Windows Simple Protector
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | March 24, 2011 |
| Last Seen: | January 8, 2020 |
| OS(es) Affected: | Windows |
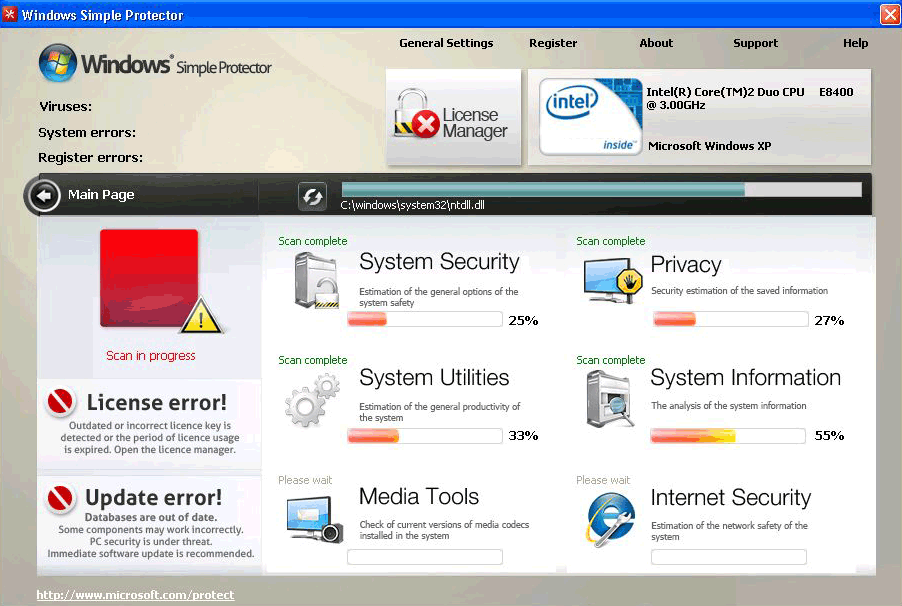
Windows Simple Protector Image
Windows Simple Protector pretends to be anti-virus software, so that Windows Simple Protector can scare you into thinking that your computer is infected with viruses that only a paid copy of Windows Simple Protector can remove. Regardless of what Windows Simple Protector may tell you, Windows Simple Protector is not a real Windows program, Windows Simple Protector can't identify or remove threats, and you will not get anything for your money if you pay for Windows Simple Protector's software license.
Table of Contents
How Windows Simple Protector Infects Your Computer
In order to get onto your computer in the first place, Windows Simple Protector needs to trick you into downloading the malware without knowing it. So, Windows Simple Protector uses a Trojan known as the Fake Microsoft Security Essentials Alert Malware, which – you guessed it – is malware that generates fake Microsoft Security Essentials Alerts. This Trojan is usually hidden in a Flash update or video codec that you download from a malicious site, say, after following a link in a spam email or spam social network post. On the other hand, the Trojan may be bundled into something that you download, like a program from a freeware site. Once the Trojan is on your computer, Windows Simple Protector starts its process of showing alerts, which always follows the same linear pattern. The fake alerts warn that Windows has found an unidentified Trojan, then they say that the Trojan has been identified as Trojan.Win32.PAV.64.a, and then they offer a file download in order to remove this nonexistent Trojan. In this case, the file that the Trojan downloads is Windows Simple Protector.
Symptoms Caused by Windows Simple Protector
The first thing that will happen once Windows Simple Protector is downloaded is that Windows Simple Protector will be set up to start when Windows starts. So, every time you start Windows, you will see the Windows Simple Protector interface before you even get to see the desktop or taskbar. The interface has some icons, and Windows Simple Protector uses the Windows name and logo – without permission, of course – but its real reason for being is to run fake scans of your computer. Every time it appears, the Windows Simple Protector interface will plan an animation simulating a scan, and then Windows Simple Protector will tell you that multiple threats have been detected on your computer. Windows Simple Protector will try to make it sound as if your computer's security is in serious jeopardy, and then Windows Simple Protector will prompt you to purchase a license for Windows Simple Protector in order to remove the threats listed in the scan results. Needless to say, because Windows Simple Protector is phony and utterly useless, you will not get any functionality out of the malware by paying for a license.
