'0000 File Extension' Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 192 |
| First Seen: | June 6, 2016 |
| Last Seen: | March 14, 2023 |
| OS(es) Affected: | Windows |
The '0000 File Extension' Ransomware is an encryption ransomware Trojan. The '0000 File Extension' Ransomware is just one of several variants in the CryptMix family of threats released in 2017. There are several ways in which Trojans like the '0000 File Extension' Ransomware can be delivered to victims. The '0000 File Extension' Ransomware may be delivered through corrupted email messages designed to resemble messages from legitimate online platforms such as Facebook, Amazon or PayPal. These email messages will frequently include a corrupted embedded link or an attached file which, when opened, downloads and installs the '0000 File Extension' Ransomware onto the victim's computer.
Some Details about the '0000 File Extension' Ransomware Infection
The '0000 File Extension' Ransomware, like most encryption ransomware Trojans, will use a strong encryption algorithm to make the victim's files unusable. The victim's files will become useless because the threat uses a combination of the RSA and AES encryptions and, without the decryption key, which the cybercrooks hold in their possession, there's no way to recover the ciphered data. The '0000 File Extension' Ransomware takes the victim's files hostage. The '0000 File Extension' Ransomware targets the user-generated files but will avoid the Windows system files. The file that may be encrypted by attacks like the '0000 File Extension' Ransomware include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The files encrypted by The '0000 File Extension' Ransomware attack will mark the files it chooses to encrypt with the file extension '.0000', added to the end of each affected file's name to indicate that the file has been encrypted by the '0000 File Extension' Ransomware attack. Apart from encrypting the victim's files, the '0000 File Extension' Ransomware will interfere with recovery options in Windows, such as the use of the Shadow Volume Copies or the Windows Restore.
How the '0000 File Extension' Ransomware Demands Its Ransom Payment
The '0000 File Extension' Ransomware delivers a ransom note to the infected computer once the victim's files have been encrypted. The '0000 File Extension' Ransomware delivers its ransom note in the form of a text file named '_HELP_INSTRUCTION.TXT' that will be dropped on the infected computer's desktop. The full text of the '0000 File Extension' Ransomware ransom note is:
'Hello!
Attention! All Your data was encrypted!
For specific informartion, please send us an email with Your ID number:
y0000@tuta.io
y0000@protonmai1. com
y0000z@yandex.com
y0000s@yandex.com
Please send email to all email addresses! we will help you as soon as possible!
DECRYPT-ID-[RANDOM CHARCTERS] number'
PC security researchers have associated the '0000 File Extension' Ransomware with an executable file named 'BC4C39B0AE.EXE' present on victim's computers.
Dealing with a '0000 File Extension' Ransomware Infection
Although a good security program should be capable of removing the '0000 File Extension' Ransomware from the victim's computer, it is important to take steps to ensure that your data is safe. This is because security software can remove the '0000 File Extension' Ransomware, but it is impossible to restore files encrypted with the combination of the AES and RSA encryptions that are used by attacks like the '0000 File Extension' Ransomware. Because of this, a combination of file backups and a reliable malware solution can protect computer users from threats like the '0000 File Extension' Ransomware.
