Troj/JSRedir-H
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
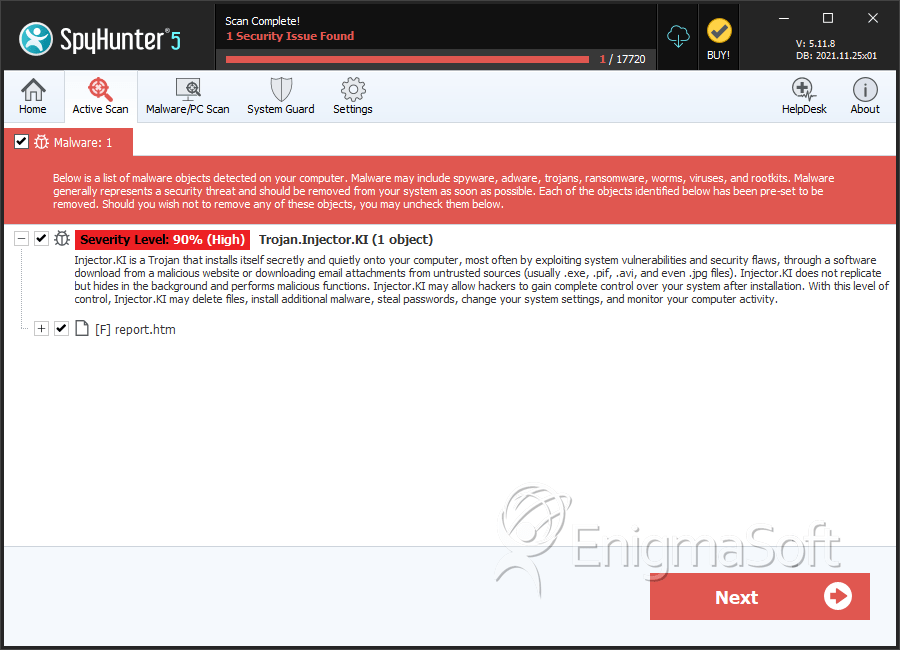
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 19,748 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 26 |
| First Seen: | July 2, 2012 |
| Last Seen: | August 22, 2025 |
| OS(es) Affected: | Windows |
Troj/JSRedir-H is very similar to numerous other malicious JavaScript Trojans designed to direct computer users to dangerous websites containing phishing scams or malware. Troj/JSRedir-H in particular will lead computer users to a website containing the BlackHole Exploit Kit, a dangerous hacking tool that will automatically try to install malware on your computer by trying to exploit numerous known vulnerabilities simultaneously. Troj/JSRedir-H is distributed through spam email messages which can be changed in order to carry out different kinds of social engineering scams. Troj/JSRedir-H is currently sent out in spam email messages claiming to have been sent by ADP (a company that is associated with payroll services). Clicking on a malicious embedded link will lead the victim to a dangerous website which will try to install malware on your computer system.
The email message containing the Troj/JSRedir-H Trojan is designed to be as convincing as possible, containing a spoofed email address, the ADP official logo, and official-sounding language. This email message will claim that it contains a link that leads to an essential security update. However, computer users that have clicked on this link have reported that this link leads to Troj/JSRedir-H, which in turn will force your web browser to download other malware from a dangerous website containing the BlackHole Exploit Kit. The final payload of Troj/JSRedir-H is detected as Troj/Dloadr-DPB, a dangerous Trojan downloader that can create a backdoor into the infected computer system as well as connect to a remote server to download and install numerous different malware threats.
Table of Contents
Do Not Let Troj/JSRedir-H Begin a Multi-Component Malware Cascade
These kinds of attacks that seem to cascade by involving numerous steps can be more difficult to control since there is a certain redundancy in the system that makes PC security analysts' work more difficult. The main way of avoiding these kinds of attacks is ensuring that Troj/JSRedir-H doesn't have a chance to activate in the first place. To do this, ESG security researchers strongly advise against clicking on the original link in the email message associated with Troj/JSRedir-H. In fact, it is important never to click on embedded links or open attached files contained in unsolicited email messages, even if the messages themselves seem to come from a reputable source. You can also prevent Troj/JSRedir-H's message from landing in your inbox in the first place by ensuring that you are using a reliable spam filter and that its setting are set at the maximum security.
SpyHunter Detects & Remove Troj/JSRedir-H
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | report.htm | 02ce72bfbefe5ba8866d4e87bb9435fd | 0 |
Analysis Report
General information
| Family Name: | Trojan.Injector.KI |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
a7a20f7a94b89c466ddb68126aec7d7f
SHA1:
53697617c1d369008f1235cd977d27eab6bb0bd1
SHA256:
6F5A5FF7C1C80D3D2800C4BC21D66328730FFA461BF9582F8B871A748F55E5EA
File Size:
9.10 MB, 9095680 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 1.8.0.0 |
| Company Name | Perfect-Privacy |
| File Description | Perfect Privacy SSH Manager |
| File Version | 1.8.0 |
| Internal Name | SSHManager.exe |
| Legal Copyright | Copyright (c) 2015, Perfect-Privacy.com |
| Original Filename | SSHManager.exe |
| Product Name | Perfect Privacy SSH Manager |
| Product Version | 1.8.0 |
File Traits
- HighEntropy
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,355 |
|---|---|
| Potentially Malicious Blocks: | 4 |
| Whitelisted Blocks: | 2,351 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- FareIt.LA
- Injector.DFF
- Injector.FHBA
- Injector.KI
- Injector.KKF
Show More
- Injector.KS

