Adware.VOPackage
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 6,024 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 283,889 |
| First Seen: | June 16, 2014 |
| Last Seen: | March 16, 2026 |
| OS(es) Affected: | Windows |
VOPackage is an adware program and potentially unwanted program. The VOPackage app and related files may load on your system due to you installing a random freeware program or bundled software application. After VOPackage has loaded, it could then display random ads in pop-up form. Allowing VOPackage to run on your system may then lead you to unwanted sites through redirects or loading of a questionable site as your default home page. The VOPackage is not a virus but it can be annoying in its actions to display ads or pop-up messages potentially leading to unwanted redirects. Detecting and removing VOPackage and all of its related files may require using an antimalware application with the ability to remove adware and browser hijackers.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| McAfee | Artemis!38E29B78CCAE |
| AVG | Generic_s.BN |
| AntiVir | RKIT/13833.A |
| GData | Win32.Trojan.Agent.CB93QW |
| McAfee | Artemis!F88501B1AB7F |
| AVG | AdInstaller.Vopackage |
| McAfee | Artemis!B702795A66F0 |
| AhnLab-V3 | Trojan/Win32.Inject |
| GData | Win32.Trojan.Agent.EMOX04 |
| Symantec | WS.Reputation.1 |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Suspicious-PKR.G |
| Avast | Win32:Dropper-gen [Drp] |
| Symantec | Trojan.ADH.SMH |
| McAfee | Artemis!EF11C2EFACFC |
| GData | Win32.Trojan.Agent.E4718A |
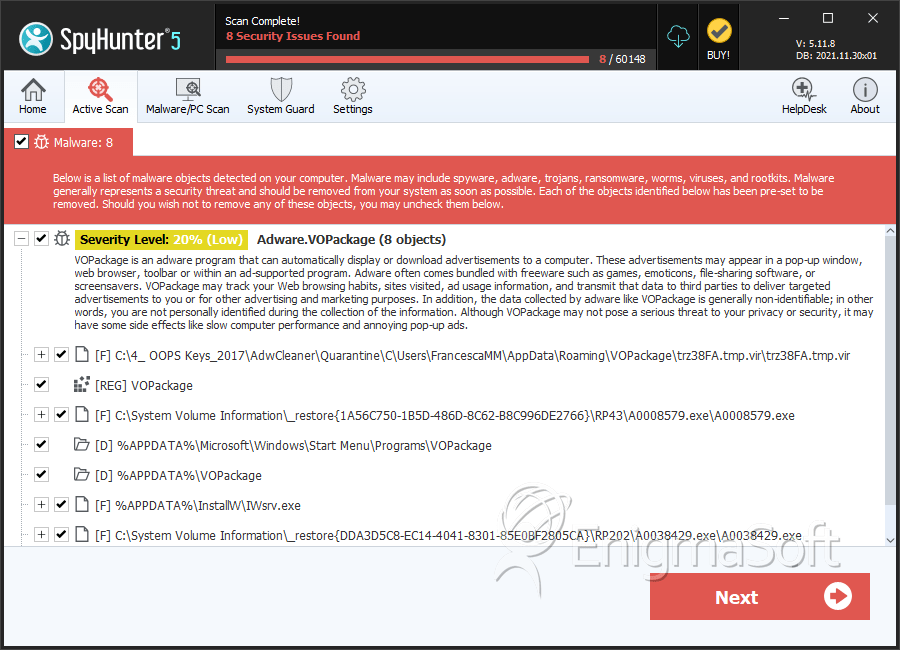
SpyHunter Detects & Remove Adware.VOPackage
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | trz38FA.tmp.vir | 77e1ee3a9ba1a7aa1744c2c869d51380 | 22,986 |
| 2. | A0390249.exe | c93576ad52cd4a6b455aca440cbb1c42 | 22,244 |
| 3. | A0008579.exe | f9b414bd06f66529b76ac62094b28ec2 | 6,489 |
| 4. | IWsrv.exe | 86a06f4ab93954f8422d9390ef041102 | 3,392 |
| 5. | A0038429.exe | 3e902906fb3786f2f7d8e594c1a6b53a | 2,175 |
| 6. | SWIService.exe | 22a48b1475e80e8a8d3025ea571f8ad6 | 1,001 |
| 7. | A0046060.exe | 20aebc4cc1cdffe692a8ca0de3a10e4b | 564 |
| 8. | dl[1].htm | 1d0a375502480b7575b99ff5246d95a4 | 554 |
| 9. | VuuPC.exe | 2c58742605655d0c61493737f39f723b | 412 |
| 10. | vp.exe | 5c480836b342f804d7ab412cce45dc7c | 353 |
| 11. | Run.exe | 09bce515770225d3949bac67dcdd075d | 309 |
| 12. | VOPackage.exe.vir | a475e36521a0e6d786530a7d0ee7ea87 | 302 |
| 13. | VOsrv.exe.vir | a7615f9c91f98bbea8574aeb1a74152d | 279 |
| 14. | A0009363.exe | 8458562d70a352365974fbe7509bef4e | 183 |