Once you have waited through the fake scan, you should be able to reach the desktop, but that doesn't mean that Windows Simple Protector will leave you alone. In fact, you will not be able to use your computer at all, because Windows Simple Protector will continue its campaign of scare tactics and self-preservation, severely disabling all of your PC's normal functions in the process. You will see the same error messages and alerts over and over, which will say the same three false things about Firefox, lsass.exe and your "register keys" somehow being involved in security risks. Windows Simple Protector will use these fake alerts in order to remind you to buy a license.
Windows Simple Protector also goes to great lengths to make sure that you can't remove the malware from your system and that you can't go looking for help. Windows Simple Protector disables all programs except for your web browser, and that means that you can't even use Task Manger to try to stop Windows Simple Protector's processes. You can forget about removing Windows Simple Protector using ordinary methods, when Windows is in its normal mode. Don't get your hopes up about the availability of the Internet, either, because Windows Simple Protector will prevent you from viewing any websites other than Windows Simple Protector's own payment site. All of this is part of Windows Simple Protector's attempt to stay on your computer as long as possible, and so Windows Simple Protector will accompany these crippling restrictions on your computer usage and will say that it's all in the name of your security.
Windows Simple Protector’s Related Malware, and What to Watch out For
As previously mentioned, Windows Simple Protector is just a re-release of malware that has been around for a while. Actually, this same malware has been re-released with a new name every single day, for practically the entirety of 2011. Regardless of what name the malware may use, it is all part of a single large-scale Internet scam, which was originated in Russia. The names for this malware are generated in a very simple way, which is the word "Windows" followed by one or two additional words pulled from lists of plausible-sounding terms. After a while, these names become easy to spot. This malware doesn't seem to be going anywhere anytime soon, so it is a good idea to be cautious about any program that claims to be an anti-virus or anti-malware application, and which has a name that fits this naming pattern.















Aliases
3 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| eTrust-Vet | Win32/FraudSecurityEssentials.A! |
| ClamAV | PUA.Packed.ASPack |
| NOD32 | a variant of Win32/Adware.PrivacyGuard2010.AU |
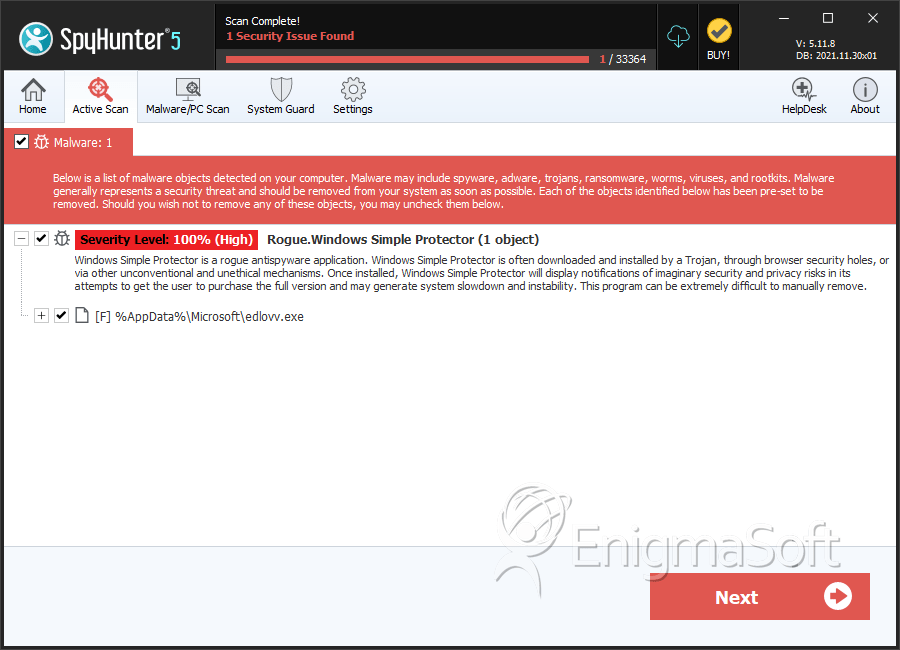
SpyHunter Detects & Remove Windows Simple Protector
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | edlovv.exe | 8971c85480bbb172b0736da087c0ea0d | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.