VECT 2.0 Ransomware
The cybercriminal operation known as VECT 2.0 presents itself as ransomware, yet technical analysis shows behavior far closer to a data wiper. A severe flaw in its encryption implementation across Windows, Linux, and ESXi variants makes file recovery impossible, even for the operators behind the attacks.
For files larger than 131 KB, which includes most enterprise-critical data, the malware does not provide recoverable encryption. Instead, it permanently destroys the data needed for restoration. As a result, ransom payment offers no realistic path to recovery.
In any VECT 2.0 incident, negotiation should not be considered a remediation strategy. There is no functional decryptor to deliver because the information required to build one is eliminated during execution. Defensive priorities should center on offline backups, validated recovery plans, rapid containment, and business resilience.
Table of Contents
A Growing RaaS Operation with Criminal Partnerships
VECT originally launched as a Ransomware-as-a-Service (RaaS) program in December 2025 and has since rebranded as VECT 2.0. Its dark web portal advertises the model 'Exfiltration / Encryption / Extortion,' signaling a triple-extortion approach.
New affiliates are reportedly charged a $250 Monero (XMR) entry fee. However, applicants from Commonwealth of Independent States (CIS) countries are exempt, suggesting targeted recruitment from that region.
The group has also formed partnerships with BreachForums and the TeamPCP hacking collective. This cooperation appears designed to simplify ransomware operations, lower barriers for new affiliates, and weaponize previously stolen data for further attacks.
The combination of supply-chain credential theft, organized affiliate operations, and forum-based criminal mobilization reflects an increasingly industrialized ransomware ecosystem.
Victim Count Remains Low Despite Bold Claims
Despite aggressive branding, VECT 2.0's leak site reportedly lists only two victims, both allegedly compromised through TeamPCP-related supply-chain attacks.
The group initially claimed to use ChaCha20-Poly1305 AEAD, a stronger authenticated encryption method. However, technical review found use of a weaker unauthenticated cipher lacking integrity protection, raising serious doubts about both capability and credibility.
The Encryption Failure That Destroys Data
The malware's most critical flaw lies in how it processes files larger than 131,072 bytes. Instead of securely encrypting recoverable data, it splits each large file into four chunks and encrypts each section using separate randomly generated 12-byte nonces.
Only the final nonce is stored with the encrypted file. The first three nonces, required to decrypt the majority of the file, are generated, used once, and discarded permanently. They are not saved locally, written to the registry, or sent to the operator.
Because the ChaCha20-IETF method requires both the correct 32-byte key and the matching nonce for decryption, the first three quarters of each affected file become unrecoverable. This means VECT 2.0 functions operationally as a destructive wiper hidden behind ransomware messaging.
Windows Variant: Advanced Features, Weak Execution
The Windows version is the most feature-rich and targets:
- Local drives, removable media, and accessible network storage
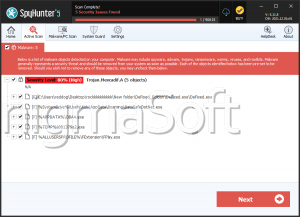
- 44 security and debugging tools through anti-analysis checks
- Safe Mode persistence mechanisms
- Remote execution script templates for lateral movement
When launched with --force-safemode, the malware configures the next reboot into Windows Safe Mode and adds its executable path to the Windows Registry so it automatically runs after restart in a reduced-security environment.
Interestingly, although the Windows variant contains environment-detection and evasion mechanisms, those routines are reportedly never called. This may allow defenders to analyze samples without triggering stealth responses.
Linux and ESXi Variants Expand the Threat Surface
The ESXi version performs geofencing and anti-debugging checks before starting encryption. It also attempts lateral movement through SSH. The Linux variant shares the same codebase as the ESXi sample but includes fewer capabilities.
This cross-platform support gives VECT 2.0 broad targeting potential against enterprise environments, especially those relying on virtualization and mixed operating systems.
Unusual CIS Geofencing Raises Questions
Before encrypting systems, the malware checks whether it is running in a CIS country. If so, execution stops. Notably, Ukraine is reportedly still included in these exclusions, an uncommon behavior since many ransomware groups removed Ukraine from CIS exemption lists after 2022.
Two likely explanations have been proposed:
- The malware may have been partially generated using AI models trained on outdated geopolitical data
- The developers may have reused an older ransomware codebase without updating regional logic
Signs of Inexperienced Operators
Although VECT 2.0 markets itself as a polished multi-platform threat with affiliate recruitment, supply-chain partnerships, and professional branding, the technical execution tells a different story.
Security assessment suggests the operators are more likely novice threat actors than seasoned ransomware developers. The possibility that portions of the malware were produced or assisted by AI-generated code cannot be ruled out.
Executive Security Assessment
VECT 2.0 demonstrates how dangerous-looking ransomware can still be technically flawed. Its infrastructure, partnerships, and branding create the image of a serious criminal enterprise, but the encryption design failure undermines the extortion model entirely.
For defenders, the lesson is clear: focus on resilience, backups, segmentation, and rapid incident response. In a VECT 2.0 attack, payment does not buy recovery, it only follows destruction.