Better_Call_Saul Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 124 |
| First Seen: | March 17, 2016 |
| Last Seen: | June 9, 2023 |
| OS(es) Affected: | Windows |
The 'Better_Call_Saul' Ransomware is a ransomware Trojan that encrypts the victim's files and then demands a ransom of $1000 AU to restore access to the encrypted files. A large number of the 'Better_Call_Saul' Ransomware infections have occurred in Australia. The unique aspect of the 'Better_Call_Saul' Ransomware that sets it up apart from the multiple other ransomware Trojans that are active today is that the 'Better_Call_Saul' Ransomware contains numerous references to the Breaking Bad television show and its spin-off, Better Call Saul. If your computer is infected by the 'Better_Call_Saul' Ransomware, PC security analysts recommend restoring the encrypted content from a back-up after wiping the infected hard drive. Unfortunately, it may not be possible to decrypt the files encrypted by the 'Better_Call_Saul' Ransomware without access to the decryption key.
The Peculiarities of the 'Better_Call_Saul' Ransomware
This attack's name references the Better Call Saul television show. The ransom note associated with the 'Better_Call_Saul' Ransomware contains the logo and content related to Los Pollos Hermanos, a fictitious chicken chain that features prominently in the Breaking Bad Universe. Other references to Breaking Bad include the language of the ransom demand, which mentions 'the one who knocks', a famous line by the Breaking Bad's protagonist. The 'Better_Call_Saul' Ransomware is not the first ransomware threat that references Breaking Bad; previous types of ransomware have been linked to this television show. The 'Better_Call_Saul' Ransomware is unique in that it correlates this attack to an encryption ransomware, rather than computer blockers or browser hijackers. The 'Better_Call_Saul' Ransomware may be delivered using a file named 'PENALTY.VBS,' included in corrupted email attachments frequently. In the case, of the 'Better_Call_Saul' Ransomware, these emails may include a PDF file that is also opened to distract computer users while the attack occurs in the background.
The 'Better_Call_Saul' Ransomware Demands a Substantial Ransom
The 'Better_Call_Saul' Ransomware displays a YouTube video with instructions on how to buy BitCoins, an anonymous online currency that may be used in these attacks. According to the 'Better_Call_Saul' Ransomware ransom note, computer users must pay $1000 AU with BitCoins to obtain access to the files encrypted by this threat. These attacks have increased in number in the last few years substantially, becoming fairly common today. The best way to prevent the 'Better_Call_Saul' Ransomware attacks is by avoiding clicking on unsolicited email attachments and learning to spot these threats in the wild.
How the 'Better_Call_Saul' Ransomware Works
The 'Better_Call_Saul' Ransomware depends on social engineering heavily. The file associated with the 'Better_Call_Saul' Ransomware is contained in a corrupted ZIP archive. When computer users open this email attachment, the 'Better_Call_Saul' Ransomware will start to search the victim's computer for files to encrypt. The 'Better_Call_Saul' Ransomware uses AES (Advanced Encryption Standard) to encrypt the victim's files. The AES key is encrypted itself using RSA. These layers of encryption make it nearly impossible for computer users to decrypt the affected files without obtaining the decryption key from the people responsible for the 'Better_Call_Saul' Ransomware.
The 'Better_Call_Saul' Ransomware looks for the following types of files on the victim's computer:
.ai
.crt, .csv
.db, .doc, .docm, .docx, .dotx
.gif
.jpeg, .jpg
.lnk
.mp3, .msi
.ods, .one, .ost
.p12, .pdf, .pem, .pps, .ppsx, .ppt, .pptx, .psd, .pst, .pub
.rar, .raw, .rtf
.tif, .txt
.vsdx
.wma
.xls, .xlsm, .xlsx, .xml
.zip
After finding files that match these extensions, the 'Better_Call_Saul' Ransomware encrypts them and displays a ransom note themed with the Breaking Bad content and a YouTube video with instructions for purchasing BitCoins. The 'Better_Call_Saul' Ransomware is associated with a YouTube video that includes music from a fictional radio channel from the Grand Theft Auto video game series, which is another link to Breaking Bad. Regardless of the playful elements present in the Better_Call_Saul' Ransomware attack, it presents a real threat to the computer users' files.
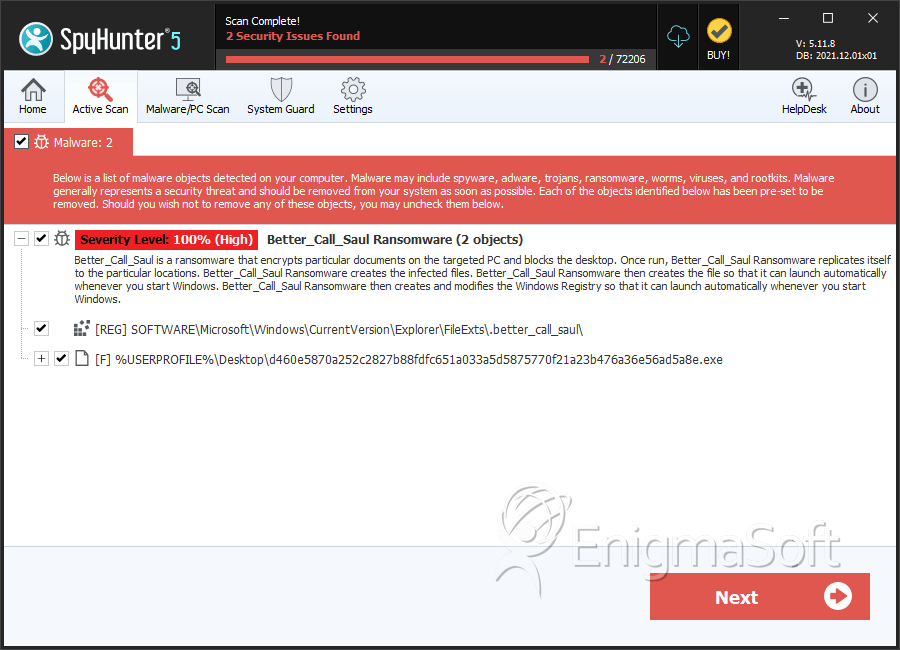
SpyHunter Detects & Remove Better_Call_Saul Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | d460e5870a252c2827b88fdfc651a033a5d5875770f21a23b476a36e56ad5a8e.exe | d1217c81cca33f5fcc4bed6cd948a36b | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.