Troj/JavaBz-IA
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
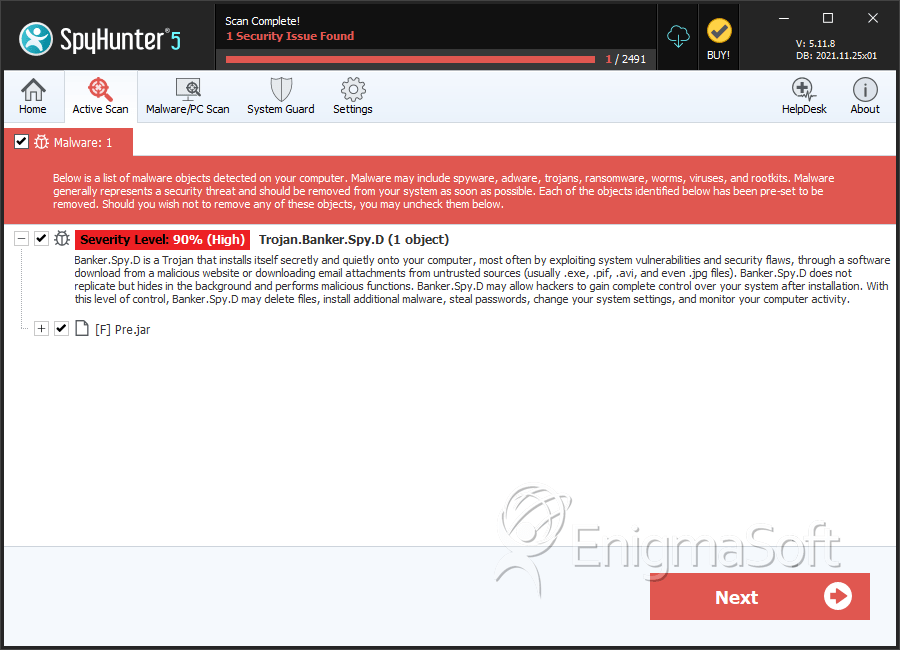
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 1 |
| First Seen: | August 30, 2012 |
| Last Seen: | April 14, 2020 |
| OS(es) Affected: | Windows |
Troj/JavaBz-IA is a Trojan component contained in the BlackHole Exploit Kit that is designed to take advantage of a recently-discovered vulnerability in Java 7. This zero-day exploit allows criminals to execute damaging code on the infected computer. The main goal of any attack involving the Troj/JavaBz-IA is to install a backdoor on the victim's computer. Using this backdoor, criminals may use the infected computer from a remote location, stealing information and installing other threats on the compromised computer. Since Troj/JavaBz-IA is part of a large scale attack that exploits Java vulnerabilities, downgrading or disabling Java is the best thing you can do to protect your computer. ESG malware analysts also advise updating your security software so that it will detect and remove this family of Java-based threats.
Table of Contents
The Relationship Between Troj/JavaBz-IA and the CVE 2012-1723 Java Vulnerability
Only a few hours after the zero-day vulnerability in Java 7 was disclosed to the public, PC security researchers started to detect the Troj/JavaBz-IA component in the infamous Black Hole Exploit Kit. This threat has been used for a couple of years to attack computers on all fronts, taking advantage of numerous known vulnerabilities such as CVE 2012-1723, another Java vulnerability that may be used to attack outdated versions of this platform.
Mac OS X Computers are not Safe from Troj/JavaBz-IA
The fact that Troj/JavaBz-IA is part of an attack that exploits vulnerabilities in Java 7 means that Mac OS X computers are vulnerable to infections involving this attacker. However, the default Java version distributed by Apple is Java 6. This means that, unless the computer user has actively upgraded to Java 7 directly from Oracle (Java's developer,) then that computer is not vulnerable to Troj/JavaBz-IA. As of the writing of this report, Mac OS X computers may be compromised with Troj/JavaBz-IA if they are using Java 7. However, it seems that criminals are delivering Windows-specific threats to Mac OS X computers. It is likely that this may change soon, since previous Java-based attacks exploit the cross-platform nature of Java by including a component that detects the victim's operating system and installs a version of the back door specific to that computer. To protect your computer from a Troj/JavaBz-IA, security researchers advise all computer users to downgrade their version of Java or to disable Java completely unless necessary.
SpyHunter Detects & Remove Troj/JavaBz-IA
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Pre.jar | 0cbc25ade65bcd7a28dd8ac62ea20186 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.