Win32/TrojanDownloader.Agent.QXN
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
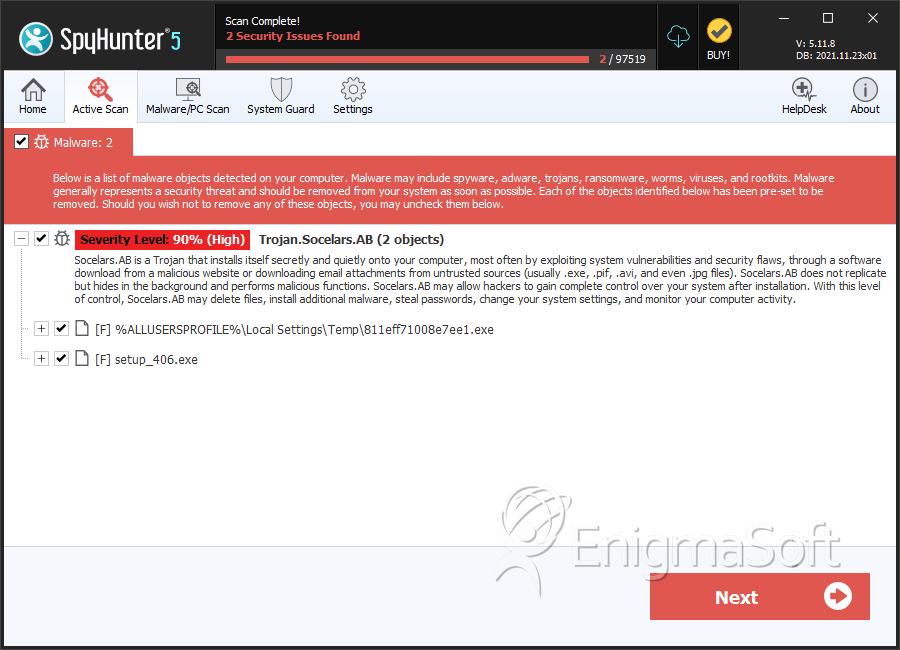
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 12,059 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 1,199 |
| First Seen: | December 1, 2011 |
| Last Seen: | September 7, 2023 |
| OS(es) Affected: | Windows |
Taking advantage of all the gift deliveries around the holiday season, criminals have started to send out fake emails from courier services and post offices in order to infect their victims with the Win32/TrojanDownloader.Agent.QXN Trojan. If you usually purchase online, chances are that you are expecting a package delivery during this holiday season. Criminals resort to emails with the 'failed package delivery' subject line in order to get your attention and convince you to open them and click on malicious links or download a dangerous attachment. The Win32/TrojanDownloader.Agent.QXN Trojan is linked with these kinds of dangerous emails, claiming to come from Canada Post, and using the canadapost.ca URL for its emails and links. ESG security researchers strongly advise being extra careful in this holiday season and to watch out for these kinds of fraudulent emails containing malware such as the Win32/TrojanDownloader.Agent.QXN Trojan. Do not be blinded by the excitement surrounding the holiday season; ESG security researchers expect a whole family of these kinds of dangerous emails corresponding to the major courier chains such as DHL, UPS, and FedEx.
Table of Contents
An Overview of the Win32/TrojanDownloader.Agent.QXN Trojan’s Scam Email
The layout of the scam email associated with the Win32/TrojanDownloader.Agent.QXN Trojan is quite professional. ESG security researchers consider it is likely that the images and text used in these emails were, in fact, copied from legitimate Canada Post emails. The criminals behind this online scam have been quite clever in including two links within this dangerous email. The first will actually take you to the Canada Post's website and to a form where you arrange a new delivery. However, the second email masks its IP address and will actually take the victim to a file hosted on a server located in Houston Texas. You can be sure that the file associated with this fraudulent email is not really associated with Canada post. Rather, the file is in .pif format and is deceptively named in order to appear to be a tracking number (by using the prefix "trk" followed by random characters). The fact that this file is in .pif format should set off alarms in most experienced computer users, and is certainly quite alarming to PC security researchers. The .pif extension is associated with a program information file which is used to run a program whenever it is opened. In this case, this file will attempt to run the Win32/TrojanDownloader.Agent.QXN Trojan, a dangerous malware infection which is designed to contact a remote server and download dangerous malware onto your computer system.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Trj/CI.A |
| AVG | Generic26.RHX |
| Fortinet | W32/Agent.QXN!tr.dldr |
| Ikarus | Trojan.SuspectCRC |
| AhnLab-V3 | Downloader/Win32.Deliver |
| AntiVir | TR/Offend.kdv.459967 |
| DrWeb | Trojan.DownLoader5.17279 |
| Comodo | UnclassifiedMalware |
| Sophos | Troj/FakeAV-EWH |
| BitDefender | Trojan.Generic.KDV.459967 |
| Avast | Win32:Downloader-LSC [Trj] |
| Symantec | Trojan.Gen |
| NOD32 | Win32/TrojanDownloader.Agent.QXN |
| K7AntiVirus | Riskware |
| McAfee | Artemis!7AD1DF533141 |
SpyHunter Detects & Remove Win32/TrojanDownloader.Agent.QXN
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | setup_406.exe | 7225bdcfd7afab35640ed22d17292aac | 2 |
| 2. | 811eff71008e7ee1.exe | 7ad1df533141d3dcafee7008b267a53c | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.