Backdoor.Bot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
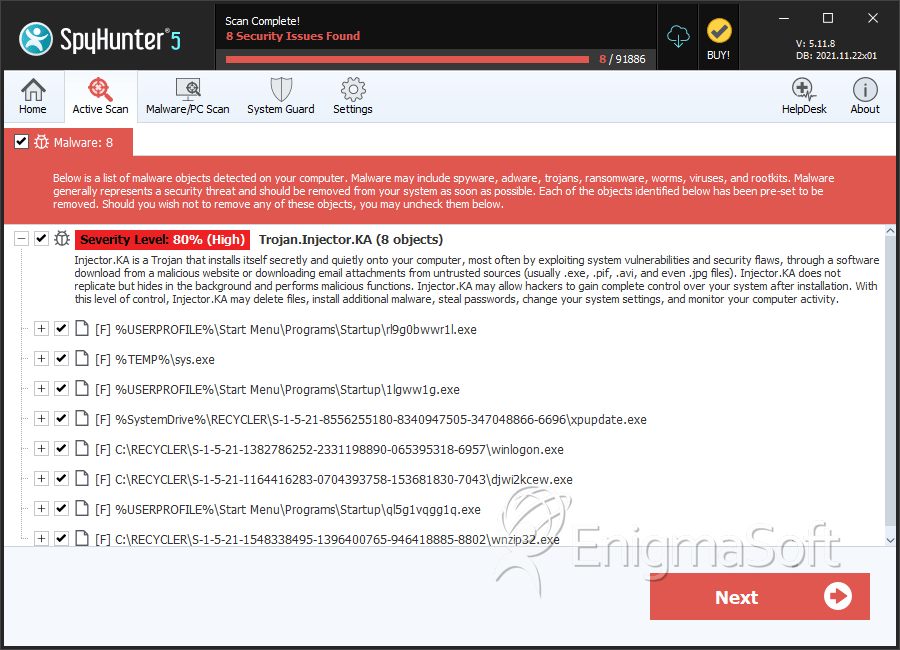
| Threat Level: | 80 % (High) |
| Infected Computers: | 378 |
| First Seen: | November 30, 2010 |
| Last Seen: | April 2, 2022 |
| OS(es) Affected: | Windows |
Like its name suggests, Backdoor.Bot is a backdoor Trojan. Like most backdoor Trojans, Backdoor.Bot is designed to allow a hacker to obtain illegal access to a computer through a digital 'backdoor'. Much like a real-life backdoor allows a robber to enter a house or a building without being seen, a backdoor into a computer like the one the Backdoor.Bot establishes allows a criminal to gain access to the infected computer without being detected by the infected computer's security. Once installed, the Backdoor.Bot will open up an unauthorized opening that allows criminals to carry out tasks by gaining access to the infected computer from a remote location. If you are afraid that your PC has been in contact with Backdoor.Bot, you should scan your computer with a reliable anti-malware tool after restarting Windows in Safe Mode.
While a backdoor can be used to do anything on the infected computer (for example, stealing information, installing other malware, or deleting the contents of the infected computer's hard drive), the Backdoor.Bot itself is usually associated with scams that involve identity theft or stealing login data for online gaming and banking accounts. The Backdoor.Bot can also be used to execute a keylogger component on the infected computer. This keylogger records all the keys that are pressed on the infected computer's keyboard, meaning that criminals can then use this data to steal your online passwords and sensitive data, such as credit card or bank account numbers. A keylogger can also be used to monitor your activity on the infected computer and spy on your personal communications. Every once in a while, the Backdoor.Bot will deliver all the gathered data to a remote server where criminals can then gain access to it and use it for their own, malicious purposes.
Table of Contents
What Kind of Tasks Can the Backdoor.Bot Be Used For?
