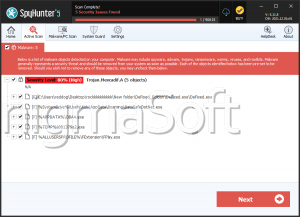
Trojan.Yoma.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 11,831 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 37 |
| First Seen: | March 13, 2025 |
| Last Seen: | May 2, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Yoma.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
576f75ea0307528b8f6be0ab1b74c8bd
SHA1:
2169bc0a7f784f98b1015b488c2f8d5bf46c91b0
SHA256:
93753E319EA88830CD30432871289B64166433E7F85D9503204657ED1BBB57FC
File Size:
4.60 MB, 4597577 bytes
|
|
MD5:
b69a658ff5c627a1c39f4bef62fa96c0
SHA1:
0fb00f4ec1b310e764aa9f2b7675ac99959382be
SHA256:
D1729DB74C077BBA916F0FD3D0D497A889C7A927D583B1090D082CEACC2ECFA4
File Size:
4.58 MB, 4584822 bytes
|
|
MD5:
a45438692631f41b81af4196c134179b
SHA1:
bbecdc573d6afeacb6a124c0ecd6eaad1ca8a563
SHA256:
345DCE41A6D6E6925D49F7485315550B6D154309C37C2119F5F61CB8BBF4F35C
File Size:
5.18 MB, 5180138 bytes
|
|
MD5:
8a23e360faa09dfb8ea1c89eeb18e12a
SHA1:
55f7beda0db7a2019a2403fa1ff8a5d4652a83fa
SHA256:
ADE7E505B425871F3887E3747D00B6A64E71ACD150740D756BCD7C90EA073D52
File Size:
4.60 MB, 4596074 bytes
|
|
MD5:
5c26d3cb87a7d0d62650797a82631385
SHA1:
b365a85be93f57c0daffd82bbdd481edd0b612aa
SHA256:
5DBEE6FC36F651E5F2A0501B705D2278EBFAB1B48A243741A45A25E9565D3E78
File Size:
5.18 MB, 5183777 bytes
|
Show More
|
MD5:
4c481c650fa73fccbad34b9afbb6f2de
SHA1:
8d97aa9d0536a6fdb23ac3045777d2f4bb1f2970
SHA256:
B10436B57D2AB3DC65E774C67B26B32886E8FE3FE2989FE7B38B85D8C9A660A1
File Size:
4.69 MB, 4694517 bytes
|
|
MD5:
c3443aa454255808a1b4a3024096049b
SHA1:
4dd05f4475a3caced3ac1090d915c57ede3eff82
SHA256:
40A2EF884CA539AF546A7FE7A4C5D2A9C05EED025CFD563329BDE86E60D44F86
File Size:
5.19 MB, 5187845 bytes
|
|
MD5:
8dbaae28676180ce9391c7e3ca5a37ba
SHA1:
fda285e7cc099ef258b5a2ebd20f19c1ec60382a
SHA256:
A42BA081E62B1BF8C324515171759A6EAF5C26CE6A4BC1BDD32E2CDE8425D266
File Size:
4.59 MB, 4591085 bytes
|
|
MD5:
0752ea62a5664af0630ca0b826c70938
SHA1:
879f1d008fe434fffb6ccb967ad4376fb408f10a
SHA256:
E2E4A6E3476F541F615A1952D4C21D8E0D518BF86831730F8224B794E8CADC65
File Size:
4.70 MB, 4703382 bytes
|
|
MD5:
25171bac01dd765d4dfd6e2545969d46
SHA1:
35e2a50a9e5dbea6de513e04808f55f498137479
SHA256:
9A2914C439AB1D5F9B04616C21F36FB11A0D14F8DAC48949E25ACAB7939BE1E6
File Size:
5.11 MB, 5109872 bytes
|
|
MD5:
952438da8d24e25961e9ba991104b01d
SHA1:
1e8c4023e905d058204d44eb1bca1b914e149ccd
SHA256:
6A2F221915025C70151BE0C9AB471EE9420DD7F8850BB4148098BA55CD01E541
File Size:
4.68 MB, 4677889 bytes
|
|
MD5:
e5f984198fcdb033ffa97252a04636d1
SHA1:
8563f245dcc6e4700789e76802da5eb9efcc921d
SHA256:
050051175A38641F9A138C9DA904B857E082AE374D9112F6740427414B21AFD7
File Size:
4.56 MB, 4556002 bytes
|
|
MD5:
1a2092b7d42f0f94ed1f2f2135fc2af8
SHA1:
0ed0707eba68178c8cf798176fd1aeb9e69be0d9
SHA256:
E236A6532A5B0879288732D8A9186AB92E7DA7A30E1015E02EBF78E74CAFA84B
File Size:
4.66 MB, 4663925 bytes
|
|
MD5:
59f7447a02a07317e6450cf92e996994
SHA1:
c2d7ff54896141fd1eabfccf0b162ed730cee151
SHA256:
A0F7E75BD9EAA07CD17523C618AA5B7FCBF2954B1054F57D70D9C99B1F4A8F1B
File Size:
4.59 MB, 4588104 bytes
|
|
MD5:
fc1e308627010decb6b78609fa22f484
SHA1:
5ecd11c326f2e9d309ae4b216502b4fbd3a8e3f0
SHA256:
B9FF3586BE37770B55F701EC76B9D8F41495D0FD0147C4FCE0AED8EC551F3AB6
File Size:
4.52 MB, 4522483 bytes
|
|
MD5:
e32a4ae456c035e87816cbdf5130fc1d
SHA1:
b551a50d323577bef2a771cea638c3f339bbf030
SHA256:
0968FD82F5C4FA306E694B0AD7295A8C45C85367222837977063E8710421CC1C
File Size:
4.59 MB, 4591553 bytes
|
|
MD5:
e2f021fe7e03ff0c1efe44d5f4b07fdf
SHA1:
976ae13cdcb4f2bd16dafda6953312623d9031d7
SHA256:
261D95A8829576CF3606C93F83FA8E873A3167B3F698789110A5BA6A0E786F40
File Size:
4.60 MB, 4596215 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | TENOKE |
| File Description | TENOKE |
| File Version | 1.0.2.0 |
| Internal Name | TENOKE |
| Legal Copyright | TENOKE |
| Original Filename | TENOKE |
| Product Name | TENOKE |
| Product Version | 1.0.2.0 |
File Traits
- big overlay
- HighEntropy
- imgui
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 7,993 |
|---|---|
| Potentially Malicious Blocks: | 271 |
| Whitelisted Blocks: | 7,722 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.AIBB
- Agent.BNDB
- Agent.FRFA
- Danabot.U
- Downloader.Agent.BND
Show More
- Downloader.Agent.FAB
- Emotet.GX
- Farfli.TD
- GameHack.HJ
- Kryptik.KABJ
- Marte.L
- OpenSUpdater.TD
- Rozena.FGB
- ShellcodeRunner.FN
- Spy.Agent.XD
- Trojan.Downloader.Gen.BP
- Trojan.Downloader.Gen.GT
- Yoma.A
- Zegost.CP
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|
| Other Suspicious |
|