Troj/BckR2D2-A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
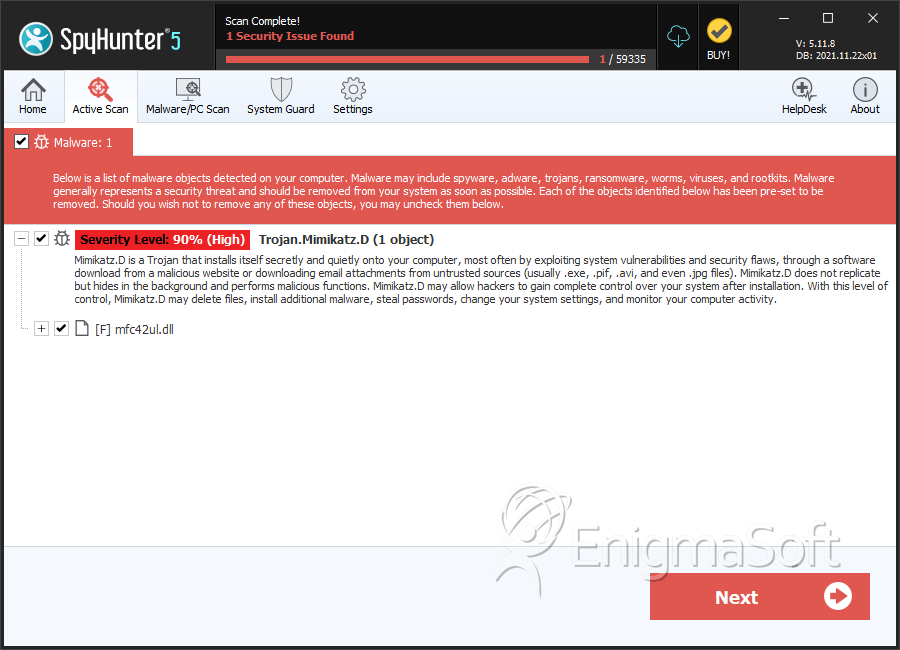
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 90 % (High) |
| Infected Computers: | 187 |
| First Seen: | October 11, 2011 |
| Last Seen: | June 17, 2022 |
| OS(es) Affected: | Windows |
The Troj/BckR2D2-A Trojan takes Troj/BckR2D2-A's name from the Star Wars universe, due to some characters in Troj/BckR2D2-A's code (C3PO-r2d2-POE) which any Star Wars fan will recognize. This dangerous Trojan has dangerous capabilities that, apart from spying on a computer's activity, can also download and install other malware, as well as monitoring Skype calls. It seems that the German police has been using the Troj/BckR2D2-A Trojan, in order to spy on specific targets. While this may be conform to current laws and rulings in regards to wiretaps and spying on online activity and Internet calls, it seems that some aspects of the Troj/BckR2D2-A Trojan may be in violation of certain regulations designed to protect citizens' rights. There have also been some claims that this Trojan has been abused by some elements of German law enforcement, particularly a well-publicized case involving the German customs authority.
Table of Contents
What the Troj/BckR2D2-A Trojan Does Apart from Spying on Internet Conversations
The Troj/BckR2D2-A Trojan does much more than simply spying on Skype phone calls and video conversations. The Troj/BckR2D2-A Trojan can also spy on popular Instant Messaging clients and keep track of all keystrokes on the infected computer system, and of keystrokes entered into the most popular Internet browsers. Like some of the most dangerous malware, Troj/BckR2D2-A Trojan can also connect to a remote server, download additional malware and updates and record and transmit screenshots taken from the infected computer system. Imagine if criminals take control of the Troj/BckR2D2-A Trojan, it would be catastrophic. This is why, according to ESG PC security researchers, it is important to use anti-malware programs that have been updated to include the Troj/BckR2D2-A Trojan in its malware database. While this malware infection may have been used to fight criminals, there is no reason why those very same criminals could not use the Troj/BckR2D2-A Trojan themselves, in order to steal your personal information.
How a Computer System Typically Becomes Infected with the Troj/BckR2D2-A Trojan
The Troj/BckR2D2-A Trojan will typically enter a computer system through a malicious email attachment or through an attack website. Since the Troj/BckR2D2-A Trojan is thought to be used by law enforcement authorities, ESG security researchers consider it likely that the Troj/BckR2D2-A Trojan could simply be directly installed onto the target's computer system. If the computer system is using the Windows operating system, then the Troj/BckR2D2-A Trojan can probably be installed and operate fully.
SpyHunter Detects & Remove Troj/BckR2D2-A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. |
C:\Documents and Settings\ |
||
| 2. | C:\WINDOWS\system32\winsys32.sys | ||
| 3. | C:\WINDOWS\system32\mfc42ul.dll | ||
| 4. | mfc42ul.dll | 36cf8434b89e5afa2ee5b4ce648dce29 | 0 |
| 5. | mfc42ul.dll | 97eb2a867184054e91952c25c77a5b5e | 0 |
| 6. | mfc42ul.dll | 24b5739c3d49960b18302a2bdaec50d5 | 0 |
| 7. | mfc42ul.dll | 8211d3a9ac88be7a9f1fead92d679ca1 | 0 |
| 8. | mfc42ul.dll | dbca4c888ad699fed8f993545d877fe3 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.