularly large number of online banks and payment platforms. There are several significant changes in Chthonic when compared to ZeusVM and other Zeus precursors of this threat infection.
Apart from threatening email messages, the Chthonic has been associated with the Andromeda bot, another threat infection that is being used to distribute Chthonic and other threats. Threatening files associated with Chthonic are often hosted on compromised websites – that is, websites that are normally not threatening but that have been hijacked by third parties in order to distribute threats without being traced to the original source. Many banks create warnings to ensure that computer users are not tricked by various types of phishing and threats approaches. However, Chthonic may hide the banks' warnings and replace the banks' websites with its own fake versions that have the same size as the original window (meaning that the victims will not be aware of the additional window on their Web browsers).
Although Chthonic incorporates many techniques that are no longer viable due to banks' security measures (probably remnants of previous versions of this threat infection), it is particularly surprising the quantity of banks targeted by Chthonic, often with different, specific techniques for different banks. For example, Chthonic may employ certain approaches specific to Russian banks (fake versions of the bank's login page) while using a completely different strategy when it comes to certain Japanese banks. Chthonic is evidence that the Zeus Trojan is still evolving, and that threat creators are still in an arms race to outsmart PC security experts.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Generic_r.EGD |
| Fortinet | W32/Foreign.CNVK!tr |
| Ikarus | Trojan-Ransom.Win32.Foreign |
| AhnLab-V3 | Trojan/Win32.Generic |
| Microsoft | Trojan:Win32/Dynamer!ac |
| Antiy-AVL | Trojan[Ransom]/Win32.Foreign |
| Sophos | Troj/Wonton-FZ |
| McAfee-GW-Edition | BehavesLike.Win32.PWSZbot.cc |
| DrWeb | BackDoor.Andromeda.541 |
| Comodo | UnclassifiedMalware |
| Kaspersky | Trojan-Banker.Win32.Chthonic.e |
| Avast | Win32:Malware-gen |
| Symantec | Trojan.Zbot |
| K7AntiVirus | Trojan ( 004afbf31 ) |
| McAfee | Generic PWS.o |
SpyHunter Detects & Remove Chthonic
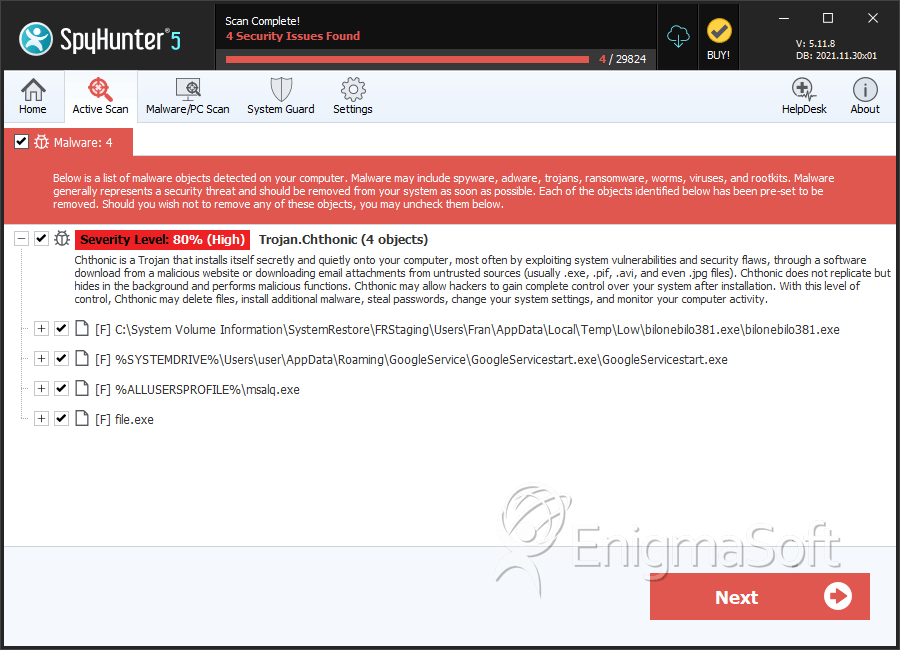
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | bilonebilo381.exe | 9cc129b0e8acaa0cf9c61041a7b247aa | 113 |
| 2. | TelltaleGamesy.exe | b400a69103795a07590fd6b97c142303 | 10 |
| 3. | msalq.exe | 5a1b8c82479d003aa37dd7b1dd877493 | 1 |
| 4. | file.exe | 742bd02d5f54998220660d74b301cc2f | 0 |
| 5. | file.exe | 7bd67403cc46251d406394b611e43b98 | 0 |
| 6. | file.exe | cc6f5c0bcf817aa2d6b3f1b6ffb55769 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.