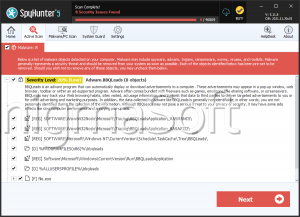
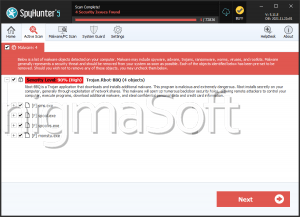
Bbq Ransomware
The threat of ransomware has become one of the most severe cybersecurity challenges. These hazardous programs are designed to encrypt critical files and demand payments in exchange for decryption tools. Among the growing list of such threats, Bbq Ransomware—a variant of the notorious Makop family—has surfaced as a harmful adversary. Protecting your systems and data from such sophisticated threats is no longer optional; it's essential.
Table of Contents
Inside the Bbq Ransomware Infection
The Bbq Ransomware follows a common but effective ransomware blueprint: infiltrate the system, encrypt the victim's files, and demand a ransom for restoration. It renames encrypted files with a distinct pattern that includes a victim-specific ID, the attackers' email address, and the '.bbq46' extension. For example, a file like 1.pdf becomes:
1.pdf.[2AF20FA3].[dashboard487@onionmail.org].bbq46
To ensure that victims are aware of the attack and the next steps, the malware alters the system's desktop wallpaper and places a ransom note titled '+README-WARNING+.txt.' This message explains that file recovery requires purchasing decryption tools from attackers and offers a small token of "trust" by allowing the decryption of two files under specific limitations.
The note also warns victims against using anti-malware tools or third-party recovery solutions, claiming these might corrupt the encrypted data permanently. However, these claims are manipulative scare tactics designed to discourage intervention and drive victims toward payment.
The Risks of Paying a Ransom: No Guarantees
As is familiar with ransomware operations, the Bbq Ransomware's decryption promises come with no guarantee. Even victims who comply with payment demands frequently do not receive the promised tools. Paying the ransom not only fails to assure file recovery, but it also finances future criminal operations.
The encrypted data remains locked unless a reliable and uninfected backup is available. Therefore, ransomware removal is critical to halt further encryption, but it won't restore already compromised files.
How the Bbq Ransomware Spreads
Like most modern ransomware, Bbq relies on deception and user interaction for distribution. The infection chain often begins with social engineering tactics, where malware masquerades as legitimate files or software updates. Once executed, these files initiate the encryption process.
Standard delivery methods include:
- Phishing emails with fraudulent links or attachments.
- Malvertising (bogus advertisements) and deceptive online pop-ups.
- Drive-by downloads, where malware is downloaded in the background when visiting compromised websites.
- Bundled downloads via cracked software, illegal media or fake updates.
- Backdoor Trojans that open the system to additional threats.
- Removable devices, which allow the malware to propagate to other systems.
Fortify Your Defenses: Essential Security Best Practices
Proactively defending your devices from threats like the Bbq Ransomware requires a layered and disciplined approach to cybersecurity.
- Strengthen System and User-Level Defenses
- Keep all software updated, including the operating system, browsers and security tools.
- Use a trusted anti-malware solution with real-time protection enabled.
- Disable macros in Office files and restrict script execution from untrusted sources.
- Configure a firewall to monitor all incoming and outgoing traffic.
- Create limited user accounts for daily use instead of operating with administrator privileges.
- Practice Safe and Smart Online Behavior
- Avoid accessing files or links from unverified or unsolicited sources.
- Do not trust email attachments or links from unknown senders—always verify authenticity.
- Steer clear of pirated software, 'free' downloads from sketchy sites, and software cracks.
- Be wary of pop-up alerts urging immediate updates or anti-malware installs.
- Train users and employees to acknowledge phishing attempts and report suspicious activity.
Backup: Your Digital Lifeline
Ultimately, the most reliable safeguard against ransomware damage is a robust backup strategy:
- Maintain frequent backups of essential data on offline or air-gapped devices.
- Use cloud backups with versioning enabled to roll back to pre-infection copies.
- Regularly check your backups to be sure they are restorable and complete.
The Bbq Ransomware exemplifies the ongoing evolution and threat posed by cybercriminals using encryption-based extortion. While the malware is destructive, victims should avoid falling into the trap of ransom payments. Instead, focus on removing the infection, restoring clean backups, and implementing preventive strategies that drastically reduce the chances of reinfection. In cybersecurity, preparation isn't just wise—it's survival.