Apart from stealing your information, Backdoor.Bot can be used as part of other large scale attacks on your computer. Criminals can use the Backdoor.Bot to install other malware on your computer, typically a rogue security program or a Trojan. There are numerous variants of the Backdoor.Bot due to the fact that the established backdoor can be used by criminals for a number of scams and attacks. Basically, the Backdoor.Bot allows criminals nearly the same level of control as if they were sitting in front of your computer's screen.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Generic16.CDTS |
| Ikarus | Trojan.Win32.Midgare |
| Sunbelt | Packed.Win32.Rebhip.a.1 (v) |
| AhnLab-V3 | Win-Trojan/Buzus.608256.D |
| eTrust-Vet | Win32/Kollah.APV |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Suspicious.H |
| DrWeb | Win32.HLLW.Autoruner.9222 |
| F-Secure | Trojan-Dropper:W32/Malis.gen!H |
| BitDefender | Trojan.Generic.2093113 |
| Kaspersky | Trojan.Win32.Buzus.bwqx |
| ClamAV | Trojan.Buzus-4637 |
| Avast | Win32:Inject-TO |
| F-Prot | W32/Trojan2.HEBD |
| NOD32 | Win32/Buzus.BIGA |
| McAfee | W32/Autorun.worm.fy |
SpyHunter Detects & Remove Backdoor.Bot
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | djwi2kcew.exe | 2ca3ca594904b5e5dfbf9bb14aea3a34 | 12 |
| 2. | rl9g0bwwr1l.exe | 26615614660d568b2509a5373cbcad1c | 9 |
| 3. | sys.exe | 6f743f8489ef000c14191c9e547bddca | 9 |
| 4. | djwi2kcew.exe | bd9d96b45feace6db343f380acbd0517 | 8 |
| 5. | djwi2kcew.exe | b086470de5018b01c17b448ebce211e8 | 7 |
| 6. | djwi2kcew.exe | a54087344c695db09afec6100a2332cc | 6 |
| 7. | 1lgww1g.exe | d6299d87ce2518668955468aa91667e3 | 6 |
| 8. | xpupdate.exe | 2d9b147c2059dce494223b818274d748 | 6 |
| 9. | djwi2kcew.exe | 160c20bd5a310b92f0a2105fe9b37ace | 4 |
| 10. | ql5g1vqgg1q.exe | e5aa1ca75d8ce62b7f0ee097346f3cec | 4 |
| 11. | winrom.exe | 742f9d3621a981a7bd6fc0cc8d225925 | 2 |
| 12. | rundll32.exe | aa36c242d9a59c54c8ad96d48702c1bc | 2 |
| 13. | ffaavqq2kf.exe | 26d217ef3002f934d9f1c4787f2692f2 | 2 |
| 14. | qql1faavlaq.exe | 6127348f0451305c0d520129f242ae1c | 2 |
| 15. | scxhost.exe | 0eca47f9d5b93ca3498526b5580abdbd | 2 |
| 16. | zvlw1mns.exe | 87c7e824dd386017f1b7651a50c3ccce | 2 |
| 17. | awwriiduup.exe | 1db63bbbddce7131378767ee8f3eb60e | 2 |
| 18. | 0hm86y8.exe | 8bc5757abfcffdf65fe041e8ae000642 | 2 |
| 19. | 5iidjfv.exe | 94afc9b7ec1a7c00a781e0f5df822c22 | 2 |
| 20. | 5wwmns8.exe | a4ec4df6ca473fa9dae91aed5c4b2592 | 2 |
| 21. | r.exe | 53d4ee6fb944fa56733d1b099ca2dbd1 | 2 |
| 22. | winrsc.exe | 729182a9cf01c56cf51cd8caed6f88b6 | 1 |
| 23. | msimfo32.exe | c67241d3ac991ece12a1c6e091284b82 | 1 |
| 24. | 2too6aa.exe | 38c94d3fc0147691b03ae361b8c899e3 | 1 |
| 25. | rnnjzzv2rmm.exe | ca96f280ab521b593b0c45676e08e4eb | 1 |
| 26. | uqqlccxooj.exe | 98784700ee33189554b397cd5ee89e2a | 1 |