Acreed Stealer
Acreed is a modern information stealer that's risen quickly into the ranks of the most widespread stealers. Because it specifically targets credentials, browser artifacts, messaging apps, and cryptocurrency wallets, a single successful infection can lead to credential theft, hijacked crypto transfers, account takeovers, and long-term persistence on a victim machine. Protecting endpoints and user behaviour is therefore critical: once sensitive data leaves a device, it's often impossible to fully recover.
Table of Contents
Acreed Goes After High-value Digital Assets
Acreed focuses on data that has immediate monetary value or enables account takeover:
- saved passwords, cookies, and autofill entries from browsers (Brave, Chrome, Edge),
- browser-based and system cryptocurrency wallets (both full client and extension wallets),
- credit-card data and messaging app data that can be abused for fraud or social engineering.
Acreed actively hunts for a wide range of wallet software and browser extensions, including (but not limited to) ArgentX, Binance, Coinbase, Crypto.com, Kasware, Martian, MetaMask, OKX, Phantom, Rabby, ReadyWallet, Ronin, Sui, ToonKeeper, TronLink, and Trust. By enumerating both installed applications and browser extension folders, it maximizes the odds of locating keys, seed phrases, private JSON files, or other wallet material.
How The Malware Operates
Acreed is typically delivered via a loader (ShadowLoader) and follows a multi-stage injection and collection model:
- ShadowLoader drops two PE files that are wrapped with a legitimate WebView2 DLL—this legitimate wrapper helps the loader evade simple detection and signature checks.
- Once Acreed is running, it enumerates browser 'User Data' directories (bookmarks, history, cookies, cache, extensions, autofill and saved credentials) and scans for wallet files and extension data.
- It harvests messaging app data and other personal files that can be abused in follow-up attacks.
- Crucially, Acreed includes transaction-hijacking capabilities: it can replace wallet addresses shown on webpages, alter QR codes, substitute clipboard contents, and capture typed/submitted wallet addresses — all intended to divert funds to attacker-controlled wallets.
Unusual Command-and-Control (C2) Techniques
Acreed uses atypical public sources for configuration and C2, which helps it blend legitimate traffic with malicious signals:
- Some samples retrieve C2 information from a smart contract deployed on the BNB Smart Chain Testnet.
- Other samples use public posts on platforms such as Steam to encode control data.
These techniques make C2 discovery more challenging and complicate detection rules that focus only on classic C2 domains.
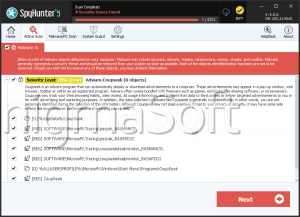
Attackers delivering Acreed employ a broad toolkit of infection routes:
pirated software and cracked installers, malvertising, tech-support scams, email attachments and malicious links, third-party updaters and downloaders, P2P networks, infected USB devices, and exploitation of unpatched software. This breadth means users can be exposed through both direct phishing and everyday risky downloads.
Why Acreed Is Dangerous
Acreed combines focused targeting of crypto wallets with broad browser and messaging data theft, and it uses a stealthy multi-stage loader and unconventional C2 channels to complicate detection. Its ability to hijack transactions (webpage/QR/clipboard manipulation) converts stolen data into near-immediate financial loss, making prevention and rapid containment essential. Strengthen endpoint controls, reduce stored secrets, and treat any confirmed infection as a high-urgency incident.