Atrax
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
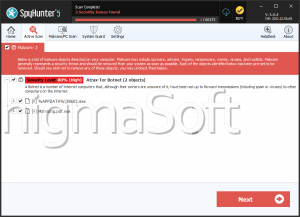
| Ranking: | 2,492 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 7,999 |
| First Seen: | December 10, 2013 |
| Last Seen: | September 20, 2023 |
| OS(es) Affected: | Windows |
Atrax is a malware kit that is capable of carrying out numerous damaging tasks, including mining Bitcoins, launching DDoS attacks and stealing targets' private information. Security researchers have received alarming reports of a malware kit that is being distributed on underground forums with user friendly capabilities and a low price for its main platform. When most widely used malware kits average prices between five hundred and a thousand dollars for the main module, the fact that Atrax costs about $250 is particularly alarming because it gives to more potentially criminals access to a powerful threat tool. The presence of Atrax on the market makes it likely that threat attacks involving these types of advanced malware kits may increase in the future.
Table of Contents
Atrax Features and Possible Attack Methods
Atrax' attacks are particularly difficult to intercept because Atrax uses TOR protocol when communicating with its Command and Control server. This type of anonymous communication is among the most secure forms of encryption and makes it nearly impossible for malware researchers to intercept the communications between Atrax and its command and control server using normal methods. Atrax may be used to launch DDoS attacks, mine crypto-currency such as Bitcoins or Litecoins and steal data from the affected computer's forms and Web browsers, potentially allowing criminals to gain access to the victims' passwords and other personal information.
The Peculiarities of Atrax
Atrax' main component is much larger than average, usually above 1MB. However, this is due to the integration with Windows and TOR communication. The larger size does not seem to be much of an issue, though, because it seems that Atrax is usually distributed using a dropper or loader that is typically about 2KB in size. Atrax has most of the features of typical malware kits, allowing criminals to steal data and install other threats on the affected computer. Atrax uses a modular design that allows criminals to customize their Atrax version by adding the appropriate modules, which are purchased separately. For example, adding DdoS capabilities to Atrax costs around $90 above the initial asking price of this threat.
URLs
Atrax may call the following URLs:
| captcha-sourcecenter.com |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.