404 Keylogger
The 404 Keylogger is a new threat that got on the radars of cybersecurity experts recently. This keylogger is what is often referred to as ‘malware-as-a-service’ because its creators have opted to rent it out to anyone who is willing to pay. Sometimes, authors of malware sell the source code of their creations or offer a lifetime license to their clients. However, the creators of the 404 Keylogger only offer this threat for a limited amount of time. For the devious individuals who want to get access to the 404 Keylogger, its authors offer three subscription types - $30/month, $85/3 months, $175/6 months.
Poses as a Legitimate Software Tool
Most projects that are utilized as a ‘malware-as-a-service’ are sold on shady hacking forums. However, this is not always the case. Many threats of this type, including the 404 Keylogger, are often sold out in the open under the pretext that they are legitimate software tools. The 404 Keylogger is hosted on a public website that is designed to look genuine. The authors of this threat claim that the purpose of the 404 Keylogger is to help employers keep an eye on the online activity of their employees and make sure that they are not engaging in any inappropriate activities while at work. They also add that the 404 Keylogger is not intended to be used for any unsafe purposes. Of course, these are empty words, as both the creators of the 404 Keylogger and the clients who obtain it know what the real deal is – monitoring and collecting data. This is a very common tactic by malware creators who offer their tools as a commodity on publicly available Web pages. The creators of the 404 Keylogger promise their potential clients that they will provide them with very specified instructions on how to set up and operate this tool, as well as customer support in case they have questions. Furthermore, they claim that the 404 Keylogger will be updated regularly. Cyber-threats require regular updates to ensure that they remain undetectable by anti-virus tools.
Capabilities
It is evident by its name that the 404 Keylogger’s main purpose is to serve as a keylogger. This means that the 404 Keylogger will collect the user’s keystrokes, store them, and then exfiltrate the collected data to the operators of the C&C (Command and Control) server. However, this threat possesses a couple of other capabilities too. It can:
- Take screenshots of the user’s desktop and active windows and transfer them to the operators of the C&C server.
- Collect stored data such as FTP clients, login credentials, etc.
- Serve as a gateway for the attackers to plant and launch additional corrupted executable from a specified URL address.
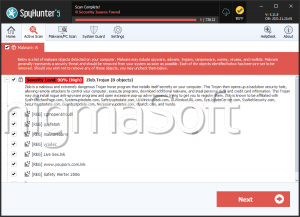
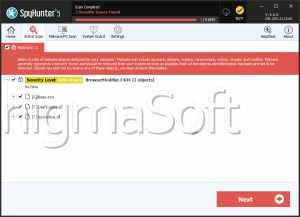
It is not yet known how many dodgy individuals have gotten their hands on the 404 Keylogger, but with a price this low, the keylogger has the potential to get very popular among cybercriminals. Make sure you keep your applications up to date, as this will make you less vulnerable to cyber attacks. Furthermore, download and install a reputable anti-virus software suite that will make sure your system remains protected in the future.