Bydes Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | May 28, 2022 |
| Last Seen: | May 28, 2022 |
| OS(es) Affected: | Windows |
The Bydes Ransomware is a harmful threat used by cybercriminals to extort money from targeted users. The threat operates as typical ransomware - it runs an encryption routine on the breached devices that will lock most of the data stored there. The victim's documents, archives, databases, photos, images, etc. will no longer be accessible or useable. After encrypting a file, the Bydes Ransomware will copy it on the system. These copies have '.bydes' appended to their names as a new file extension. Finally, the threat will generate a pop-up window containing a ransom note with instructions from its operators.
Table of Contents
Ransom Note’s Details
The pop-up window's message states that the only way to restore the affected files is to pay the attackers. In exchange, they promise to send back the necessary decryption key. Victims are given exactly 48 hours to restore their data with the pop-up window showing the end date and a countdown. After that period, all encrypted files will supposedly be deleted. Victims also are given the chance to decrypt one file for free. However, the chosen file must be less than 10KB in size. One immediately obvious problem is that the note fails to provide any ways to contact the attackers as the placeholder 'NAME' on 'PLATFORM' have not been substituted with the attackers' information.
The full text of the note is:
'bydes
Your Files have been Encrypted!
WHAT HAPPENED?
Your important files are encrypted with military-grade encryption.
Read this carefully before doing anything, as your files depend on you and your actions entirely.CAN I GET THEM BACK?
Yes, you can get them back.
You won't be able to revert them to their original state without our key.
If you wanna get your files back, follow the steps below.HOW DO I GET THEM BACK?
It's easy and effortless, just follow the instructions.
Contact NAME on PLATFORM with your identifier and we'll help you get your files back.
Upon receiving your key, press "Decrypt" and fill in the key, your files will then be decrypted shortly.IS THERE ANYTHING ELSE I SHOULD KNOW?
If you don't believe we can get your files back, you can try the decryptor below and choose to decrypt one file under 10KB.
Your files will be deleted after 48 hours if you don't decrypt your files in time.
It's strongly advised that you don't modify any encrypted files, try to delete or terminate this program and disable your antiviruses to ensure that your files won't be lost.Good luck!'
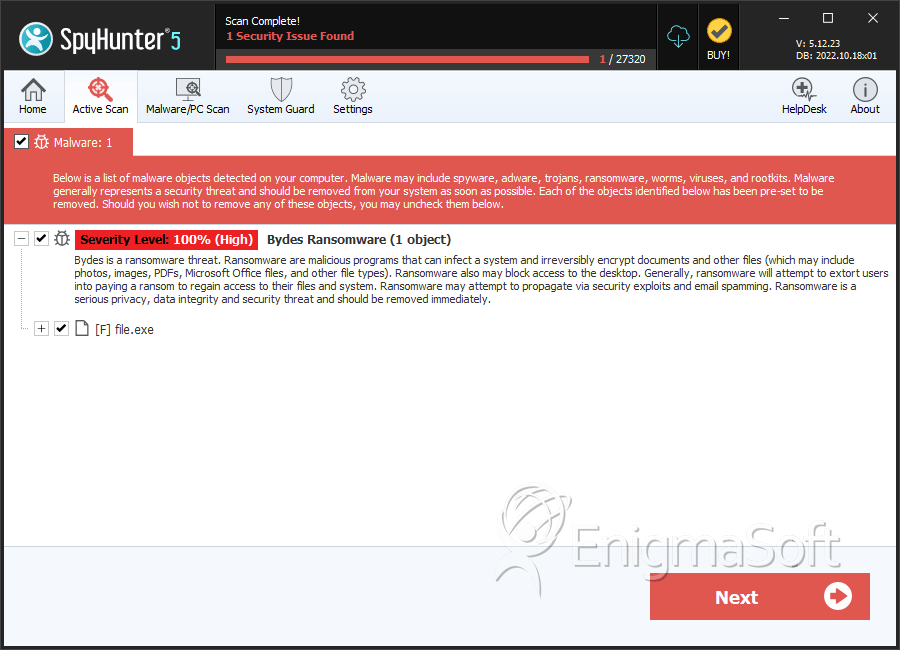
SpyHunter Detects & Remove Bydes Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | bc52d18853a6b575d319692ae8f90fd7 | 1 |

