AnonWorld Ransomware
The importance of protecting digital devices from advanced threats cannot be overstated. As technology advances, so do the schemes of cybercriminals. The AnonWorld Ransomware is a prime example of how malevolent actors exploit vulnerabilities to disrupt lives and businesses. This sophisticated threat underscores the critical need for robust security practices and vigilance.
Table of Contents
Understanding the AnonWorld Ransomware: A Geopolitical Weapon
The AnonWorld Ransomware is a highly targeted threat designed to encrypt a victim's files and demand payment for decryption. Once deployed on a device, it systematically encrypts data, appending the file names with the extension '.SNEED.' For instance, files like '1.png' are transformed into '1.png.SNEED,' effectively rendering them inaccessible.
After completing its encryption process, AnonWorld alters the victim's desktop wallpaper and leaves a ransom note in a file named 'R3ADM3.txt.' This note reveals the ransomware's geopolitical motivation, targeting companies in Russia or Belarus. Victims are given a three-day window to contact the attackers, failing which stolen data may be leaked online. Despite these demands, paying the ransom is a risky choice, as there is no guarantee that the promised decryption tools will be provided.
How Ransomware Spreads: The Tactics behind the Threat
AnonWorld, like most ransomware, relies on a variety of deceptive methods to infiltrate systems. These include:
- Phishing Emails: Disguised as legitimate communications, these emails deliver fraudulent attachments or links that, when opened, trigger the ransomware's installation.
- Trojans and Backdoors: Malware loaders often pave the way for ransomware to execute its malicious tasks undetected.
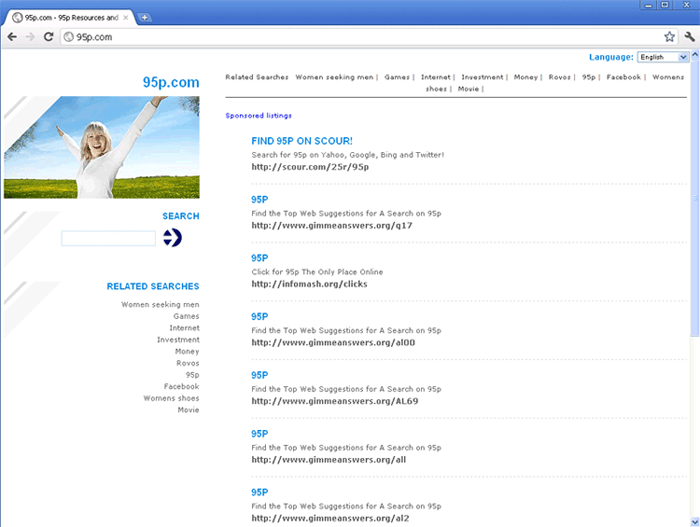
- Compromised Downloads: Threats may be bundled with software obtained from untrustworthy sources such as peer-to-peer networks or free file-hosting platforms.
- Exploiting Software Vulnerabilities: Fake software updates and illegal activation tools ('cracks') are common vectors for malware delivery.
- Self-Proliferation: Some ransomware strains can spread autonomously through local networks and removable devices, amplifying their reach.
Merely opening an infected file, regardless of its format—be it an executable, archive, or document—can initiate an attack.
Defending against AnonWorld and Similar Threats
Proactive measures are essential to protect systems from ransomware and other harmful programs. Here are some best practices to strengthen your defenses:
- Implement Robust Backups: Regularly back up critical files and store them in secure, offline locations. This ensures that even if ransomware encrypts your data, you have accessible copies.
- Upgrade Programs Regularly: Keep your operating system and all installed applications updated. Software patches often close vulnerabilities that ransomware exploits.
- Exercise Caution with Emails and Downloads: Avoid interacting with links or attachments from unknown or unverified sources. Be particularly wary of unexpected emails that create a sense of urgency.
- Use Reliable Security Software: Install reputable anti-ransomware tools to uncover and block threats before they can be executed.
- Restrict Administrative Privileges: Limit user accounts with administrative access to reduce the potential impact of an attack. Use the Multi-Factor Authentication for an added layer of security.
- Educate and Train: Promote awareness of phishing and other social engineering tactics among employees and household members. A well-informed user base is a strong first line of defense.
- Monitor and Segment Networks: Regularly monitor network activity for unusual behavior and segment networks to contain potential breaches.
Removing the AnonWorld Ransomware: A Post-Infection Strategy
If the AnonWorld Ransomware infiltrates your system, immediate action is critical. While removing the ransomware halts further encryption, it does not restore already locked files. This makes preventative measures and robust backups indispensable.
Specialized tools and professional assistance may help eliminate ransomware, but relying on attackers' decryption tools is ill-advised due to their unreliability. In rare cases where the ransomware is poorly designed, free decryption methods may exist, but such occurrences are exceptions rather than the rule.
The Path Forward: Vigilance is Key
The AnonWorld Ransomware exemplifies the evolving complexity of digital threats. Staying informed, practicing caution, and implementing robust security measures are vital in safeguarding personal and organizational data. Users can fortify their defenses against ransomware and mitigate its potentially devastating consequences by taking proactive steps.