Trojan.Yakes!Usf1NLb8Ipo
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
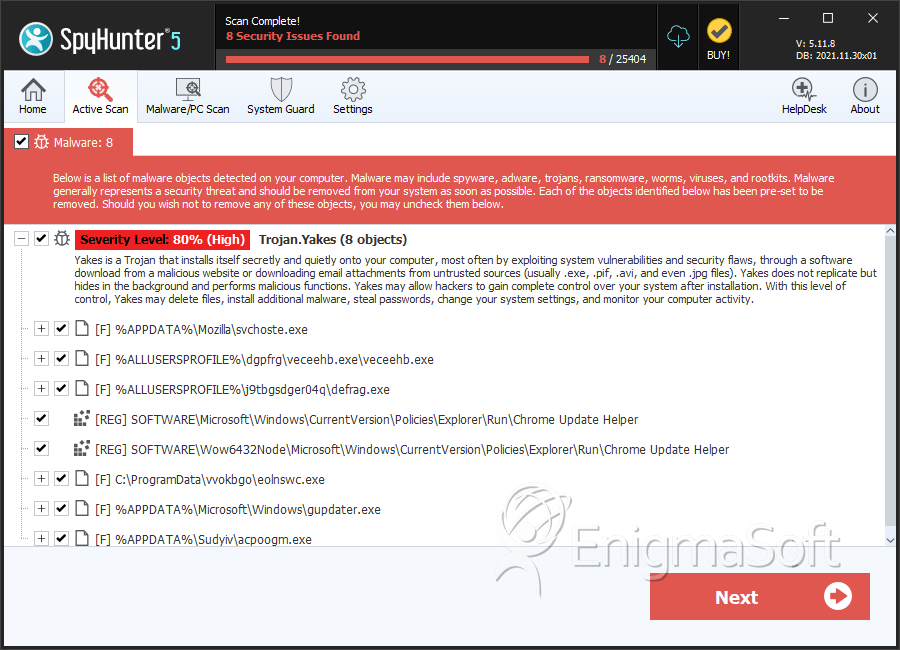
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,315 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 2,974 |
| First Seen: | June 18, 2011 |
| Last Seen: | July 24, 2023 |
| OS(es) Affected: | Windows |
Trojan.Yakes!Usf1NLb8Ipo is a variant of the Yakes trojan and deployed in spam emails as an attached file and on low-quality software centers as a helpful program. Trojan.Yakes!Usf1NLb8Ipo is known to place its executable file in the temp folder of Windows and to insert a registry key in order to auto-start with your OS. Security experts note that Trojan.Yakes!Usf1NLb8Ipo may redirect infected users to visit harmful online resources that might be used by hackers to exploit web browser vulnerabilities. The succesful installation of the Trojan.Yakes!Usf1NLb8Ipo can expose you to viruses, worms, keyloggers and other trojans. You should not think lightly of Trojan.Yakes!Usf1NLb8Ipo because attackers may use it to steal your banking and social media credentials, your files and passwords for your email clients. Computer users may want to consider installing a reputable anti-malware shield that can allow you to browse the Internet safely.
Table of Contents
SpyHunter Detects & Remove Trojan.Yakes!Usf1NLb8Ipo
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svchoste.exe | 1dd4c9cd29fc5ca667fcf272f0585dcb | 96 |
| 2. | svchoste.exe | 2718e9630267a97f51260d60cdddca97 | 49 |
| 3. | veceehb.exe | 22c03932747c80dce58b329b2df2cf84 | 49 |
| 4. | svchoste.exe | 8b2c6c021c28e8a6ec1e5ef6e25a3d6a | 45 |
| 5. | svchoste.exe | 2f0693a0d7949db5f0cc6fb3ecb9bef0 | 38 |
| 6. | svchoste.exe | e1f5d24c5511d578d16012ee2611482d | 38 |
| 7. | svchoste.exe | 017c6f38ac7f986aa6230309d25f45dd | 37 |
| 8. | svchoste.exe | abe1f6a73066c6ba7ea7e4e5127d36d2 | 29 |
| 9. | svchoste.exe | 5097db181aa44da81282e849d6e7fa79 | 26 |
| 10. | svchoste.exe | 40b925a588bb0e42ddc88288a8809a94 | 25 |
| 11. | svchoste.exe | b0510d4e7d8e66cb07ab5abbfdcbe4b6 | 25 |
| 12. | svchoste.exe | 907e06d8ee9e1105cc38796eade6bf39 | 24 |
| 13. | svchoste.exe | 19b831b5249861bce52fd0c6c04aa368 | 21 |
| 14. | svchoste.exe | 17597aecc8ca8ceb662691398164be1d | 21 |
| 15. | svchoste.exe | cde8f8407bdb7c405427829bd29c1dc1 | 19 |
| 16. | svchoste.exe | 79f8b040121ca8feb36e2152817e1d5c | 18 |
| 17. | svchoste.exe | 088aa397024543561dadf3d3869b9bb3 | 17 |
| 18. | svchoste.exe | 1ddb891f37b11fc6753e733da2aa15b4 | 14 |
| 19. | svchoste.exe | c0ac419f139068fb210f8fda8080b0d9 | 14 |
| 20. | svchoste.exe | f6d6b3089bd7c2cae0afff10a2c2176c | 13 |
| 21. | svchoste.exe | d49edd41c665531e7cfd298be5a30d57 | 12 |
| 22. | svchoste.exe | 31c59d7ead9c7107d68fd06b6ea46ae8 | 12 |
| 23. | svchoste.exe | 9e9d41bce6eedbe11f4b10992a08fde0 | 12 |
| 24. | eolnswc.exe | 502a1ce046e11ae3941f311f1b869157 | 10 |
| 25. | gupdater.exe | f669d799fc876b313e43de677fe97cf2 | 7 |
| 26. | d3dxxva2.exe | f858f8deb7725fc72574f29deb946951 | 4 |
| 27. | file.exe | 31aaa02ac947faf16b3313fddade437f | 0 |
| 28. | eee.exe | 66dad151e7419f6290172a574799284f | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.