Zentom System Guard
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 53 |
| First Seen: | July 20, 2011 |
| Last Seen: | February 25, 2023 |
| OS(es) Affected: | Windows |
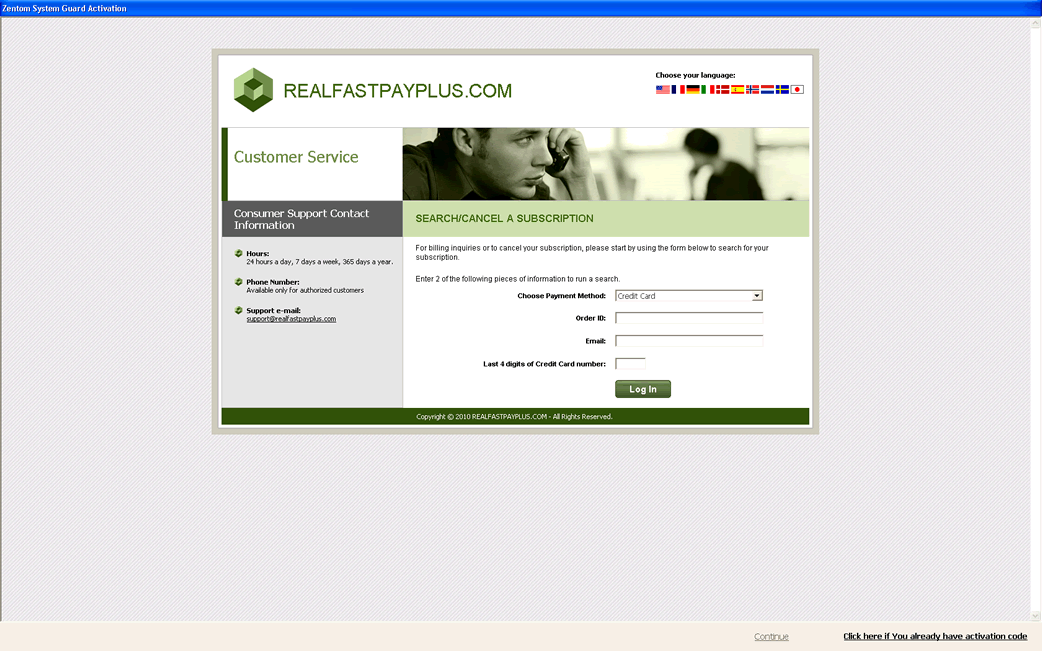
Zentom System Guard Image
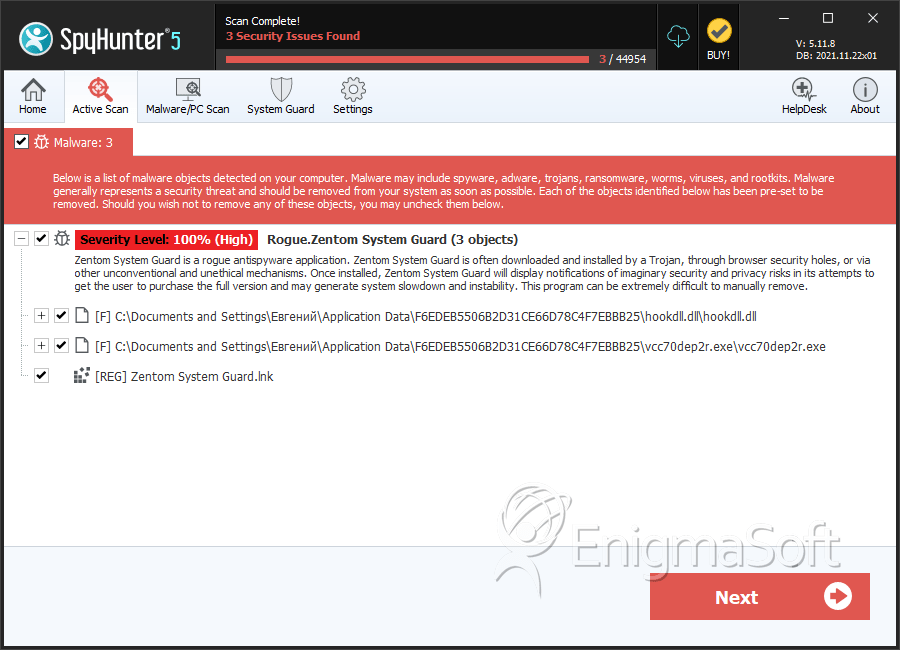
Zentom System Guard is a clone of the fake anti-spyware program Zentom System Guard Protection. These fake security applications are what are known by computer security experts as "rogueware". Rogue anti-spyware programs like Zentom System Guard are programs designed to resemble legitimate security utilities; however, in reality they use a variety of underhanded tactics to trick computer users into disclosing their credit card information. Regardless of Zentom System Guard's marketing and genuine-looking appearance, Zentom System Guard is not a real anti-spyware application. If you have installed Zentom System Guard on your computer, remove Zentom System Guard immediately with a real anti-spyware program.
Table of Contents
How Zentom System Guard Tries to Trick You
Zentom System Guard uses several approaches to make you believe that your computer is in trouble. Zentom System Guard's actions are typical of most rogue security programs. Typically, a Zentom System Guard infection will follow these steps:
- Zentom System Guard is installed on a computer, usually using misleading advertising or is delivered by a Trojan infection.