| 15. | VOsrv.exe | 10ef29b9c1dde9847905b4967e8f872b | 169 |
| 16. | setup_137.exe | ce16f7613eaf12f50c6d70e5ca3c0eb9 | 112 |
| 17. | VOPackage.exe | d10e43b384f368b4cd89946246159940 | 31 |
| 18. | JOSrv.exe | 9c4b43a21ffa0535faac0492b414ad2b | 12 |
| 19. | runasu.exe | 8a868b8be0411783041ba6e61d7d5591 | 6 |
| 20. | Uninstall.exe | 37ab183587cb7f3249ec0cd2412a7b38 | 6 |
| 21. | Uninstall.exe.vir | 4e708f48c2a0b3d91d76b39e99e1390c | 5 |
| 22. | 1_Offer_2.exe | efd68413a1f7086f031ac798de6a5b67 | 4 |
| 23. | Setup[1].exe | 84b992e8673e595658568c8285c89446 | 2 |
| 24. | Setup.exe | 90dfc005a96bbd1feec4b21507f01a2d | 2 |
Registry Details
Directories
Adware.VOPackage may create the following directory or directories:
| %APPDATA%\Microsoft\Windows\Start Menu\Programs\VOPackage |
| %APPDATA%\VOPackage |
| %USERPROFILE%\Start Menu\Programs\VOPackage |
Analysis Report
General information
| Family Name: | Adware.VOPackage |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
7f225fadfbc5c7b8f75331bf5cbe807b
SHA1:
bfa70624a68fb96f08da94f94b923baa50043dc9
SHA256:
6061DA1F32D194196C112C655722F6A30FC1BC830528573CA379AFAC35715C9B
File Size:
224.90 KB, 224897 bytes
|
|
MD5:
4333cae92e3616cdc06a37153722e843
SHA1:
1c146a846a101806561cc20901d28e6788f4667b
SHA256:
2AA2DDDD53C3A4B9281F5A9C444A2E892C78F0755EB5BA4EEDD37EAA82E769BE
File Size:
875.75 KB, 875751 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | VuuPC, You're Always a Click Away! |
| Company Name | VuuPC Limited |
| File Description |
|
| File Version |
|
| Legal Copyright | Copyright 2013 |
| Legal Trademarks | VuuPC is a trademark of CMI Limited |
| Product Name | VuuPC |
| Product Version |
|
File Traits
- Installer Manifest
- Installer Version
- nosig nsis
- Nullsoft Installer
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nslbd99.tmp\ipconfig.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nso4766.tmp\modern-header.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nso4766.tmp\system.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nso4766.tmp\userinfo.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\~nsu.tmp\au_.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | \??\C:\Users\Oltosuoa\AppData\Local\Temp\~nsu.tmp\Au_.exe | RegNtPreCreateKey |
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | \??\C:\Users\Oltosuoa\AppData\Local\Temp\~nsu.tmp\Au_.exe��\??\C:\Users\Oltosuoa\AppData\Local\Temp\~nsu.tmp | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Shell Execute |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"C:\Users\Oltosuoa\AppData\Local\Temp\~nsu.tmp\Au_.exe" _?=c:\users\user\downloads\
|
