TROJ_DROPPR.JET
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 2 |
| First Seen: | May 14, 2012 |
| Last Seen: | February 18, 2022 |
| OS(es) Affected: | Windows |
TROJ_DROPPR.JET has been detected in a malicious email attachment and used in an attempt by criminals to exploit the death of Beastie Boy Adam Yuach as a way of distributing malware. This file claims to contain information about this recently deceased celebrity. However, when the computer user opens this file it will run TROJ_DROPPR.JET, which will install a second Trojan designed to connect to a remote server in order to install other malware on the victim's computer system.
These kinds of malicious email messages are quite common and will often accompany important breaking news events, celebrity or political deaths, and popular releases (such as new iPhone or iPad releases). To avoid becoming a victim of TROJ_DROPPR.JET, ESG security analysts strongly advise against opening these kinds of email messages, even if they appear to be harmless text files. Using exploits, criminals can use files in PDF, DOC, or other common formats to execute dangerous Trojans. Indubitably, it is also crucial to have a strong spam filter and a reliable real-time malware scanner.
Table of Contents
How Criminals Exploit Tragedies to Install Malware Like TROJ_DROPPR.JET
The TROJ_DROPPR.JET email claims to have been sent by the International Campaign for Tibet. To further enhance this illusion, this malicious email includes this organizations logo as well as a photograph of the recently deceased Adam Yuach posing with the Dalai Lama. This email will contain a seemingly harmless file in DOC format supposedly containing more news on Adam Yuach's death. This kind of attack is quite common. Even just in recent months PC security researchers have observed similar malicious email attacks exploiting the deaths of Amy Winehouse, Whitney Houston, Muammar Ghadaffi, and Steve Jobs.
How TROJ_DROPPR.JET Carries Out Its Attack
TROJ_DROPPR.JET is a Trojan dropper, which means that its payload is basically limited to installing another malware threat. ESG security analysts have observed that TROJ_DROPPR.JET can be used to install a variety of other threats. In the case of the Adam Yuach-related email attack, TROJ_DROPPR.JET dropper installs the TROJ_SWYSYN.SME Trojan. This Trojan has the ability to connect to a remote server, establish a backdoor on the infected computer system, allow criminals to gain access to your confidential data, and download and install other malware from a remote server.
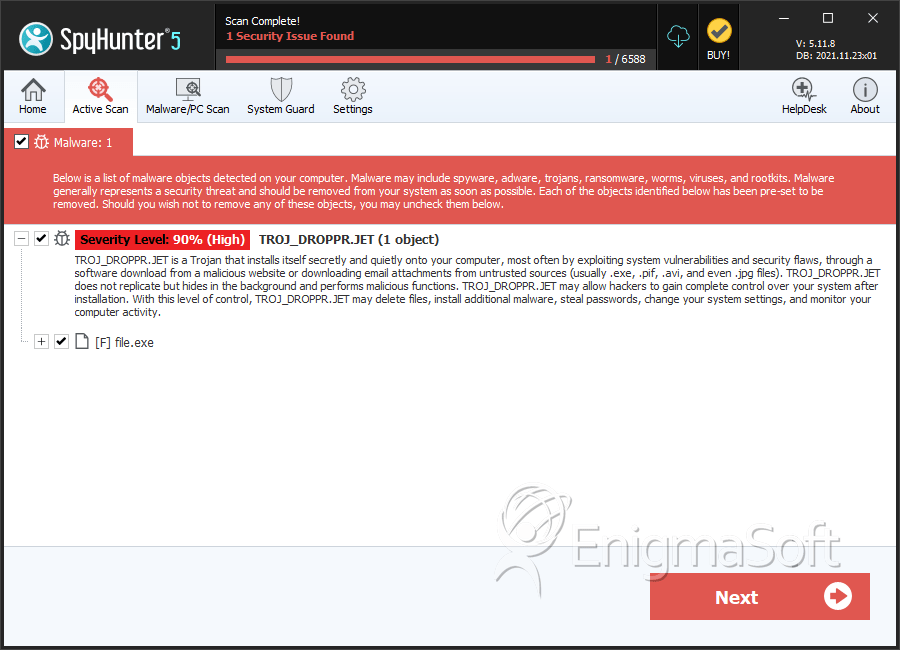
SpyHunter Detects & Remove TROJ_DROPPR.JET
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | a6e3fbea1a839cb612a15396d6c35f98 | 1 |
| 2. | %System%\winlogin.exe |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.