Best Antivirus
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 45 |
| First Seen: | December 20, 2011 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
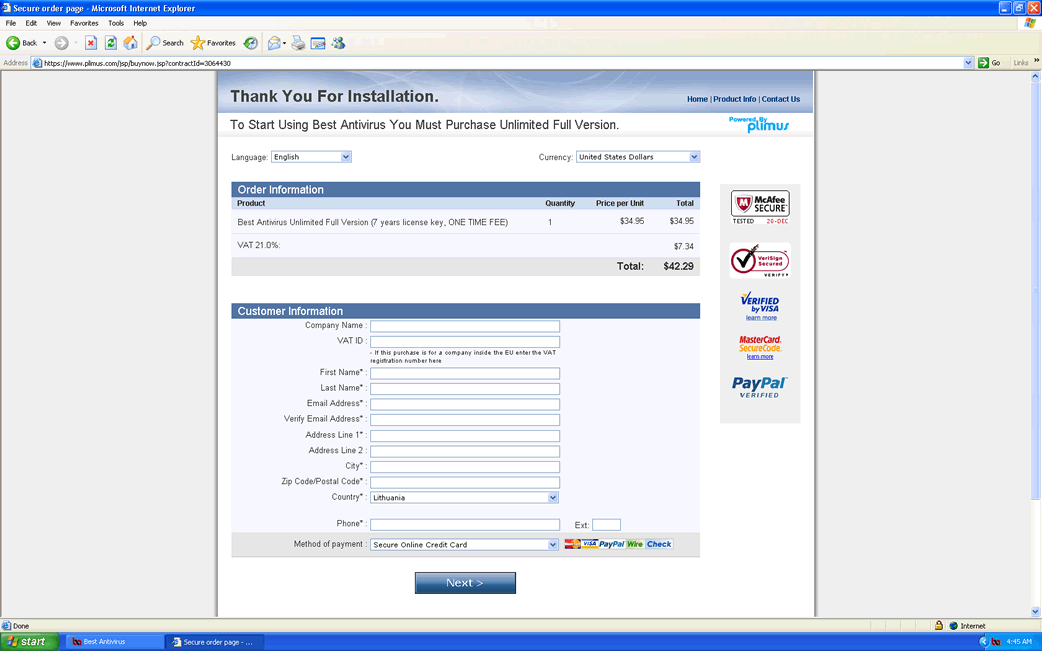
Best Antivirus Image
Despite its name, Best Antivirus is actually a kind of malware infection known as a rogue security application. Rogue security programs such as Best Antivirus are fake anti-virus programs that are designed to take a computer hostage and then convince inexperienced computer users to purchase a useless license or 'full version' of Best Antivirus. Best Antivirus, as a member of the VirusDoctor family, is designed to harm a computer's operating system and to interfere with the way it connects to the Internet or carries out its normal tasks. ESG security researchers strongly recommend against purchasing Best Antivirus. In fact, since Best Antivirus is actually a malware threat, it is important to remove Best Antivirus from your computer immediately by using a legitimate, fully-updated anti-malware application.
According to ESG malware analysts, most cases of infection related to Best Antivirus come from fake online anti-malware scanners. These will usually take the form of an attack website, pop-up window or a malicious advertisement claiming that your computer system may be infected with malware and offering a free scan of your hard drive. In fact, these fake online scanners are actually designed to deliver Best Antivirus into your computer. Other common sources for the Best Antivirus infection include files and embedded links contained in spam email. While most reliable anti-spam filters are able to catch most messages containing an infected attachment, some of these malicious emails may slip through your filter. Because of this, ESG security researchers strongly advise against opening any links or file attachments contained in unsolicited email (even if it appears to come from a legitimate source).
