BAFAIAI Ransomware
Protecting personal and business systems from malicious software is essential, as modern threats continue to evolve in complexity and reach. When a ransomware strain infiltrates a device, the consequences are often immediate and severe, data loss, operational disruption, and potential exposure of sensitive information. BAFAIAI Ransomware is one such advanced threat that highlights why strong defensive measures are no longer optional but necessary.
Table of Contents
A New Addition to a Dangerous Ransomware Lineage
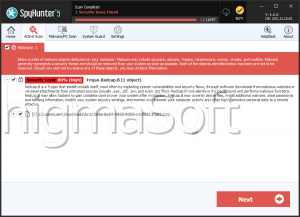
Security analysts detected BAFAIAI Ransomware during ongoing investigations into emerging malware activity. This threat belongs to the MedusaLocker family, a group known for aggressive tactics and high-impact attacks. Once BAFAIAI activates on a compromised system, it begins encrypting stored data and modifying filenames by attaching the '. BAFAIAI' extension. A file formerly named '1.png,' for instance, becomes '1.png.BAFAIAI,' making it immediately clear that the data is no longer accessible.
After the encryption phase, the malware generates a ransom message titled 'read_this_to_decrypt_files.html,' signaling that the system has been breached and that confidential information has been extracted.
Extortion Through Encryption and Data Theft
The attackers behind BAFAIAI claim to have infiltrated the victim's network, encrypted critical files, and exfiltrated private data. They warn that tampering with the encrypted files will make them permanently unusable. Victims are instructed to pay a ransom in exchange for decryption tools and the supposed promise that stolen information will not be leaked or sold.
The ransom note outlines several coercive elements:
- The price increases if the victim fails to make contact within 72 hours.
- The attackers offer to decrypt up to three non-sensitive files as 'proof' of their capabilities.
- Victims are pressured with the threat of public data exposure.
While these tactics aim to push organizations into quick compliance, payment rarely leads to a reliable recovery. Cybercriminals frequently ignore victims after receiving money, and paying ultimately finances further criminal operations.
Recovery Limitations and the Reality of Ransomware Damage
Once BAFAIAI encrypts files, regaining access without assistance from the attackers is nearly impossible unless the ransomware itself contains significant flaws, an uncommon scenario. Removing the infection will halt further damage, but it does not reverse the encryption already applied.
The most dependable recovery method is restoring affected data from clean, offline, or otherwise isolated backups. These backups should be maintained across multiple storage points to reduce the risk of simultaneous compromise.
How BAFAIAI Reaches Its Victims
This ransomware leverages the same distribution ecosystem that supports many high-profile malware operations. Threat actors rely on deceptive tactics to trick users into downloading or opening malicious content. Common delivery routes include:
- Trojan downloaders, compromised installers, and harmful email attachments.
- Unreliable or illegal download sources, pirated software, fake updates, malvertising, and files shared through peer-to-peer platforms.
Beyond these methods, some malware strains possess the capability to move laterally across networks or spread via removable devices, increasing the scope of an outbreak if not contained quickly.
Strengthening Security to Resist Malware Attacks
Reducing exposure to ransomware requires a comprehensive set of best practices. While no single technique guarantees immunity, a layered defense dramatically lowers risk and limits the impact of an attack.
Key defensive measures include:
- Maintain reliable backups stored in multiple, isolated locations, such as offline drives and secure remote servers.
- Keep operating systems, drivers, and software up to date to eliminate exploitable vulnerabilities.
- Deploy trusted antivirus and endpoint protection solutions capable of detecting suspicious behavior rather than just known signatures.
- Treat unsolicited emails, messages, links, and attachments with suspicion, especially when they come from unknown or unexpected sources.
- Avoid downloading software or media from unofficial platforms, and stay clear of pirated material and cracked activation tools.
- Limit administrative privileges to essential personnel and enforce strong password policies across the organization.
- Monitor network traffic, restrict macro execution where possible, and segment networks to contain potential outbreaks.
Final Thoughts
BAFAIAI Ransomware exemplifies the financial and operational risks posed by modern cyberthreats. While the damage inflicted by these attacks can be extensive, strong security habits, reliable backups, and cautious digital behavior significantly reduce the likelihood of becoming a victim. Proactive defense remains the most effective strategy against ransomware and other evolving forms of malware.