Worm.Shopper.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 10 |
| First Seen: | July 24, 2009 |
| Last Seen: | December 12, 2025 |
| OS(es) Affected: | Windows |
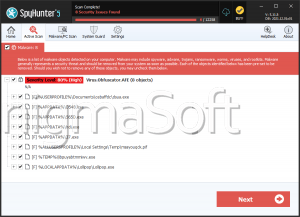
Worm.Shopper.A is a network worm that spreads to systems with poor security. Worm.Shopper.A will infect the explorer.exe process in the DLL cache folder while it attempts to replicate across networks. Worm.Shopper.A will search a victim's system for private information such as credit card numbers, passwords, and other personally identifiable information. Do not delay the removal of Worm.Shopper.A from your system once detected.
Table of Contents
Aliases
4 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| McAfee-GW-Edition | Worm.Shopper.A |
| Ikarus | Trojan-PWS.Agent.rtt |
| Authentium | W32/Shopper.A |
| AntiVir | Worm/Shopper.A |
Analysis Report
General information
| Family Name: | Adware.Shopper.A |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
0410c652d6f1d8b8bdea82cf4cd21565
SHA1:
b4c631eb3dcfe7b8c3251fa4c45581a5de733cca
SHA256:
D9C43E55E37C92179D05533F1582FBC8CAEBBCB5F258291313E147EF89C08E04
File Size:
4.23 MB, 4228960 bytes
|
|
MD5:
6ed40afc8e4ea64a91648c8e472770f2
SHA1:
2c7616b445ef6b8e88932b1d6b30e47c3f338cb1
SHA256:
8477906CBD95D85E38963F9815A1C615A014199C2CDD4DC41B67D54E59820DBC
File Size:
4.25 MB, 4254016 bytes
|
|
MD5:
64fe6524d7443bc96f9a8875165d0bc9
SHA1:
c7ddd47afe5f8a7722fd7b921b874c32318435dd
SHA256:
7E12ACB2074E059BDCF947A7BF101EFD94ABB709BDC1F79ABA9C00032EE93A2B
File Size:
4.82 MB, 4821040 bytes
|
|
MD5:
a1a4b8cb94bcc5ae788f5fac7d23a385
SHA1:
6be023c6f0898fdb9cbc61bb012a502b07ddd6c6
SHA256:
C1E234B38216C6ABC2F31C861AB342FE547B32BBEE5AA9E2F13FCF7D21CF5EFF
File Size:
4.80 MB, 4800048 bytes
|
|
MD5:
2d4f957f8f9e9f8ee0704c04ecb82b35
SHA1:
9c90fc76cf6cad5b8c7108431bbc9e69ea6f1c53
SHA256:
CAC007E57A2271FF3AC95BF235DAA7F8112C73CF6B2299436E8DBF5BC13B55A2
File Size:
4.83 MB, 4825136 bytes
|
Show More
|
MD5:
75a7c5bf6c393dec5db7a6b6a4be7c5c
SHA1:
e6b57624762d1cc805fe41bd294e7b1282ec4f5a
SHA256:
17829822A4342DCCE258E7228442EBD9B3B90CA8FCC680E894AB2AF731E3DAD7
File Size:
4.81 MB, 4809272 bytes
|
|
MD5:
56729a3d33ec09d0621a9bde2b4d77a8
SHA1:
3f64b791f6f6827da4b1d8eaa4214806f09b8810
SHA256:
B3B7E99F2A7CB36D55D46BE4EB23A0E95659A0B804CAC67B52FD65D1A973581E
File Size:
4.22 MB, 4221488 bytes
|
|
MD5:
0316a4acf22a5e0a9e4df255648dd5ad
SHA1:
ade18d843115a1c8ac7d6d85c00acdd70ad98356
SHA256:
DB9C1E82E8007A109621E470C24D306A859226A2AAC4398BAAB1E20451A1F39C
File Size:
4.82 MB, 4824112 bytes
|
|
MD5:
19f8dfa291ecb6b32938bfa3310cf440
SHA1:
68d9f993450a018e644266c005d47dc57ac70a56
SHA256:
7003BDBD6B5A2DFAB1A35E5B770FA27B537E29DF85765CA8113256AF067C6C33
File Size:
4.83 MB, 4830264 bytes
|
|
MD5:
4821e7106733fb6ff6c89ecdacbba74c
SHA1:
3b2e200acb1595098739ad52a925032fe6127ad7
SHA256:
7FDA2D3C9A46A768E38343235077F6D6765883AF1A1A2D40844EB38789960ECD
File Size:
4.81 MB, 4808240 bytes
|
|
MD5:
e87640d34c39dec811ba2f9b4eda887b
SHA1:
39b0600f3399a29eac7b155f5a019c5df1a80d10
SHA256:
5A77A41B16557BBB73BC8CDD7F526391F1F914D60083E05791F5B0F539E3F872
File Size:
4.80 MB, 4799024 bytes
|
|
MD5:
fefbde24a97344f2a4003bb0eb1b7469
SHA1:
6be604c7a607ec8c2a8d3f7ef350cbda730c6773
SHA256:
CFEAF4D705C8FFB801A8A056671E572E805C88EB146BB4E043F0AA1B5F114D02
File Size:
4.80 MB, 4802608 bytes
|
|
MD5:
b63160ce637f295c79610f4c974d7d48
SHA1:
4fdc580c3dbd9421d5cad0dce36a2887f23110c3
SHA256:
7431F3B4BA8BBE07F0E01F7E2FB47E47FA89E2F7BF2ADD7AC558E62BB987A90B
File Size:
4.80 MB, 4802616 bytes
|
|
MD5:
3783b895500d3e3cf6124d9ea2d50da2
SHA1:
8a92871835510c2b198b6a08907d9034cd7ff825
SHA256:
7F19F9A1EA5C98D8647456AA1FC59F31CD79E1EA57979E8A10157E2F556A355C
File Size:
4.83 MB, 4830264 bytes
|
|
MD5:
e6faee4713b46086cc5a0246ded75c87
SHA1:
02b6e7aa1082a3e21a1e0741dd79853f68129b67
SHA256:
37F0FB69EA3D2B80270DF24F4D17A4394C95C6D5DB0A82C06E03D29A28631311
File Size:
4.81 MB, 4808240 bytes
|
|
MD5:
9df49a3fe3fa421b424f70d530ffe09d
SHA1:
5421950191fbd5dd2afcad7852ca69e3304a597a
SHA256:
262A015BF2D1A2846B224F6C3E8B1C250E746C209928D1362D3D122B3E6B3AA5
File Size:
4.80 MB, 4797496 bytes
|
|
MD5:
ebaeb0daf490f8e9fdebcbc17c534aa6
SHA1:
1a95c82dad4154eac8369324ccbb9fec16fe01f2
SHA256:
D3F2943A59A311F574411BDDE436B35785C6AFFED73A4FA6B73BC52ABAECA31D
File Size:
4.79 MB, 4791856 bytes
|
|
MD5:
fc1610d75d1ac3aa5ac12806f56852be
SHA1:
719044afebb5103dab89c244b3ad072bb61065a4
SHA256:
9201813E3FB247C96E14C8ABEC57AA0ADE6AA3A30D3A8A3E8F84819EA0EA1625
File Size:
4.81 MB, 4806704 bytes
|
|
MD5:
1b4dbecb1aaa18ecd0aa0f26ce1c40bc
SHA1:
81cb38a92ff914ce97718337bad521b9a5e58930
SHA256:
A918FF96F36EC82AE9A0C6ADEB948F300B782D35BCBC590802C61E73EFF061E0
File Size:
4.84 MB, 4842032 bytes
|
|
MD5:
a94a12e2d52d59e2c7fbcefcc2f9cb2c
SHA1:
2a2642b6323cf91aef3dfd63f08a91f072b21de0
SHA256:
FEC366A292E008BD7EA052E8E68FE9C512B14CDE9473591F1B5DF2237E7704D0
File Size:
4.84 MB, 4840504 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
Show More
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename | SetupHlp.dll |
| Product Name |
|
| Product Version |
Show More
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| AVB Disc Soft, SIA | Entrust Code Signing Root Certification Authority - CSBR1 | Root Not Trusted |
| DT Soft Ltd | VeriSign Class 3 Code Signing 2009-2 CA | Self Signed |
File Traits
- 2+ executable sections
- dll
- HighEntropy
- Installer Version
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 12,291 |
|---|---|
| Potentially Malicious Blocks: | 299 |
| Whitelisted Blocks: | 11,613 |
| Unknown Blocks: | 379 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.OFHA
- Convagent.I
- Crack.FB
- Draobo.A
- Eszjuxuan.B
Show More
- Farfli.LE
- Lazzzy.A
- Outbrowse.CG
- Shopper.A
- Ursnif.AD
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.0.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.1.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\microsoft\windows\usrclass.dat{dba6b5ef-640a-11ed-9bcb-f677369d361c}.txr.2.regtrans-ms | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Shell Execute |
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\b4c631eb3dcfe7b8c3251fa4c45581a5de733cca_0004228960.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2c7616b445ef6b8e88932b1d6b30e47c3f338cb1_0004254016.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\c7ddd47afe5f8a7722fd7b921b874c32318435dd_0004821040.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\6be023c6f0898fdb9cbc61bb012a502b07ddd6c6_0004800048.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\9c90fc76cf6cad5b8c7108431bbc9e69ea6f1c53_0004825136.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\e6b57624762d1cc805fe41bd294e7b1282ec4f5a_0004809272.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3f64b791f6f6827da4b1d8eaa4214806f09b8810_0004221488.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\ade18d843115a1c8ac7d6d85c00acdd70ad98356_0004824112.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\68d9f993450a018e644266c005d47dc57ac70a56_0004830264.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3b2e200acb1595098739ad52a925032fe6127ad7_0004808240.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\39b0600f3399a29eac7b155f5a019c5df1a80d10_0004799024.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\6be604c7a607ec8c2a8d3f7ef350cbda730c6773_0004802608.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\4fdc580c3dbd9421d5cad0dce36a2887f23110c3_0004802616.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\8a92871835510c2b198b6a08907d9034cd7ff825_0004830264.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\02b6e7aa1082a3e21a1e0741dd79853f68129b67_0004808240.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\5421950191fbd5dd2afcad7852ca69e3304a597a_0004797496.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\1a95c82dad4154eac8369324ccbb9fec16fe01f2_0004791856.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\719044afebb5103dab89c244b3ad072bb61065a4_0004806704.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\81cb38a92ff914ce97718337bad521b9a5e58930_0004842032.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2a2642b6323cf91aef3dfd63f08a91f072b21de0_0004840504.,LiQMAxHB
|