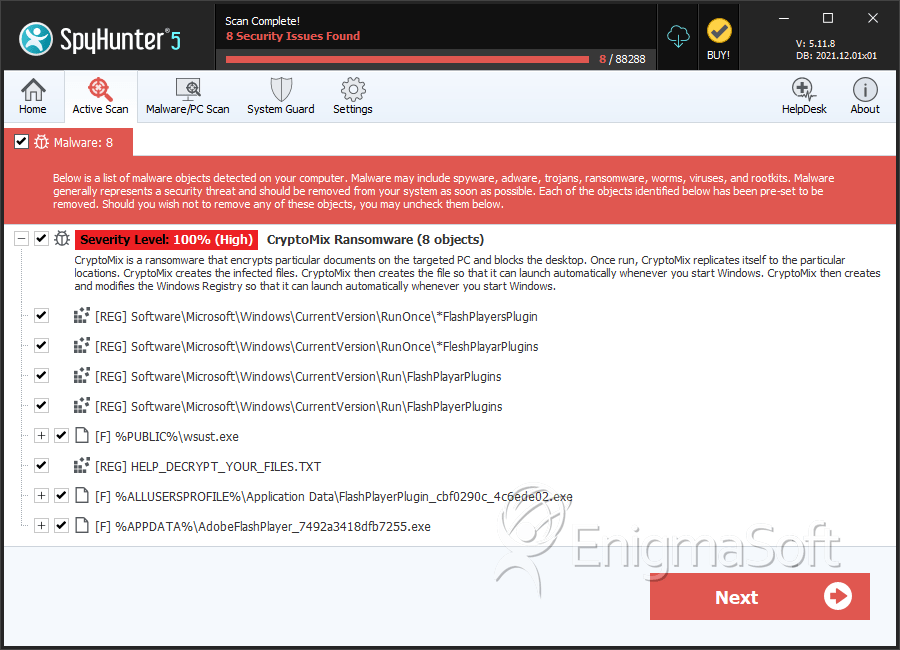
SpyHunter Detects & Remove '0000 File Extension' Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | wsust.exe | 32b6f1ad13030cd9fe4d574377c41da6 | 30 |
| 2. | FlashPlayerPlugin_cbf0290c_4c6ede02.exe | f26be6279ec6092515d9dae51563660c | 16 |
| 3. | AdobeFlashPlayer_7492a3418dfb7255.exe | 0f43c5cf5f627ed0bc650fd61094d680 | 7 |
| 4. | AdobeFlashPlayer_94e30973ab4e2d2.exe | 818a0a4a3843f7eb7166a807a597898a | 5 |
| 5. | AdobeFlashPlayer_cc1414a71ab0ee.exe | a9e64c10bb40d127e7ae7d622eb47b8e | 4 |
| 6. | AdobeFlashPlayer_b8a94cdf1330f5.exe | ad66f350d86b140201fa0885f5d09fe0 | 4 |
| 7. | BC001B7832.exe | 7dca6ef84f0c99f34ca21fae124d4f1b | 4 |
| 8. | AdobeFlashPlayer_907b51565e5a75e5.exe | 8002bee84df90f2bd177bceb0ae604a9 | 3 |
| 9. | AdobeFlashPlayer_3207783b69ba0b7d.exe | 99f2ea85b58ed6b138a577d6782308a0 | 2 |
| 10. | AdobeFlashPlayer_70a333d85e797934.exe | 2728a5665ec6ae0b03321d0f4b2c8e2e | 2 |
| 11. | AdobeFlashPlayer_e82246b15d9a70f0.exe | 4ba02659f560b420d9f6dfe875e0e124 | 2 |
| 12. | FlashPlayerPlugin_cb8b2ee_681b245c.exe | ab352361300a6dbe645d332e838e5236 | 2 |
| 13. | AdobeFlashPlayer_502277412c7b42ee.exe | 1af6e689a041ab774233d5e620f78cc1 | 1 |
| 14. | AdobeFlashPlayer_b0619e261a7322d2.exe | 5bb7d85f7a5f1d2b01efabe5635e2992 | 1 |
| 15. | AdobeFlashPlayer_40942f642c280de6.exe | 7b2feb0796bb932d89437877d168de0d | 1 |
| 16. | AdobeFlashPlayer_8cd260f56cda739b.exe | 6b67d8d65b3f0c63dac45e246fb5f1d6 | 1 |
| 17. | AdobeFlashPlayer_7014f5a0fe9ca174.exe | 9cca586f1eee2bb729f5fc49421d5a8d | 1 |
| 18. | AdobeFlashPlayer_9c6c3b96dc3cb1eb.exe | 3ab3afb15dba15c7dd9391f4dc4d335b | 1 |
| 19. | FlashPlayerPlugin_9ddb30cf_c80c92f8.exe | 0995230b95584a48f405c25e3d370482 | 1 |
| 20. | file.exe | 0403db9fcb37bd8ceec0afd6c3754314 | 1 |
| 21. | cryptomix.exe | cacf78f42e19d6253351e97842d815da | 0 |

