Troj/Inject-VI
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
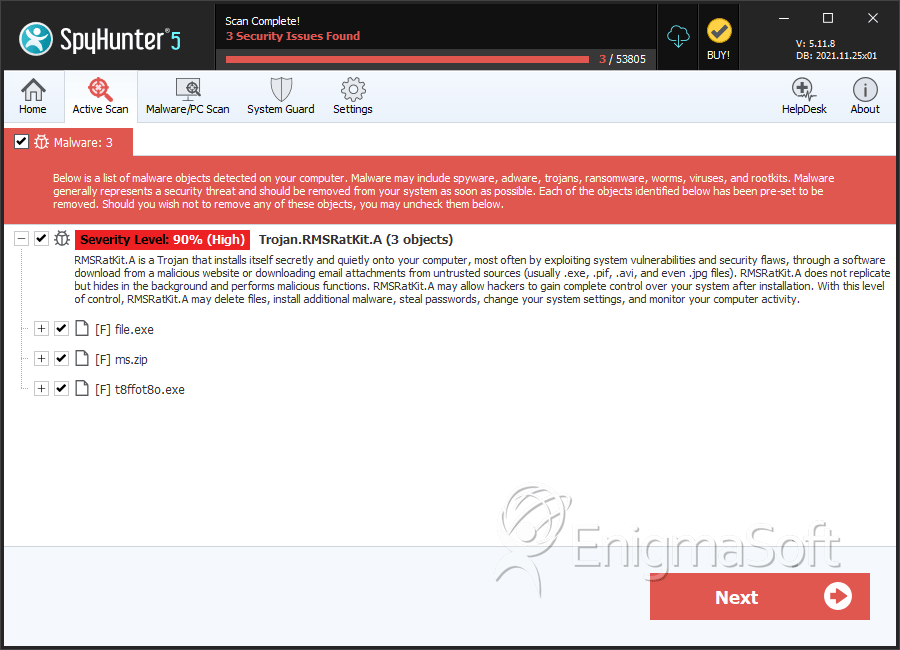
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 15 |
| First Seen: | May 31, 2012 |
| Last Seen: | March 15, 2023 |
| OS(es) Affected: | Windows |
An email scam, detected as Troj/Inject-VI, attempts to infect computers with malware from the BredoZP family. These kinds of Trojans are often distributed through malicious email campaigns, with Troj/Inject-VI being one of the latest variations on this theme. While previous methods for distributing BredoZP Trojans include fake emails from courier services, airlines and the IRS, the Troj/Inject-VI scam involves fake 'booking confirmations' from spoofed hotel email addresses. As always, ESG security researchers strongly advise against opening unsolicited email attachments; even if they are written convincingly and include logos, email addresses or link associated with a legitimate company.
The Troj/Inject-VI email is disguised as a booking confirmation from a popular web page used for these kinds of transactions, booking.com. Curious computer users may be tempted to open the email attachment, infecting their computer system with a dangerous malware invader. The Troj/Inject-VI email message will typically have some variation on the following subject line: [Fwd: Hotel booking confirmation XXXXXXXXX] with a random fake booking number. This email message will have an attached ZIP file with some variation on the following name: Hotel_Reservation_Booking_Com_XXXXXXID.zip, using the random 'booking number' in the email subject and body. While Troj/Inject-VI's message body is convincingly written and even contains 'contact information' and a confirmation telephone number, this is intended to increase the chances of an unsuspecting computer user opening its malicious email attachment.
Table of Contents
What the Troj/Inject-VI Email is Trying to Install on Your Computer System
The BredoZP family of Trojans has been active since 2010. While the basic malware infection has not changed much over the years, there are new fake email messages designed to distribute this dangerous Trojan. Generally, BredoZP is a somewhat generic label for Trojans distributed through email scams like the Troj/Inject-VI email scam. Because of this, the result of a Troj/Inject-VI malicious email can vary from case to case. In general, most malware associated with Troj/Inject-VI will install a backdoor on the victim's computer system, connect to a remote server to download and install other malware, and make changes to the infected computer systems in order to make that computer system more vulnerable to other malware attacks. Because of this, if you have come into contact with the Troj/Inject-VI email scam, ESG security analysts strongly advise scanning your computer system with a reliable, fully-updated anti-malware program.
SpyHunter Detects & Remove Troj/Inject-VI
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | bbb24047344147f012a820bcc204aadc | 0 |
| 2. | file.exe | 5343593f082cd71a29b1510e12e3cb0d | 0 |
| 3. | ms.zip | df8bce35c725968f9ed5ffb8ba9493c0 | 0 |
| 4. | t8ffot8o.exe | 9b4e4dc586f982ef1b2d14ce17d32722 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.