ASN1 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6 |
| First Seen: | December 2, 2016 |
| Last Seen: | December 16, 2018 |
| OS(es) Affected: | Windows |
The ASN1 Ransomware is a threat that has been linked to several attacks in December 2016. The ASN1 Ransomware has the capability to spread within a network, making it a particular threat to corporate computers and networks. Employees within one company may become infected by a threat like the ASN1 Ransomware after opening an email sent by one of their colleagues. There is little to distinguish the ASN1 Ransomware from numerous, other similar ransomware threats that are currently active. The ASN1 Ransomware may be distributed using corrupted spam email messages that will include an embedded link or file attachment that downloads the ASN1 Ransomware from a dummy website. The ASN1 Ransomware is being used in targeted attacks designed to compromise computers belonging to small businesses as well as Web servers deliberately.
Table of Contents
The ASN1 Ransomware Uses a Different Encryption Method
The ASN1 Ransomware is particularly unique in that it uses CMS, or Cryptographic Message Syntax, in its encryption attack. The ASN1 Ransomware provides a private key in the form of an ASN.1 key, which also identifies the victim of the attack. The ASN1 Ransomware receives its name because of its use of this key precisely. Not many encryption ransomware Trojans use this encryption method, making the ASN1 Ransomware fairly unique in a field that is saturated with ransomware Trojans that use identical encryption methods during their attack currently. The technique used by the ASN1 Ransomware is similar to the techniques used by software developers to protect their proprietary codes.
The ASN1 Ransomware attack is typical of these attacks: the ASN1 Ransomware scans the victim's drives and creates a list of the victim's files that will be encrypted. The ASN1 Ransomware, making it different from many ransomware Trojans that are currently active, will not change the targeted files’ extensions. Once the ASN1 Ransomware has encrypted the victim's files, these files will no longer be accessible to the computer user.
Recovering from an ASN1 Ransomware Attack
The people responsible for the ASN1 Ransomware demand a ransom payment of 0.25 Bitcoin, which is currently approximate $200 USD at the actual exchange rate. PC security analysts strongly advise computer users to refrain from paying the ASN1 Ransomware ransom. There is no guarantee that the con artists will keep their word and deliver the means for decryption after the victim has paid the ransom. In fact, it is equally likely that the con artists will simply ignore the victim or turn around and demand even more money.
Malware researchers recommend that computer users instead remove the ASN1 Ransomware completely with the help of a reliable security program that is fully up to date. A reliable anti-malware application also can help intercept the ASN1 Ransomware before it begins carrying out its attack. Since the most common way in which the ASN1 Ransomware is distributed is through the use of corrupted spam email messages, malware analysts strongly advise that computer users take extra care when handling email messages or visiting suspicious websites. It is especially important to avoid opening unsolicited email attachments or embedded links, even if they appear to come from a trusted source (which may have been compromised to spread the ASN1 Ransomware infection). Taking proper precautions online is the best way to prevent the ASN1 Ransomware attacks, as well as other forms of threats.
Having backups of all files is the best way to become invulnerable to the ASN1 Ransomware and other encryption ransomware Trojans completely. If the computer user can recover the compromised files from a backup, then the con artists can no longer threaten the victim by encrypting the files. Because of this, PC security researchers strongly advise computer users to backup their files regularly and ensure that these backups are properly secured. A combination of strong security practices and good browsing practices should be enough to prevent the ASN1 Ransomware infections.
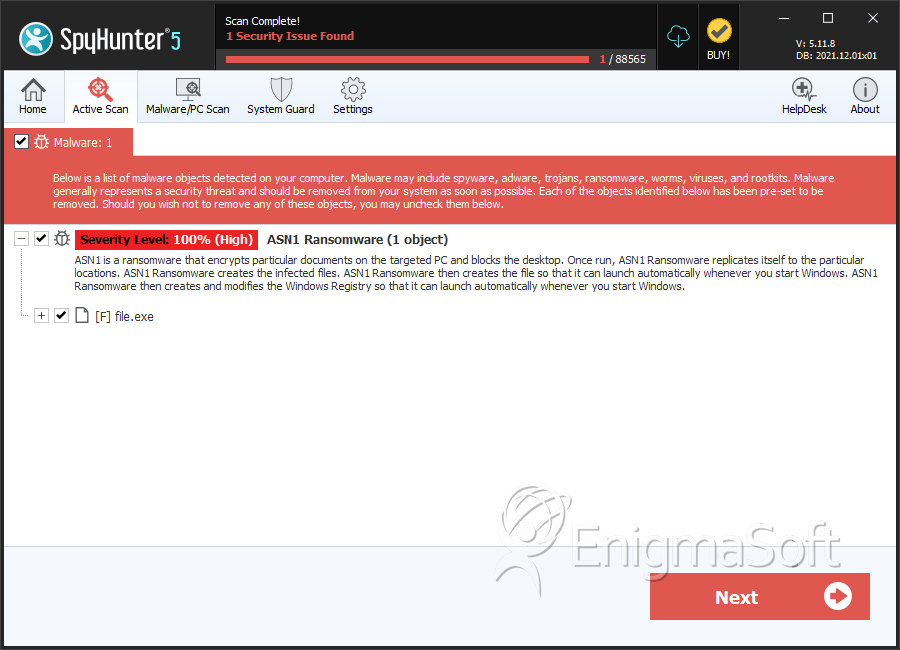
SpyHunter Detects & Remove ASN1 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 5682be2d6efed420f6e15424e5ca0d98 | 1 |
| 2. | file.exe | cec1bce79b0503ce76f97618d55b5fa2 | 0 |
| 3. | file.exe | 737a1d20c85fd62cde1ad14d3bc69102 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.