Black Kingdom Ransomware
Black Kingdom Ransomware Image
The Black Kingdom Ransomware is a brand-new file-locker that also is known as DEMON Ransomware or DemonWare Ransomware. Dealing with a file-encrypting Trojan like the Black Kingdom Ransomware may end up costing you all your files. This is because the Black Kingdom Ransomware will compromise your PC to encrypt your files and demand a payment in exchange for a decryption tool. A significant number of cybercriminals will not provide you with a decryptor even if you pay them, so it is not advisable to contact conmen like the ones responsible for the Black Kingdom Ransomware at all.

Propagation and Encryption
Most file-locking Trojans are propagated via phishing emails, bogus software updates, and downloads, torrent trackers, malvertising, fake social media pages, etc. However, the Black Kingdom Ransomware does not rely on any of the distribution mentioned above techniques. The authors of the Black Kingdom Ransomware have opted to rely on a known vulnerability – CVE-2019-11510. This vulnerability regards the Pulse Secure VPN service. If you are using this service, it is strongly recommended to apply the latest update to the utility to avoid being vulnerable to the Black Kingdom Ransomware. Upon infecting a targeted system, the Black Kingdom Ransomware will scan the files present on it. The Black Kingdom Ransomware would gain persistence on the infected host by scheduling a task, which will ensure that the file-locker will be launched every time the system is rebooted. To avoid raising suspicion, the task associated with the Black Kingdom Ransomware appears to be a legitimate task, which would be run by the Google Chrome Web browser. The ransomware threat uses a pre-made PowerShell script to open a reverse shell on the infected system. Next, the Black Kingdom Ransomware will carry out an encryption process that will render most files present on the compromised host unusable. The files locked by the Black Kingdom Ransomware will have a '.black_kingdom' or '. DEMON' extension appended to their names. For example, a file called 'parsley-dish.mp3' will be renamed to 'parsley-dish.mp3.black_kingdom' or 'parsley-dish.mp3. DEMON.'
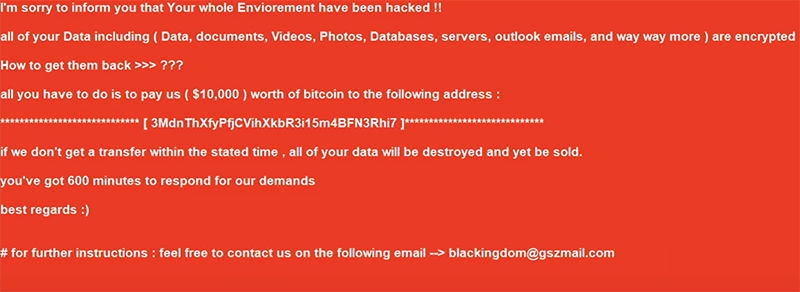
The Ransom Note
The conmen behind the Black Kingdom Ransomware demand to be paid $10,000 in Bitcoin. The attackers state that there is a deadline for contacting them – 600 minutes (10 hours). There is a countdown, which serves as a social engineering trick to pressure the users into paying the ransom fee demanded. There is an email address provided so that the victim can contact the attackers – ‘blackingdom@gszmail.com.'
The best approach in this tricky situation is to remove the Black Kingdom Ransomware from your PC with the help of a legitimate, up-to-date anti-virus software suite.

