Chip (MedusaLocker) Ransomware
Protecting endpoints against modern malware has become a fundamental requirement for both individuals and organizations. Ransomware campaigns continue to evolve in complexity, combining strong encryption, data theft, and psychological pressure to maximize impact. One particularly sophisticated strain drawing attention from analysts is Chip Ransomware, a threat linked to the notorious MedusaLocker family.
Table of Contents
Threat Overview: A MedusaLocker Variant with Enhanced Impact
Chip Ransomware was identified during an investigation into high-risk malware samples and has been confirmed as a variant within the MedusaLocker lineage. This classification is significant, as MedusaLocker-based threats are known for coordinated double-extortion tactics, robust encryption routines, and enterprise-targeted campaigns.
Once deployed, Chip encrypts user files and appends the '.chip1' extension to compromised data. The numerical suffix may vary, potentially reflecting different campaign builds or victim identifiers. For example, files such as '1.png' are renamed to '1.png.chip1,' and '2.pdf' becomes '2.pdf.chip1.' In addition to altering file extensions, the ransomware drops a ransom note titled 'Recovery_README.html' and modifies the desktop wallpaper to reinforce the attack's visibility and urgency.
Encryption Mechanics and Psychological Coercion
Chip's ransom note claims that files are encrypted using a combination of RSA and AES cryptographic algorithms. This hybrid encryption approach is typical of high-end ransomware operations: AES is used for fast file-level encryption, while RSA secures the symmetric keys, making brute-force recovery infeasible without the private key controlled by the attackers.
The note emphasizes that files are not 'damaged' but 'modified,' warning victims against using third-party recovery software or renaming encrypted files. Such warnings are designed to discourage experimentation and increase the likelihood of ransom payment. Victims are told that no public decryption tool exists and that only the attackers can restore access.
Compounding the threat, Chip operators claim to have exfiltrated sensitive data to a private server. If payment is not made, the stolen information may be published or sold. This double-extortion strategy significantly increases pressure, particularly for businesses concerned about regulatory exposure and reputational damage.
Victims are instructed to initiate contact via email at 'recovery.system@onionmail.org' or through the qTox messaging platform using a provided ID. A strict 72-hour deadline is imposed, after which the ransom amount is allegedly increased.
Recovery Challenges and Operational Risks
In most ransomware incidents, recovery without paying the ransom is possible only if reliable, unaffected backups are available. When such backups do not exist, victims are placed in a difficult position. Even then, paying the ransom offers no guarantee that a working decryption tool will be provided. Numerous documented cases demonstrate that attackers may disappear, demand additional payments, or supply faulty decryptors.
Immediate removal of Chip Ransomware from infected systems is critical. If left active, the malware may continue encrypting newly created or connected files and could potentially spread laterally across shared network resources. Prompt containment reduces the blast radius and prevents additional data loss.
Infection Vectors: How Chip Gains Access
Chip Ransomware leverages common but highly effective distribution methods. Phishing emails remain a primary delivery channel, typically containing malicious attachments or embedded links. These files often masquerade as legitimate documents but conceal executable payloads, scripts, or weaponized archives.
Other propagation techniques include:
- Exploitation of unpatched software vulnerabilities
- Fake technical support schemes
- Bundling with pirated software, cracks, or key generators
- Distribution through peer-to-peer networks and unofficial download portals
- Malicious advertisements and compromised websites
The malicious payload is frequently embedded within executable files, compressed archives, or documents such as Word, Excel, or PDF files. Once the victim opens or enables content within the file, the ransomware activates and begins its encryption routine.
Strengthening Defense: Essential Security Best Practices
Effective defense against sophisticated ransomware like Chip requires a layered and proactive security strategy. Users and organizations should implement the following measures:
- Maintain regular, offline, and tested backups of critical data.
- Keep operating systems, applications, and security software fully updated.
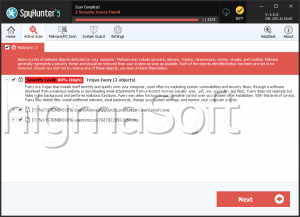
- Deploy reputable endpoint protection solutions with real-time monitoring.
- Disable macros in Microsoft Office documents by default.
- Restrict administrative privileges and apply the principle of least privilege.
- Implement network segmentation to limit lateral movement.
- Train users to identify phishing attempts and suspicious attachments
Beyond these measures, continuous monitoring and incident response preparedness are essential. Organizations should establish a clear response plan outlining isolation procedures, forensic analysis steps, and communication protocols. Logging and centralized monitoring systems can help detect anomalous activity early, potentially stopping encryption before it completes.
In a threat landscape defined by increasingly aggressive ransomware campaigns, vigilance and preparedness remain the most effective defenses. Chip Ransomware exemplifies the convergence of strong cryptography, data exfiltration, and extortion tactics. A disciplined cybersecurity posture, combined with informed user behavior, significantly reduces the likelihood of successful compromise and long-term operational disruption.