- Zentom System Guard will then display a fake computer scan showing numerous fake infections on the computer. This will be accompanied by numerous fake security alerts and pop-up notifications.
- To reinforce the idea that the computer is infected, Zentom System Guard will cause several problems on the infected computer. Some of these include blocked Internet access, failure to launch executable files and legitimate security applications, and severely decreased system performance.
- Zentom System Guard will refuse to fix any of the supposed "infections" unless the computer user is willing to enter his credit card information to "upgrade" to a full version of Zentom System Guard.
Of course, since Zentom System Guard is causing problems in the first place, giving Zentom System Guard your credit card information is completely useless and will only leave you vulnerable to identity theft and your money being stolen. You should not be fooled by Zentom System Guard's realistic-looking interface. This program has absolutely no security capabilities; Zentom System Guard is comprised solely of the interface and a collection of Trojans and harmful scripts that cause the computer problems mentioned above.
Removing Zentom System Guard for Good
A properly updated anti-malware application should take care of rogue anti-spyware programs like Zentom System Guard. However, it may be difficult to gain access to your security software, because Zentom System Guard tries to protect itself from removal. Two ways in which Zentom System Guard protects itself are by blocking access to Internet browsers and redirecting browsing to prevent the computer user from getting help online and by blocking legitimate security applications from running. To avoid Zentom System Guard's tactics, it is recommended that you launch Windows in Safe Mode (by pressing F8 during start-up) and then run your anti-malware program as normal.









SpyHunter Detects & Remove Zentom System Guard
Zentom System Guard Video
Tip: Turn your sound ON and watch the video in Full Screen mode.

File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | hookdll.dll | 0aebcc563df1a5a7f8996df00ae16c69 | 10 |
| 2. | vcc70dep2r.exe | 21872480abb724db4b9c2bec68bab7f7 | 7 |
| 3. | %APPDATA%\Adobe\plugs\KB2721125.exe | ||
| 4. | %AppData%\[RANDOM CHARACTERS]\hookdll.dll | ||
| 5. | %APPDATA%\Adobe\plugs\KB2692265.exe | ||
| 6. | %AppData%\[RANDOM CHARACTERS]\[RANDOM CHARACTERS].exe | ||
| 7. | %APPDATA%\205BA7C8FC5F7E32A2A4797AFBB34F61\hookdll.dll | ||
| 8. | %APPDATA%\205BA7C8FC5F7E32A2A4797AFBB34F61\nv716saver.exe | ||
| 9. | %TEMP%\2B88A7.dmp | ||
| 10. | %TEMP%\2AD39F.dmp | ||
| 11. | %AppData%\[RANDOM CHARACTERS]\ | ||
| 12. | %TEMP%\WER14.tmp | ||
| 13. | %TEMP%\WER15.tmp.dir00\appcompat.txt | ||
| 14. | %USERPROFILE%\Start Menu\Programs\Zentom System Guard\Zentom System Guard.lnk | ||
| 15. | %USERPROFILE%\Start Menu\Zentom System Guard.lnk | ||
| 16. | %AppData%\[RANDOM CHARACTERS]\enemies-names.txt | ||
| 17. | %StartMenu%\Programs\Zentom System Guard\ | ||
| 18. | %UserProfile%\Desktop\Zentom System Guard.lnk | ||
| 19. | %TEMP%\FY11.tmp | ||
| 20. | %TEMP%\WER13.tmp | ||
| 21. | %APPDATA%\205BA7C8FC5F7E32A2A4797AFBB34F61\local.ini | ||
| 22. | %TEMP%\44d18f1b51a1182dac79e4320ec31538310a8c5f | ||
| 23. | %TEMP%\WER14.tmp.dir00\appcompat.txt | ||
| 24. | %TEMP%\WER16.tmp.dir00\appcompat.txt | ||
| 25. | %USERPROFILE%\Start Menu\Programs\Zentom System Guard\Uninstall.lnk | ||
| 26. | %AppData%\[RANDOM CHARACTERS]\local.ini | ||
| 27. | %StartMenu%\Programs\Startup\Zentom System Guard.lnk | ||
| 28. | %StartMenu%\Programs\Zentom System Guard\Zentom System Guard.lnk | ||
| 29. | %TEMP%\WER15.tmp | ||
| 30. | %TEMP%\2A9473.dmp | ||
| 31. | %APPDATA%\Microsoft\Internet Explorer\Quick Launch\Zentom System Guard.lnk | ||
| 32. | %TEMP%\2A8F24.dmp | ||
| 33. | %TEMP%\WER13.tmp.dir00\appcompat.txt | ||
| 34. | %TEMP%\2AE6AA.dmp | ||
| 35. | %USERPROFILE%\Start Menu\Programs\Startup\Zentom System Guard.lnk | ||
| 36. | %AppData%\[RANDOM CHARACTERS]\lsrslt.ini | ||
| 37. | %StartMenu%\Zentom System Guard.lnk | ||
| 38. | %StartMenu%\Programs\Zentom System Guard\Uninstall.lnk |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.