Virus.Small.R
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Prevx1 | Medium Risk Malware |
| BitDefender | Trojan.Agent.Small.D |
| AVG | Worm/AutoRun.M |
| Authentium | W32/Trojan5.HJY |
| Prevx1 | Generic.Malware |
| Panda | Bck/Agent.DLI |
| AVG | Worm/Generic.BVE |
| AntiVir | W32/Small.R |
| TrendMicro | WORM_SMALL.HYN |
| Symantec | W32.SillyDC |
| Sunbelt | Virus.Win32.Small.GeN |
| Sophos | W32/SillyFDC-H |
| Prevx1 | System Back Door |
| Panda | Trj/Agent.FQZ |
| NOD32 | Win32/Small.R |
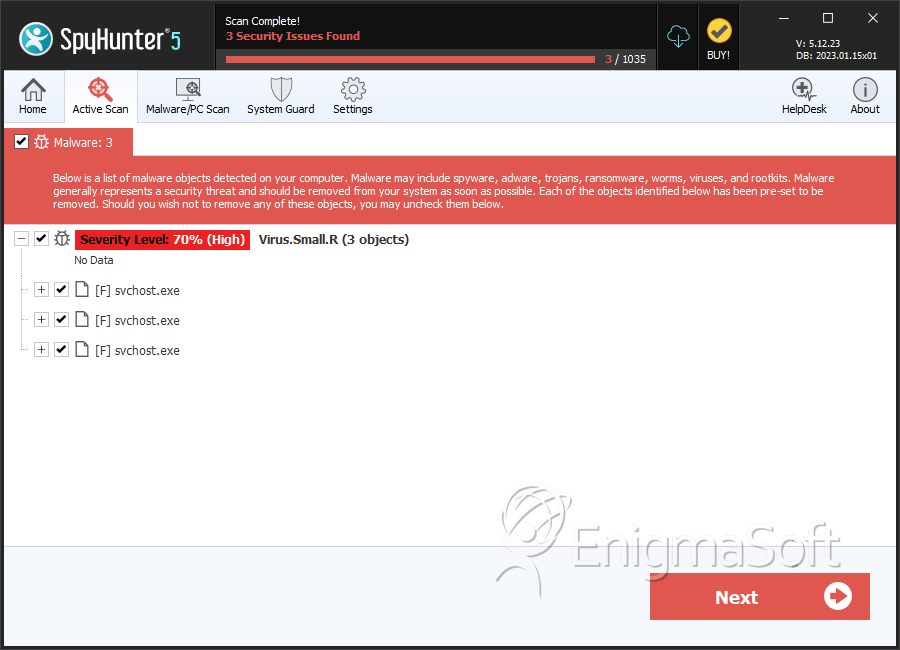
SpyHunter Detects & Remove Virus.Small.R
File System Details
Virus.Small.R may create the following file(s):
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svchost.exe | a0ce65fc2369cf8aaa67556f992377d1 | 0 |
Analysis Report
General information
| Family Name: | Trojan.Downloader.Small.R |
|---|---|
| Packers: | UPX |
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
32a31758d67926dcb8520662391ceab2
SHA1:
50bd378a15d215b54ac9dd4f89cacf6dd454512d
SHA256:
6E91886C597DA1069DBA2E56356A9CEAFFF845E30AC28EBB9B30515455AE3F6A
File Size:
3.62 KB, 3616 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File has been packed
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- No Version Info
- packed
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 14 |
|---|---|
| Potentially Malicious Blocks: | 7 |
| Whitelisted Blocks: | 7 |
| Unknown Blocks: | 0 |
Visual Map
0
0
0
0
0
x
x
x
x
x
x
x
0
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Downloader.Small.R
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\windows\syswow64\init32m.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |

