Win32/Olmasco.R
ESG PC security researchers have issued a warning concerning the TDL4 rootkit, one of the most dangerous and complicated malware threats in recent years. The TDL4 rootkit has been characterized by the fact that its creators have constantly improved TDL4 rootkit, always staying one step ahead of PC security experts from all around the world. Win32/Olmasco.R is how the newest version of the TDL4 rootkit is detected. In the most recent versions of Win32/Olmasco.R and this rootkit, its creators have managed to innovate ways to circumvent the most popular anti-virus applications. These new versions are able to create an undetectable partition on the infected computer system's hard drive. All the malware on this invisible compartment can be executed before the Windows Operating System launches. Traditional anti-malware programs cannot detect Win32/Olmasco.R and the TDL4 rootkit, because they are not designed to detect and scan this invisible partition that the TDL4 rootkit creates. To remove malware such as Win32/Olmasco.R, a specialized tool is needed, usually an anti-rootkit utility. The newest versions of this dangerous threat have improved the various ways in which it infiltrates a computer system, as well as the way it can conceal its presence and the presence of other malware threats on the same infected computer.
According to ESG malware analysts, this latest version of the TDL4 rootkit was capable to infect millions of PC systems around the world. The levels of complexity shown by the Win32/Olmasco.R malware infection pose a significant problem for many malware analysts. The main reason that Win32/Olmasco.R is so dangerous is the fact that its creators update Win32/Olmasco.R constantly, to undo any advances made by PC security researchers. For example, only a month after Microsoft released an update to protect computers from the effects of the TDL4 rootkit, the criminals behind Win32/Olmasco.R managed to release a new version of their malware agent, which circumvented the recently instated Microsoft defenses, even mimicking them in order to attack more effectively. Win32/Olmasco.R can infect computer systems with 64 bit operating systems. This malware contaminant also contains several components that make remote access to the infected computer much more likely than before. According to ESG PC security researchers, the development of Win32/Olmasco.R has followed a rigorous schedule and evolution that is indicative of the work of high-level professionals rather than of amateur hackers. This is why it is important to make sure that your machine is protected with the latest security updates. New versions of Win32/Olmasco.R are released periodically to circumvent the newest security measures put into place.
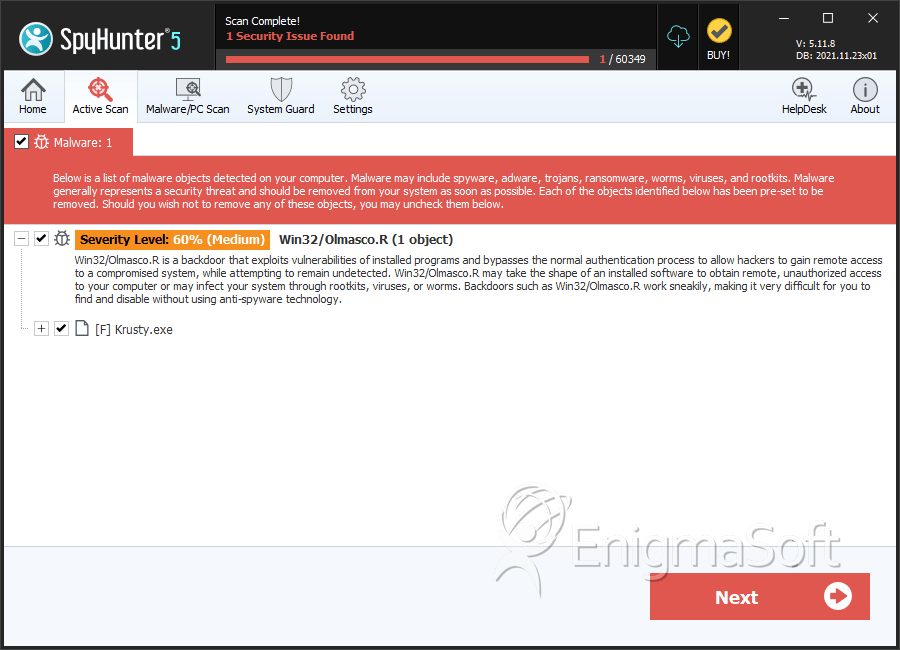
SpyHunter Detects & Remove Win32/Olmasco.R
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %temp%\MRT.exe | ||
| 2. | %temp%\%RANDOM CHARACTERS%.tmp | ||
| 3. | Krusty.exe | b8a7d3e95c64f088769c4f6399fb2a0d | 0 |
| 4. | Krusty.exe | 17f580bfc2c068916245585847596f99 | 0 |
| 5. | Krusty.exe | 58c6acd118b76fbb44deac79da5ed2ff | 0 |
| 6. | Krusty.exe | a7fc3257e7c9d3b4571f93b1788205ca | 0 |
| 7. | Krusty.exe | 7580fb0b136ab7b2cc167b65b7a98986 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.