7ev3n Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 1,146 |
| First Seen: | January 22, 2016 |
| Last Seen: | June 7, 2020 |
| OS(es) Affected: | Windows |
The 7ev3n Ransomware is a ransomware Trojan that is used to force computer users to pay large amounts of money by making their files inoperative. The 7ev3n Ransomware may be distributed using corrupted email attachments. Other common ways of distributing the 7ev3n Ransomware include fake software updates and peer-to-peer file networks. PC security researchers strongly advise computer users to protect their computers from ransomware Trojans like the 7ev3n Ransomware with the help of a reliable security application and by backing up all files on their computers.
Table of Contents
The 7ev3n Ransomware Demands a Very Expensive Ransom
The 7ev3n Ransomware will encrypt the victims' files, changing their extension to R5A and deleting all Shadow Volume copies. Once the victim's files are encrypted, the 7ev3n Ransomware displays a pop-up message informing the victim on how to pay the 7ev3n Ransomware's ransom using BitCoin. The 7ev3n Ransomware demands payment of an extraordinarily elevated ransom in exchange for the decryption key. The 7ev3n Ransomware pop-up message claims that if the ransom isn't paid within a certain time frame, the decryption key will be deleted. Without the decryption key, it is nearly impossible to recover encrypted files.
Why the 7ev3n Ransomware Victims shouldn’t Pay the Ransom
The 7ev3n Ransomware demands the payment of 13 BitCoin, which currently is more than five thousand USD! Almost all Ransomware Trojans demand ransoms of $500 to $1000 USD, so such an elevated amount is practically unheard of when it comes to these kinds of threats. According to the 7ev3n Ransomware message, victims have 96 hours to pay the ransom before their files are lost forever. PC security researchers strongly advise computer users against paying the 7ev3n Ransomware ransom. This allows con artists to continue carrying out their attacks and profit at your expense.
The following is the text of the 7ev3n Ransomware message:
YOUR PERSONAL INFORMATION ARE ENCRYPTED by 7ev3n
All your documents, photos, databases, office projects and other important files have been encrypted with strongest encryption algorithm and unique key, original files have been overwritten, recovery tools and software will not help. Private key is stored on a server and nobody can decrypt your files until you pay and obtain the private key.
You have only 96 hours to make a payment. If you do not send money within provided time, private key will be destroyed, and all your files will be lost. Follow the instructions:
1. Pay amount of 13 bitcoin (approximately 4980 USD) to address: bitcoin address, this unique address generated only for you.
2. Transaction will take about 50 minutes to accept and confirm the payment, decryption and uninstalling of this software will start automatically. For correct key and decryption, DO NOT: power off computer, disable Internet connection, run antivirus program. Usually decryption will take about 1-3 hours, average decrypt speed 21gb per hour.
Bitcoin is a digital currently that you can buy on ‘eBay.com’, ‘localbitcoins.com’, ‘anxpro.com’, ‘cued.com’ and many other online and physical exchangers through credit card, bank account, using PayPal and many other payment methods.
Warning, do not try to get rid of this program, any action taken will result in decryption key being destroyed, you will lose your files forever, one way to get you files os to follow that instructions. In case of non-payment reserve the right to publicly publish all encrypted files.
What is the Objective of Threats such as the 7ev3n Ransomware
Most ransomware Trojans currently active follow identical strategies to take money from computer users. Their attacks typically demand computer users to pay to decrypt their files. Even if the computer users pay the ransom, there is no guarantee that they will recover their files. Since it is so difficult to recover from a 7ev3n Ransomware attack, the best approach to dealing with these infections is prevention. Malware researchers advise computer users to backup all their files on an external memory device or the cloud and use a strong anti-malware application to protect their computers from intrusion.
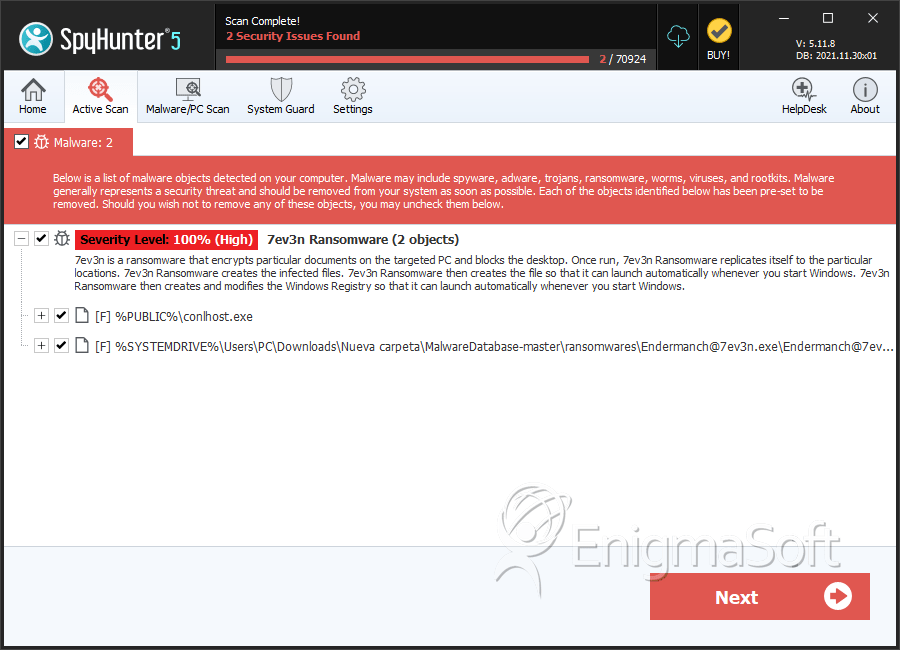
SpyHunter Detects & Remove 7ev3n Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | conlhost.exe | cfa8a707a2a65948f58736b32a2ddab5 | 41 |
| 2. | Endermanch@7ev3n.exe | 9f8bc96c96d43ecb69f883388d228754 | 28 |
