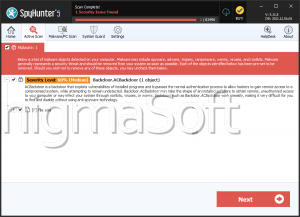
ACBackdoor
Most malware strains target Windows running machines, as this is the most popular operating system in the world undoubtedly. However, this does not mean that systems running alternative operating systems like OSX or Linux are impenetrable fortresses. Recently, researchers spotted a new malware strain that is capable of targeting various operating systems. The name of the threat is ACBackdoor, and it appears to be compatible with both Linux and the Windows OS. The Linux variant of the ACBackdoor is rather impressive. The Linux-based ACBackdoor executes its code without files, which reduces the footprint of the threat on the compromised device. Furthermore, this variant of the ACBackdoor can tamper with the properties of the running processes on the infected host. However, it would appear that the creators of the ACBackdoor likely specialize in threats targeting Linux, as the Windows variant of this threat is far less impressive, to say the least.
The ACBackdoor was first discovered as malware researchers noticed that the Fallout EK (Exploit Kit) was propagating a new strain of malware, which had never been seen before. The main use of this exploit kit leads experts to believe that the individuals behind the ACBackdoor have been active in this scene for a while and likely have generated enough capital to purchase high-end exploit kits.
Uses Generic Utility Names to Mask Itself
Once the ACBackdoor compromises a system, it will start gathering basic information about the infected host. Then, the threat will utilize HTTPS to transfer all the collected data to the server of its operators. The Linux variant of the ACBackdoor will attempt to remain under the radar of the victim by naming itself ‘Ubuntu Release Update Utility.’ On systems that are running Windows, the ACBackdoor will try to gain persistence by generating a new Windows Registry Key and masking itself as a ‘Microsoft Anti-Spyware Utility.’
Capabilities
There is nothing jaw-dropping when it comes to the capabilities of the ACBackdoor. However, this threat can do more than enough to cause great damage to the compromised host. The ACBackdoor can:
- Use the ‘run’ command to run remote shell commands on the host.
- Update itself using a command called ‘update.’
- Use the ‘execute’ command to grab and launch files from the attackers’ server.
- Gather data about the system using the ‘info’ command.
To avoid becoming a victim of the ACBackdoor, make sure you update all your applications regularly so that your system is not as vulnerable to threats. Also, make sure you download and install a legitimate anti-virus software suite that will protect your data and computer.