Bert Ransomware
With cyber threats evolving rapidly, defending your devices against malware is more critical than ever. Among the most damaging threats is ransomware, a type of malware that locks users out of their data and demands payment for access. One such advanced strain making the rounds is Bert Ransomware, a threatening program designed to encrypt valuable files and extort victims. Understanding this threat and implementing proactive security measures is essential to safeguarding personal and organizational data.
Table of Contents
The Bert Ransomware: A Silent Saboteur
The Bert Ransomware operates with a clear and destructive objective: encrypting users' files and holding them hostage. Once it infiltrates a system, Bert modifies the filenames of affected documents by appending the extension '.encryptedbybert.' For instance, a file named report.pdf would become 'report.pdf.encryptedbybert.'
After encryption, the malware drops a ransom note titled '.note.txt.' This file informs victims that their network has been compromised and sensitive data exfiltrated. The attackers instruct victims to reach out through the Session messaging platform using a provided Session ID.
The ransom note often emphasizes that payment is the only route to file recovery. However, trusting these cybercriminals is a gamble—many victims never receive the promised decryption tools even after payment. Furthermore, paying only encourages continued criminal activity.
Infection Vectors: How the Bert Ransomware Spreads
The Bert Ransomware is distributed through a range of deceptive techniques designed to lure users into opening malicious files or links. These include:
- Fraudulent email attachments (e.g., Word documents, PDFs, or executables)
- Fake software updates or installers
- Pirated software and illegal key generators (keygens)
- Infected USB drives and compromised websites
- Peer-to-peer (P2P) networks and third-party downloaders
- Exploitation of software vulnerabilities
In many cases, the malware tricks users into enabling macros or bypassing security warnings, resulting in a successful system compromise.
The Real Cost: Data Loss and More
Once active, Bert not only locks important files but may also steal sensitive data, amplifying the threat. Beyond potential data loss, victims can face reputational damage, regulatory penalties and significant recovery costs. Worse still, infected systems can serve as launchpads to spread the ransomware across an entire network.
While recovery tools are rare and often unreliable without paying the ransom, users with clean backups stand a better chance of restoring data without giving in to criminal demands.
Fortify Your Defenses: Best Practices against Ransomware
Protecting your systems against Bert and similar threats requires a layered and proactive approach. Here are key cybersecurity best practices to reduce your exposure:
- System Hardening & Maintenance
- Keep security patches, your operating system and software updated.
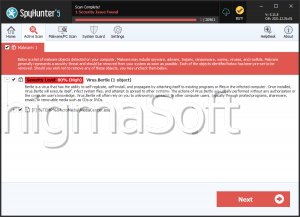
- Use a reputable anti-malware solution with real-time protection enabled.
- Disable unnecessary services and user privileges to minimize attack surfaces.
- Data Protection & Backup Strategy
- Implement a regular backup routine for critical files.
- Store backups offline or in cloud environments with version control.
- Periodically inspect your backups to ensure they can be restored successfully.
- Safe Browsing & Email Habits
- Avoid clicking unchecked links or downloading attachments from unsolicited emails.
- Be wary of pop-ups or fake support pages urging software downloads.
- Never enable macros in documents unless you're sure of the source.
- Employee Awareness & Training
- Educate users on how to realize phishing attempts and social engineering tactics.
- Simulate real-world attack scenarios to assess and improve response readiness.
Don’t Wait for Disaster: Stay Prepared
Ransomware like Bert is a serious and growing threat, capable of crippling individuals and organizations alike. By understanding how it operates and applying robust security practices, users can drastically reduce the risk of infection and its devastating consequences. Prevention, vigilance, and preparedness are your best allies in the fight against ransomware.