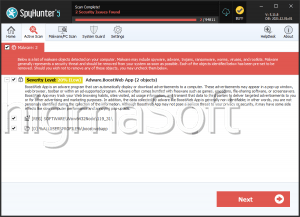
BoostWeb App
The BoostWeb App is an adware that may deceive the PC users about its true functionality. The official page of this suspicious add-on states that it will improve the browsing experience of its clients significantly. In reality, the feedback of the users says otherwise. The reason for the discontentment is the presence of many unrequested advertisements, which may appear on every Web page. These commercial elements may take the shape of pop-ups, banners, in-text and interstitial ads, and display seemingly good deals. The nature of the offered products may be based on some private information – such as the sites you prefer to visit and the information you search. As a result of this adjustment, the sponsored products may seem to be just the thing you need. However, if you click on the corresponding pop-up or banner, you may land on an unknown shopping site. This occurrence may be expected since famous sites don't rely on such ways to boost their popularity. When the sponsored page is unknown to the public, nothing can guarantee that it is safe. There are cases when people have been involved in hoaxes after clicking on such ads, so you should stay away from them. Even if you do, BoostWeb App may still ruin your online sessions as its processes happen thanks to system resources. For that reason, you may experience some random freezes or occasional crashes. To block the loading of the unrequested ads, you should delete the adware wholly, and to achieve this task is with a special security application because otherwise some files may remain.
Table of Contents
Analysis Report
General information
| Family Name: | Adware.BoostWeb App |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
3f27d96ab1a0c40f4433f0ba5fdc929f
SHA1:
8b79f2e10076c0bfcee6d1c74105bda6d970e678
SHA256:
B2CB541C1E69DE16C48E579A1DAE7DF35BA773A65D0F807B269B5BB39F192E51
File Size:
871.22 KB, 871224 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Product Name | Boost |
| Product Version | 3.0.0.27 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Boost Shopping | VeriSign Class 3 Code Signing 2010 CA | Self Signed |
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsxa777.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsxa7c6.tmp\modern-header.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsxa7c6.tmp\modern-wizard.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsxa7c6.tmp\nsdialogs.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsxa7c6.tmp\system.dll | Generic Write,Read Attributes |