W32.Virut.G
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
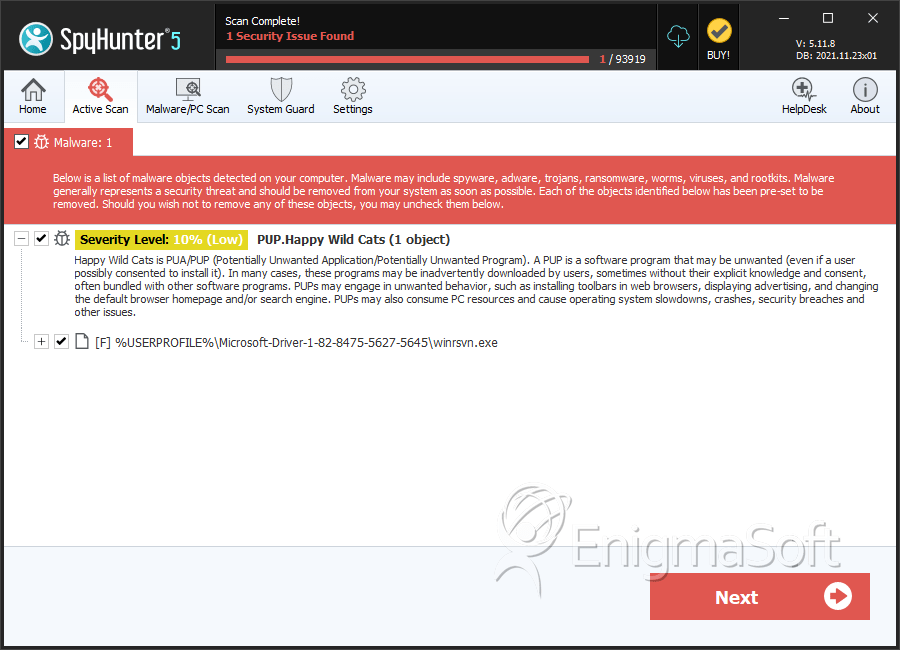
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 5,615 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 998 |
| First Seen: | January 5, 2012 |
| Last Seen: | September 20, 2023 |
| OS(es) Affected: | Windows |
W32.Virut.G is a family of viruses associated with various botnets. According to ESG security researchers, the W32.Virut.G family of viruses are designed to connect to IRC (Internet Relay Chat) through a backdoor that they establish on the infected computer system. Through this backdoor, W32.Virut.G can then download additional malware and install it onto the victim's computer. This malware will typically allow a criminal to control the infected computer by relaying automated commands through IRC. Like most viruses, W32.Virut.G is designed to corrupt files and spread on its own within an infected computer system. Like some worms, W32.Virut.G can jump from one computer to another by infecting files on a shared folder (giving W32.Virut.G the capacity to spread in a network) or by infecting files in an external memory device. Using this memory device on another computer would then cause it to become infected with the W32.Virut.G virus as well. The W32.Virut.G family of viruses has been mostly contained to infections in southeast Asia and Japan, with sporadic cases appearing in South Africa and Central Europe.
Table of Contents
An Overview of How W32.Virut.G Viruses Infect Your Computer System
W32.Virut.G is characterized by injecting itself into active file processes. It can infect executable files and open a backdoor into the infected computer system through port 80. This port is normally used for HTTP traffic. However, W32.Virut.G viruses use this port in order to establish an IRC connection with a remote server. The server with which the W32.Virut.G virus attempts to connect is located at the address proxim.ntkrnlpa.info. On this server, the W32.Virut.G virus will join the channel #virtu3 in order to receive commands from the criminals that control it. Through IRC, criminals can command the W32.Virut.G virus to download and execute malware located on other locations.
Symptoms of W32.Virut.G
According to ESG security researchers, a common way of detecting whether an executable file has been infected is by detecting any modifications in its size. Typically, a modified executable file will be bigger than usual, because it will contain the W32.Virut.G virus' harmful additions. Analyzing the infected computer's network traffic can also allow detection of W32.Virut.G. An infected computer will present DNS traffic to the proxim.ntkrnlpa.info server as well as IRC activity. Most of the time, W32.Virut.G infections are detected because of the symptoms presented by the malware that W32.Virut.G downloads and installs.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Suspicious file |
| AVG | Suspicion: unknown virus |
| Fortinet | W32/Buzus.GF!tr |
| Ikarus | Trojan.Win32.Menti |
| AhnLab-V3 | Trojan/Win32.Buzus |
| AntiVir | TR/Buzus.C.265 |
| DrWeb | BackDoor.Cybergate.1 |
| Comodo | TrojWare.Win32.Buzus.DAS |
| Sophos | W32/Scribble-B |
| BitDefender | Gen:Variant.Minggy.5 |
| Kaspersky | Virus.Win32.Virut.ce |
| Avast | Win32:Agent-AMTX [Trj] |
| Symantec | W32.Virut.CF |
| F-Prot | W32/CeeInject.R.gen!Eldorado |
| NOD32 | a variant of Win32/Injector.EZF |
SpyHunter Detects & Remove W32.Virut.G
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | .EveryplayCache.exe | ed5c3a1d648013d9ebb690456c01a655 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.