8lock8 Ransomware
The 8lock8 Ransomware is a ransomware threat that uses the AES-256 encryption to encrypt its victims' files and then demand the payment of a ransom in exchange for the decryption key. There is currently a decryption utility available to help computer users recover from an 8lock8 Ransomware infection. Therefore, there is no need to pay the 8lock8 Ransomware's ransom at this point.
Table of Contents
Unraveling the 8lock8 Ransomware Infection
The 8lock8 Ransomware encrypts the victim's files and changes their extension to '.the 8lock8,' displaying a ransom note on the victim's computer. The 8lock8 Ransomware copies HiddenTear, another encryption ransomware Trojan that is currently active in the wild. The 8lock8 Ransomware's ransom note is both in English and Russian, notifying the victims that their files have been encrypted and containing information about the payment. The 8lock8 Ransomware may be distributed using corrupted spam email attachments. The 8lock8 Ransomware may be distributed through file sharing networks disguised as a popular file on these networks. The 8lock8 Ransomware is also distributed using corrupted email embedded links specifically, which lead computer users to attack websites where corrupted scripts are used to deliver the 8lock8 Ransomware to the victim's computer.
Some Particularities About the 8lock8 Ransomware Attack
The 8lock8 Ransomware is very similar to HiddenTear, which is an open source ransomware threat that has been linked to a wide variety of other ransomware attacks. Threats related to the 8lock8 Ransomware and HiddenTear tend to share characteristics in the way they encrypt the contents of the victim's hard drive. After the 8lock8 Ransomware is delivered to the victim's computer, the 8lock8 Ransomware will start encrypting the victim's files. The 8lock8 Ransomware uses scripts to delete Shadow copies of files encrypted, as well as any System Restore and backup points. The 8lock8 Ransomware makes changes to the Registry Editor that allow the 8lock8 Ransomware to run whenever Windows starts automatically, meaning that it is essential to ensure that the 8lock8 Ransomware has been removed completely before attempting to recover from a backup copy of the encrypted files.
The 8lock8 Ransomware will encrypt the following file types (among various others):
zip,.bmp, .csv, .doc, .docx,., sql, .txt, .wav, .xls, ..avi, xlsx, .xml, ..ppt, .pptx, .rar, .sln, .htm, .html, .jpg, .mdb, .odt, .pdf, .php, .png, asp, .aspx.
After the 8lock8 Ransomware has encrypted the victim's files using an AES-256 encryption algorithm, the 8lock8 Ransomware changes the affected files' extension to '.the 8lock8' and delivers ransom notes in the form of a text file named 'READ_IT.txt' that are dropped in directories where the 8lock8 Ransomware has encrypted files. The following is the text of the 8lock8 Ransomware's ransom note:
'Files have been encrypted!Файлы были зашифрованы
It uses cryptographically strong algorithm!Используется криптостойкий алгоритм
contact by e-mail: d1d81238@tuta.io or d1d81238@india.com
to identify, use lower hash!для идентификации используйте нижний хэш
{Random hash identification}'
Fortunatelly, there is a Decryption Utility Available for the 8lock8 Ransomware
Fortunately, a decryptor for the 8lock8 Ransomware has been released. This involves a variant of a brute force utility that has been used to decrypt files encrypted by HiddenTear. A small file that was decrypted by the 8lock8 Ransomware can be used to find the decryption key using one of these available decryption utilities. There is one additional quirk related to the 8lock8 Ransomware: if the hash (included in the ransom note) ends with the string 'AH33,' it is possible to skip the decryption utility entirely and instead use the password 'Whendiplomacyends,Warbegins.1933' to decrypt it. This is displayed whenever the 8lock8 Ransomware tries to reach its Command and Control server to send the private encryption key but was unsuccessful in establishing a connection. As you can see, the best way to deal with the 8lock8 Ransomware is to prevent attacks in the first place by establishing safe browsing practices, and always using a reliable security application to protect your computer.
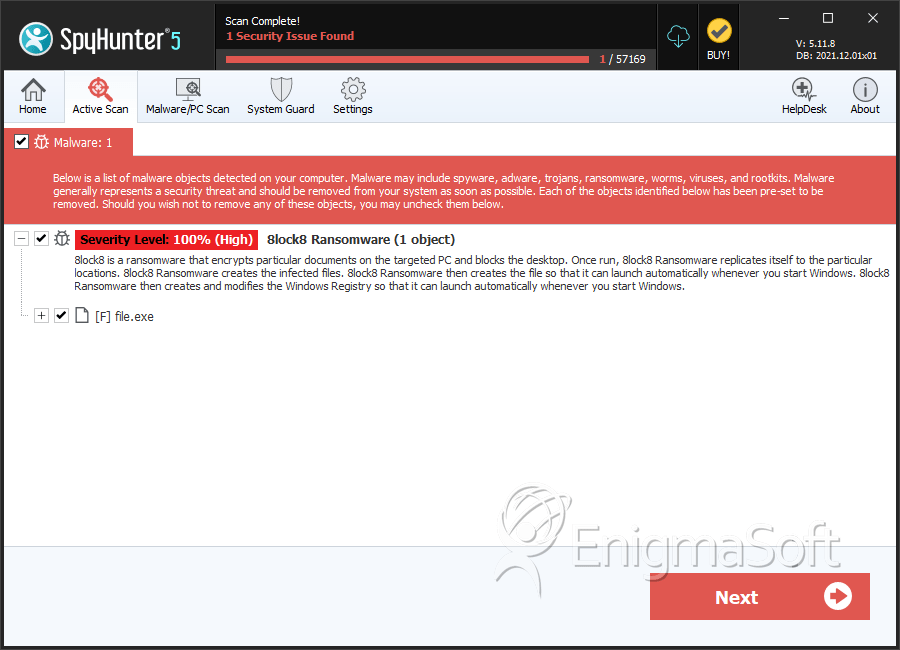
SpyHunter Detects & Remove 8lock8 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | cde35efa535dbda233dbf296c6ed462d | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.