Annabelle Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 8 |
| First Seen: | February 23, 2018 |
| Last Seen: | June 19, 2022 |
| OS(es) Affected: | Windows |
PC security researchers are receiving reports of infections involving the Annabelle Ransomware, a ransomware Trojan first observed in February 2018. The Annabelle Ransomware is being delivered to victims through the use of damaged email attachments, as well as other, typical ways of delivering threats (such as hacking into the victim's computer directly, or through unsafe advertising). The Annabelle Ransomware carries out a typical ransomware attack, encrypting the victim's files to take them hostage, and then demanding a ransom payment from the victim in exchange for the decryption utility.
Table of Contents
How the Annabelle Ransomware Carries out Its Attack
Once the Annabelle Ransomware is installed on the victim's computer, the Annabelle Ransomware will use a strong encryption algorithm to make the victim's files inaccessible. The Annabelle Ransomware encrypts a variety of user-generated files, which include text files, images, videos and audio files. When the Annabelle Ransomware enciphers a file, it becomes inaccessible to anyone without the decryption key or program. The people handling the Annabelle Ransomware attack will hold the victim's files hostage until the victim agrees to pay a ransom. This is a way in which most encryption ransomware Trojans work, and there is little to differentiate the Annabelle Ransomware from the countless other versions of this tactic that are being used to take advantage of inexperienced computer users currently.
The Annabelle Ransomware and Its Ransom Demand
Once the Annabelle Ransomware has encrypted the victim's files, the Annabelle Ransomware will deliver a ransom message. The Annabelle Ransomware ransom note alerts the victim of the attack and contains links to websites on the Dark Web where the victim would pay the ransom. The Annabelle Ransomware's ransom note contains the following ransom demand, which threatens the victim with the permanent loss of the affected files if the ransom amount is not paid. The full text of the Annabelle Ransomware's ransom note reads:
'Your Personal ID: HIuMVtQbk
Frequently Asked Questions
What happened to my files?
All your files are encrypted and secured with a strong key. There is no way to get them back without your personal key.
How can I get my personal key?
Well you need to pay for it. You need to visit one of the special site below & then you need to enter your personal ID (you find it on the top) & buy it. Actually it costs exactly 0.1 Bitcoins.
Darknet Site: xxxx://annabelle85x9tbxiyki.onion/tbxlyki
Darknet Site: xxxx://annabelle59j3mbtyyki.onion/mbtyyki
How can I get access to the site?
You easily need to download the Torbrowser, you can get it from this site:
xxxxs://www.torproiect.org/
What is goin to happen if I'm not going to pay?
If you are not going to pay, then the countdown will easily ran out and then your system will be broken. If you are going to restart, then the countdown will ran out a much faster. So, its not a good idea to do it.
I got the key, what should I do now?
Now you need to enter your personal key in the textbox below. Then you will get access to the decryption program.
- The darknet sites are not existing, its just an example text. The other things are right, except the darknet thing. Its possible to get the key, but if I going to do a new trojan, or new version of this then I will add real ways to get the key 🙂 If you wanna that I going to do a 2.0 or a new trojan, then write it below in the comments. Thanks
If you wanna chat with me, contact me easily in discord: iCoreX#1337'
The Annabelle Ransomware also will display a short message about its infection, which reads:
'Warning! Do you got .NET Framework'4.5' (not 4.0)? If you are not running it with .NET Framework'4.5' then the TROJAN wont work! If you got .NET Framework '4.5' then press on 'yes' if not then on 'no'!'
Affected users shouldn't even consider paying the Annabelle Ransomware ransom and, instead, remove this threat with the help of a good security program that is fully up-to-date. Affected users can restore the files compromised by the Annabelle Ransomware attack from backup copies.
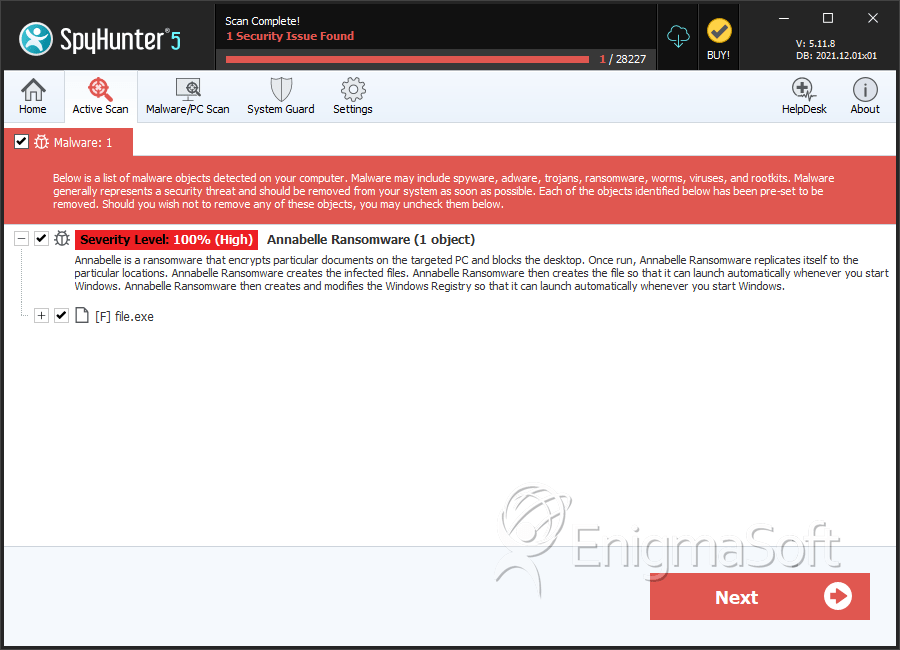
SpyHunter Detects & Remove Annabelle Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | ee041688d36494fdddf710a3ddb873bd | 0 |

