Troj/BatDel-B
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 5,505 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 2,745 |
| First Seen: | December 18, 2012 |
| Last Seen: | September 14, 2023 |
| OS(es) Affected: | Windows |
Troj/BatDel-B is a malware infection that is used to delete data from an infected hard drive. ESG security researchers warn computer users that Troj/BatDel-B has been used in targeted attacks against computers located in Iran. Troj/BatDel-B is not particularly sophisticated, but Troj/BatDel-B can be highly destructive. Troj/BatDel-B is distributed in a malicious compressed archive named GrooveMonitor.exe, a self extracting RAR file that drops three executable files, jucheck.exe, juboot.exe, and sleep.exe. These make the infected computer run Troj/BatDel-B automatically upon start-up. Troj/BatDel-B will check the current date and then delete all the contents of the infected computer's D: through I: drives and all contents of the computer system's desktop. According to Troj/BatDel-B's code, the attacks will occur on the following dates:
- 10-December-2012 to 12-December-2012
- 21-January-2013 to 23-January-2013
- 06-May-2013 to 08-May-2013
- 22-July-2013 to 24-July-2013
- 11-November-2013 to 13-November-2013
- 3-February-2014 to 5-February-2014
- 5-May-2014 to 7-May-2014
- 11-August-2014 to 13-August-2014
- 2-February-2015 to 4-February-2015
In its list are also dates in November and October of 2012, meaning that it is likely that Troj/BatDel-B has been at work for at least two months. It is obvious that Troj/BatDel-B is highly rudimentary, especially when compared to the many high-profile malware attacks that have hit the region in recent months, such as Flame, Duqu, and the infamous Stuxnet worm. Is Troj/BatDel-B a state sponsored attack? The likely culprits being Israel and the United States, in this case. Due to the fact that the Iranian government is gathering attention to Troj/BatDel-B, it is just as likely that there is a hidden political motive to these kinds of accusations, especially due to the high degree of complexity from confirmed state sponsored attacks in the past when compared to Troj/BatDel-B.
Part of the danger of Troj/BatDel-B's simplicity is that Troj/BatDel-B may allow this malware infection to bypass some anti-virus programs. Troj/BatDel-B has one main task, to destroy data on the infected hard drive. Although a Trojan dropper has been identified that seems to be associated with the Troj/BatDel-B attack, Troj/BatDel-B can conceivably be distributed through a variety of tactics. Troj/BatDel-B attacks can come from phishing email messages, attack websites using exploit kits to install Troj/BatDel-B on the victm's computer or from infected removable memory devices. Since the Trojan dropper associated with Troj/BatDel-B is named GrooveMonitor.exe, it is possible that the social engineering distribution scheme associated with Troj/BatDel-B involves the use of a fake version of the Microsoft Office 2007 collaboration utility.
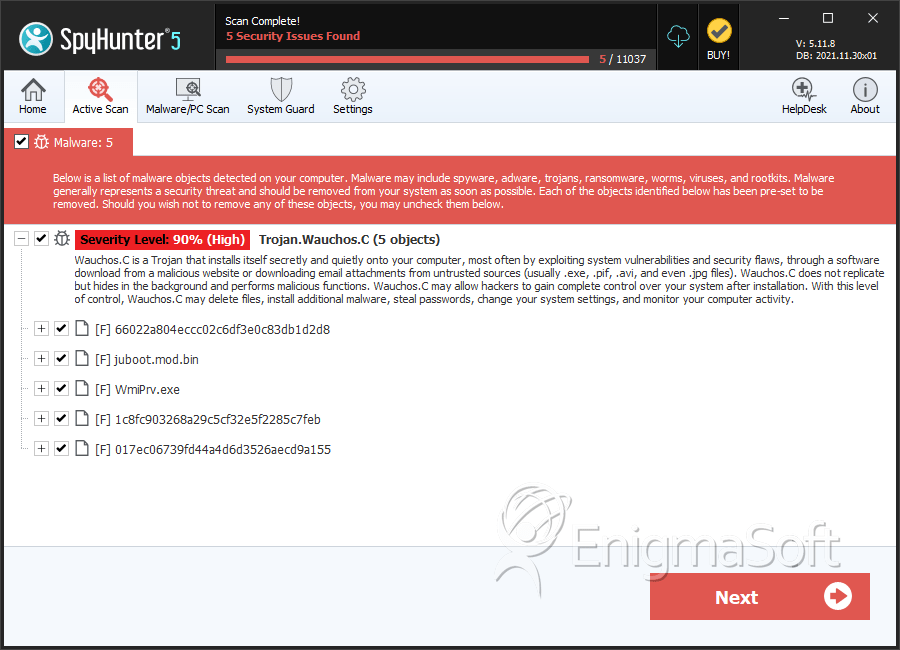
SpyHunter Detects & Remove Troj/BatDel-B
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | juboot.exe | ||
| 2. | jucheck.exe | ||
| 3. | GrooveMonitor.exe | ||
| 4. | Wmiprv.exe | ||
| 5. | 66022a804eccc02c6df3e0c83db1d2d8 | 66022a804eccc02c6df3e0c83db1d2d8 | 0 |
| 6. | juboot.mod.bin | 0c1161634d4f25e57a9e7bc560a1496d | 0 |
| 7. | WmiPrv.exe | b7117b5d8281acd56648c9d08fadf630 | 0 |
| 8. | 1c8fc903268a29c5cf32e5f2285c7feb | 1c8fc903268a29c5cf32e5f2285c7feb | 0 |
| 9. | 017ec06739fd44a4d6d3526aecd9a155 | 017ec06739fd44a4d6d3526aecd9a155 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.