AutoEncryptor Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
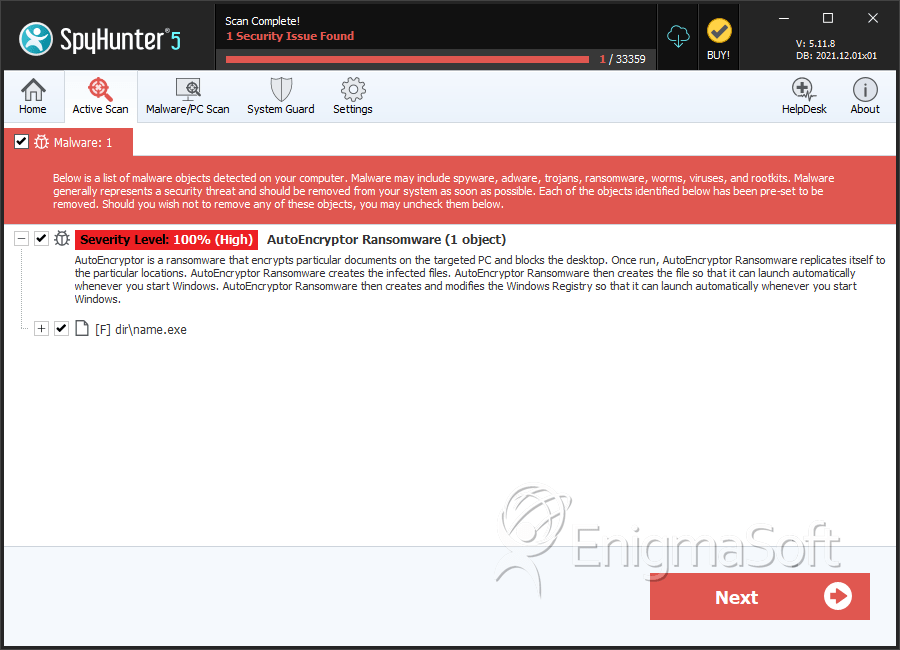
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6 |
| First Seen: | April 17, 2017 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
The people behind a ransomware program called AutoEncryptor Ransomware, are asking for a ransom of 10 000BTC, which equals around 11 769 800 USD! The AutoEncryptor Ransomware is a threat infection that targets English-speaking users mainly, but was also detected in computers belonging to the Czech Republic and Slovakia users. The AutoEncryptor Ransomware may spread to vulnerable computers by spam email campaigns or by using exploit kits. The perpetrators of the AutoEncrypt Ransomware are using a double encryption to prevent a free decryption option. Once inside a computer, the AutoEncryptor Ransomware will generate a unique AES-256 encryption key for each victim.
As soon as the files are enciphered, the AutoEncryptor Ransomware will use another key generated in the process and encrypt it with the RSA-2048 encryptor. The AutoEncryptor Ransomware uses a table called FileLocker to display its ransom note. However, even if someone takes the risk of agreeing with the absurd demands of the AutoEncryptor Ransomware, the paid ransom will not help victims to restore access to the computer because the AutoEncryptor Ransomware is designed by cyber crooks to rip PC users off. The targeted computer will be blocked completely so that the PC user can't even reboot it.
Do not trust any information delivered by the AutoEncryptor Ransomware and do not pay the so-called ransom because you will face huge financial losses. Use a reputable anti-malware application to uninstall the AutoEncryptor Ransomware from the corrupted PC and then restore the affected files from the Shadow Volume Copies from Windows or any backup resource you have.
SpyHunter Detects & Remove AutoEncryptor Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | name.exe | 05950b038b5781d940c939a3af3ecd32 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.