Table of Contents
Best Antivirus is Caused by a Trojan Infection
The above distribution methods are typical of a Trojan infection. Trojans, unlike viruses or worms, are malware infections that cannot spread on their own. They require a computer user to download and install them. Because of this, much like the Trojan from which they derive their name, Trojans will use deception in order to convince a computer user to download and install them. Best Antivirus’s methods are typical examples of ways in which Trojans spread. Best Antivirus will usually be associated with a malicious fake anti-virus Trojan, which may also rely on other Trojan infections in order to disrupt your computer system. Best Antivirus may also be protected with a rootkit, a kind of malware infection that is extremely difficult to remove.
There are various clones of Best Antivirus. These clones encompass
Aliases
3 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Suspicious file |
| DrWeb | Trojan.FakeAV.10542 |
| BitDefender | Trojan.Generic.KDV.438454 |
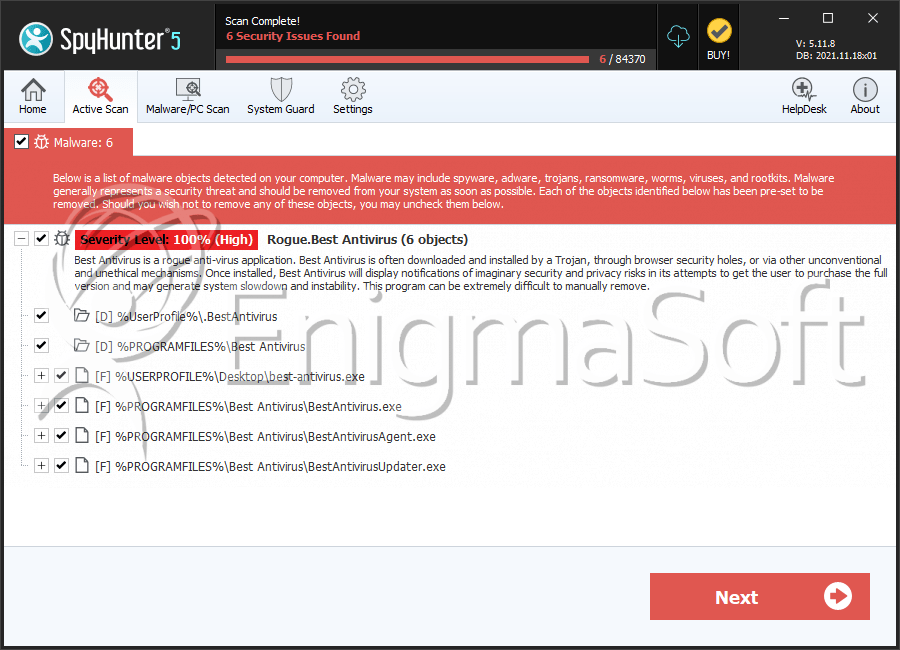
SpyHunter Detects & Remove Best Antivirus
Best Antivirus Video
Tip: Turn your sound ON and watch the video in Full Screen mode.
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | best-antivirus.exe | 17f95f9721f43da68ce9bcaf07be72f5 | 4 |
| 2. | BestAntivirusAgent.exe | e0a7b17104fe820a87ac33bab3048ae8 | 3 |
| 3. | BestAntivirusUpdater.exe | 66e8f9cd15febd7f531fe4d2e76d700d | 3 |
| 4. | BestAntivirus.exe | b688abe5d3ebb87ef093bf1b58c2e8ac | 2 |
| 5. | BestAntivirus.exe | 05dc12acbf680c739ca00f58c671779a | 2 |
| 6. | BestAntivirusUpdater.exe | 1ad53c415612ebce525e00b818126c7e | 2 |
| 7. | %PROGRAMFILES(x86)%\ Best Antivirus\ BestAntivirus.exe | ||
| 8. | %PROGRAMFILES(x86)%\ Best Antivirus\ BestAntivirusUpdater.exe | ||
| 9. | %PROGRAMFILES(x86)%\ Best Antivirus\ BestAntivirusAgent.exe |
Registry Details
Directories
Best Antivirus may create the following directory or directories:
| %PROGRAMFILES%\Best Antivirus |
| %UserProfile%\.BestAntivirus |

