Action Required On Your Email Account
When it comes to online safety, caution is everything. Cybercriminals rely on urgency, deception, and fear to trick unsuspecting users into giving up sensitive information. Phishing emails remain one of the most effective ways for scammers to infiltrate accounts, steal identities, and spread malware. One such campaign currently making the rounds is the 'Action Required On Your Email Account' scam, which preys on users' trust in their email providers.
Table of Contents
The False Promise of Security Updates
The fraudulent 'Action Required On Your Email Account' message pretends to come from a legitimate email service. It claims that the provider is rolling out an update to improve reliability and security, and urges the recipient to take immediate action to avoid service disruptions. A deadline is usually included to pressure users into reacting quickly without thinking critically.
The email contains a link labeled 'Click here to update your account'. Instead of leading to the provider's official platform, it redirects users to a phishing page carefully disguised as an email login portal. Any credentials entered there are harvested by scammers, granting them full access to the victim's email account.
Why Email Accounts Are a Prime Target
Email inboxes are treasure troves of information. They often store personal conversations, sensitive documents, and confirmations for social media, financial, and shopping accounts. Once attackers gain access, they can:
- Hijack connected accounts, including banking, e-commerce, and digital wallet services.
- Impersonate the victim to request money from contacts, spread scams, or deliver malware-laden files.
- Use stolen work email accounts as entry points to infect corporate networks with ransomware or other malicious payloads.
The fallout from such compromises can include identity theft, significant financial losses, and long-term privacy violations.
Beyond Just Phishing Links
Spam campaigns are versatile. In addition to fake sign-in portals, attackers frequently distribute malware through infected attachments. These can come in Word or OneNote documents, PDFs, ZIP archives, executables, or even JavaScript files. Some require extra user interaction, such as enabling macros or clicking embedded files, while others launch the infection the moment they are opened.
The ultimate goal is always the same: compromise the victim's device, steal information, and create further opportunities for fraud.
Spotting the Red Flags
While phishing emails are sometimes sloppy, many are professionally crafted and nearly indistinguishable from real messages. A few signs can help uncover them:
- Suspicious sender addresses that mimic but do not match the real domain.
- Generic greetings such as 'Dear user' instead of addressing the recipient by name.
- Links that do not lead to the official domain – always hover over them before clicking.
- Unsolicited attachments, often disguised as invoices, faxes, or delivery notes.
What To Do If You Fell for It
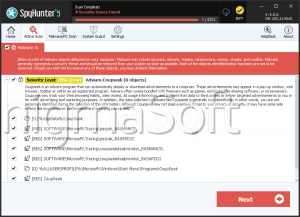
If you already entered your credentials on a phishing site, change your password immediately. Update not only the compromised email account but also any accounts linked to it. Contact your bank to secure your funds and potentially replace compromised cards if you entered financial information. If malware was downloaded, perform a full system scan with a reputable antivirus such as Combo Cleaner for Windows to eliminate infections.
Staying Protected Going Forward
To reduce the risk of future attacks, follow these security practices:
- Avoid opening attachments or links from suspicious or irrelevant emails, texts, or private messages.
- Stick to official download sources and avoid pirated or cracked software, which often carries hidden malware.
- Keep your operating system and software updated using only legitimate update tools.
- Run reliable antivirus software, ensure it is always updated, and schedule regular scans.
Final Thoughts
The 'Action Required On Your Email Account' campaign is just one of many phishing operations circulating online. Others like 'Alert Regarding Your System Credentials', 'EFT Debit Release', 'Your Account Security Settings May Need Attention', and 'UPS - Delivery Action Needed' all follow the same playbook: trick users into panicking and handing over their private data. Recognizing these tactics and responding calmly is the best way to avoid becoming a victim.