Win32/Olmarik.AWO
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 340 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 18,145 |
| First Seen: | December 28, 2011 |
| Last Seen: | February 6, 2026 |
| OS(es) Affected: | Windows |
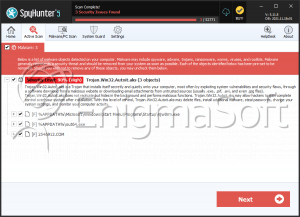
Win32/Olmarik.AWO is classified as a rootkit parasite that is difficult to remove even when using common antivirus programs. Win32/Olmarik.AWO is known to modify the Master Boot Record (MBR) where it could have access to make changes to an infected PC. These changes may include eliminating a PC's ability to operate normally or allow an administrator full control. Usually the removal of Win32/Olmarik.AWO can be successfully performed with the use of an updated antimalware program.
Table of Contents
Directories
Win32/Olmarik.AWO may create the following directory or directories:
| %ALLUSERSPROFILE%\wrnmscjqmost |
| %programfiles%\BNyTRLFWpkwbC |
| %programfiles%\HReuCWjxaimU2 |
| %programfiles%\JDdywVbgHqEU2 |
| %programfiles%\KnniQPNKaQpppomCylR |
| %programfiles%\KypIUqUeagMswzwjgbR |
| %programfiles%\MSTWKudwtFUn |
| %programfiles%\OHOmOJqmlvUn |
| %programfiles%\RMSgaodHU |
| %programfiles%\WctMgKafU |
| %programfiles%\ZPSkSQzenpoLC |
| %programfiles%\adlqtbpogebu2 |
| %programfiles%\aesxduqzszsdc |
| %programfiles%\anzkqvcqepxeehbyunr |
| %programfiles%\bDNsouxkWGUn |
| %programfiles%\bowhlfwwjwmu2 |
| %programfiles%\bvtiohlku |
| %programfiles%\cfvzwthqjvwu2 |
| %programfiles%\cfyimwhuqfzu2 |
| %programfiles%\cgsujuujawupc |
| %programfiles%\cowllrirafwxxhskzlr |
| %programfiles%\cpxepzdtdbvu2 |
| %programfiles%\dkolouibhibu2 |
| %programfiles%\dxebjoueczqinppdusr |
| %programfiles%\dzcscmyvfvfu2 |
| %programfiles%\eovzglkbu |
| %programfiles%\estnihpocszmc |
| %programfiles%\fnwihnsyeydoc |
| %programfiles%\gJqVIfoClyUn |
| %programfiles%\gawzsswzouou2 |
| %programfiles%\gdxxwfaefuknc |
| %programfiles%\grwtrdugu |
| %programfiles%\gtajkzwmfcqiwwrqior |
| %programfiles%\hkoodxutdxsu2 |
| %programfiles%\holteycvfzuu2 |
| %programfiles%\iyoovabuyjdu2 |
| %programfiles%\jXIFwscvdibGNTECIVR |
| %programfiles%\jvNFufxzjhUn |
| %programfiles%\kbkooyaoyyuu2 |
| %programfiles%\kjumgaftnyuu2 |
| %programfiles%\kmaslacxrpru2 |
| %programfiles%\lYEuBzwmGcUn |
| %programfiles%\ldfiykbtiklu2 |
| %programfiles%\lmyyddabxbeu2 |
| %programfiles%\motbbgfsrnku2 |
| %programfiles%\motvmfifvwau2 |
| %programfiles%\mpuoxlmroocu2 |
| %programfiles%\neuyocoegulaxndskxr |
| %programfiles%\ngwakbxtmuhu2 |
| %programfiles%\nlqycnznsemec |
| %programfiles%\nyhsxaisbbjec |
| %programfiles%\paqgivubjfuu2 |
| %programfiles%\poacokcqaubu2 |
| %programfiles%\qiuyuessgcigc |
| %programfiles%\qyrnywqkfhgiblceqxr |
| %programfiles%\rdrriohrsyau2 |
| %programfiles%\rlhwxtnparxu2 |
| %programfiles%\ruamtkavghnu2 |
| %programfiles%\sffdfvypjlqu2 |
| %programfiles%\teQFxlHihlUn |
| %programfiles%\upehecsrdhvu2 |
| %programfiles%\vgyhgswnvrpzepsvwqr |
| %programfiles%\vmwnjiqvhrlu2 |
| %programfiles%\vqsklubpuyxqssrpxxr |
| %programfiles%\wDsgizeLvyDU2 |
| %programfiles%\wrnmscjqmost |
| %programfiles%\xgvvxsckopbu2 |
| %programfiles%\xjgDFRUIUcUn |
| %programfiles%\yqxanpqzfryu2 |
| %programfiles%\yxufcojlbotu2 |
| %programfiles%\zqgnyzdragwu2 |
| %programfiles%\zsenbinduyiu2 |
| %temp%\1DZzC8rB |
| %temp%\DiwVUfrnBRxYQUgw |
| %temp%\FUAGPiNbWxDrEdwE |
| %temp%\LJaQOIYosxeelUdT |
| %temp%\dSEqUCVOPUvmFZjdC |
| %temp%\kLYpeNwXXVpPGGJu |
| %temp%\tuVAoTiSdBqSCmQlq |
| %temp%\wIluitOtFfikmcmF |
Analysis Report
General information
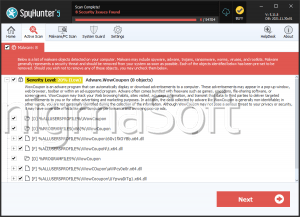
| Family Name: | Adware.Neoreklami |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
781463ccc21f6d2a9b24b1d3417e1dc0
SHA1:
a23036ce284bc8d3790b388c22e5a330952ff803
SHA256:
EEB87AD850682EA46A9E93E3B7567233C1483742ACF32E9D13CEADE9768EE122
File Size:
2.08 MB, 2082971 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- Installer Manifest
- nosig nsis
- No Version Info
- Nullsoft Installer
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsy549a.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |