Allcry Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | October 2, 2017 |
| Last Seen: | January 9, 2019 |
| OS(es) Affected: | Windows |
The Allcry Ransomware is an encryption ransomware Trojan that was first observed carrying out attacks in the wild on October 2nd, 2017. The Allcry Ransomware is delivered to victims through spam email messages. These email messages will often contain a Microsoft Word document attachment. The Allcry Ransomware will be downloaded and installed by these documents, which uses macro scripts to accomplish this task when the document is downloaded. The Allcry Ransomware's primary targets are located in Eastern Asia, targeting countries such as China, Hong Kong, and Japan. As with most encryption ransomware Trojans, taking preemptive measures will ensure that your data is safe from the Allcry Ransomware attack, or from the many other encryption ransomware Trojans that are active in the wild today.
Table of Contents
How the Allcry Ransomware can Infect a Computer
The Allcry Ransomware will infect computers running the Windows operating system. Like most encryption ransomware Trojans, the purpose of the Allcry Ransomware is to encrypt the victim's files using a strong encryption algorithm. The Allcry Ransomware uses the AES encryption to make the victim's files inaccessible, and identifies the affected files with the file extension '.allcry,' which is added to each affected file's name. The Allcry Ransomware will target the user-generated files, while avoiding files that are necessary for Windows to function properly. The following are some examples of the files the Allcry Ransomware attacks during its infection process:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Allcry Ransomware’s Ransom Note
The Allcry Ransomware displays its ransom note in a text file named 'readme.txt' that is dropped on the victim's desktop. The Allcry Ransomware also may display a program window with a ransom message. The Allcry Ransomware ransom note is written in three languages: Korean, Chinese and English. The program window associated with the Allcry Ransomware is named 'Allcry crypter' and contains the following ransom message:
'Some files have been encrypted
Please send 0.2 bitcoins to my wallet address
If you paid, send the machine code to my email
I will give you program to decryper
If there is no payment within seven days,
we will no longer support decryption
Email: allcry@mail.com
Btc wallet: [RANDOM CHARACTERS]'
The Allcry Ransomware's ransom of 0.2 Bitcoin is equivalent to 900 USD approximately at the current exchange rate. PC security researchers are totally against paying the ransom or contacting the people responsible for the Allcry Ransomware attack.
Dealing with an Allcry Ransomware Infection
Malware analysts advise against contacting the people responsible for the Allcry Ransomware. In most cases, they will not deliver the means to decrypt the affected files. They are just as likely to ignore the victim or ask for more money. Instead, taking precautionary methods against the Allcry Ransomware and similar ransomware Trojans you can avoid a lot of problems. Having an updated backup system in place is the most reliable way to avoid these attacks. If you have file backups on the cloud or on a place that threats can't reach, then you can restore your files easily rather than having to deal with the people responsible for the Allcry Ransomware. If computer users are available to restore their files for themselves, then the people responsible for the Allcry Ransomware attack lose all of their leverage. A reliable backup method combined with a good anti-virus program that is is the best protection against the Allcry Ransomware and similar threats.
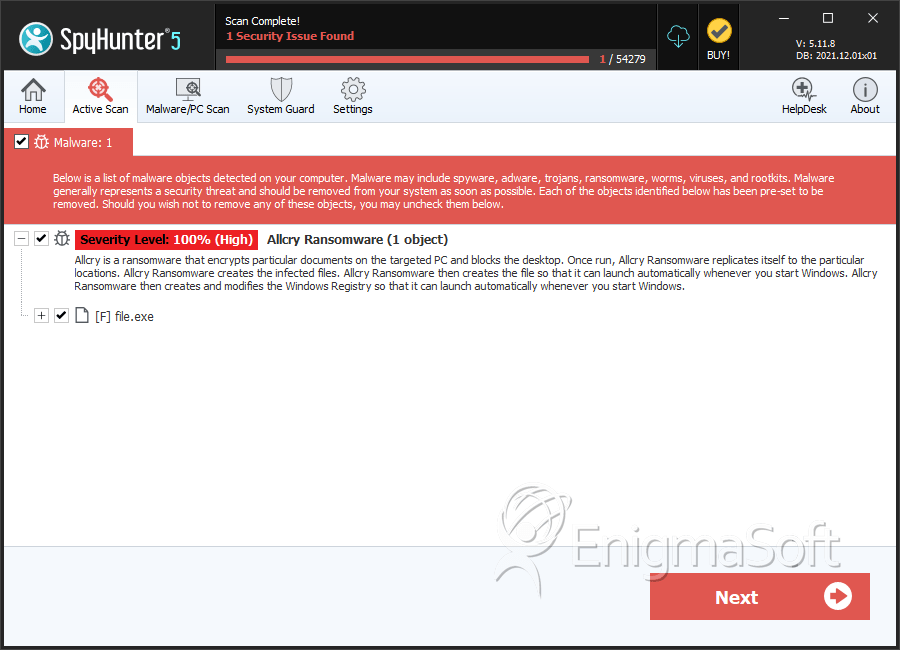
SpyHunter Detects & Remove Allcry Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | db8c7db3d873890d8ea2de2c9ba815e3 | 0 |

