Trojan.Weelsof.C
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 683 |
| First Seen: | July 20, 2012 |
| Last Seen: | February 26, 2021 |
| OS(es) Affected: | Windows |
Trojan.Weelsof.C is designed to infiltrate computers and to deliver malware. Trojan.Weelsof.C is closely associated with ransomware Trojans, specifically with the many variants of the so-called Ukash Virus. This family of malware is used to take computers hostage by blocking access to Windows. Ransomware associated with Trojan.Weelsof.C will display a threatening message claiming that the infected computer was involved in illegal activities. Posing as a message from the infected computer's country's law enforcement agency, malware associated with Trojan.Weelsof.C will try to convince victims to pay a hefty ransom through the Ukash or PaySafeCard money transfer service. If your computer is infected with Trojan.Weelsof.C, you should try a reliable anti-malware program to protect your computer and remove this threat.
There are several things that you should definitely avoid if your computer is infected with Trojan.Weelsof.C. Some of these include:
- You should never pay the ransom for any ransomware associated with Trojan.Weelsof.C. Although their threatening message claims that the infected computer will be unlocked if you pay the demanded ransom, you have absolutely no guarantee that the criminals will follow through on their word. It is also important to note that ransomware associated with Trojan.Weelsof.C is typically not difficult to remove, meaning that there is no need to risk paying the fake police fine.
- You should not confuse ransomware associated with Trojan.Weelsof.C with a real message from law enforcement. Real police organizations do not typically send out these kinds of messages in order to charge fines from computer offenders. Since Winlockers associated with Trojan.Weelsof.C will also accuse you of very serious crimes (such as trafficking with child pornography), it is laughable to consider that a fifty euro fine would be sufficient to resolve such a severe transgression.
- If you find signals that your computer has been exposed to Trojan.Weelsof.C, but you haven't lost access to your computer, ESG security researchers strongly admonish against accessing sensitive data or entering passwords for banking accounts or email accounts. Malware rarely attacks alone, and the Trojan.Weelsof.C infection may be accompanied with other Trojans that may steal sensitive data or spy on your activities.
Most of the time, the main difficulty in dealing with a Trojan.Weelsof.C-related infection is actually gaining access to the infected computer. Fortunately, most ransomware infections distributed with Trojan.Weelsof.C can easily be bypassed by booting up Windows from an alternate source (such as CD or a shared network drive).
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Generic30.ARFR |
| Fortinet | W32/Weelsof.AAC!tr |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Suspicious-DTR.K |
| AntiVir | TR/Weelsof.aac |
| Kaspersky | Trojan.Win32.Weelsof.aac |
| AVG | Generic32.BRPZ |
| Fortinet | W32/Weelsof.PHF!tr |
| AntiVir | TR/Weelsof.C.9 |
| Kaspersky | Trojan.Win32.Weelsof.phf |
| Symantec | Suspicious.Cloud |
| McAfee | Artemis!31CD61043694 |
| Fortinet | W32/Weelsof.XY!tr |
| AntiVir | TR/Weelsof.C.25 |
| F-Secure | Gen:Variant.Symmi.6534 |
| Kaspersky | Trojan.Win32.Weelsof.xy |
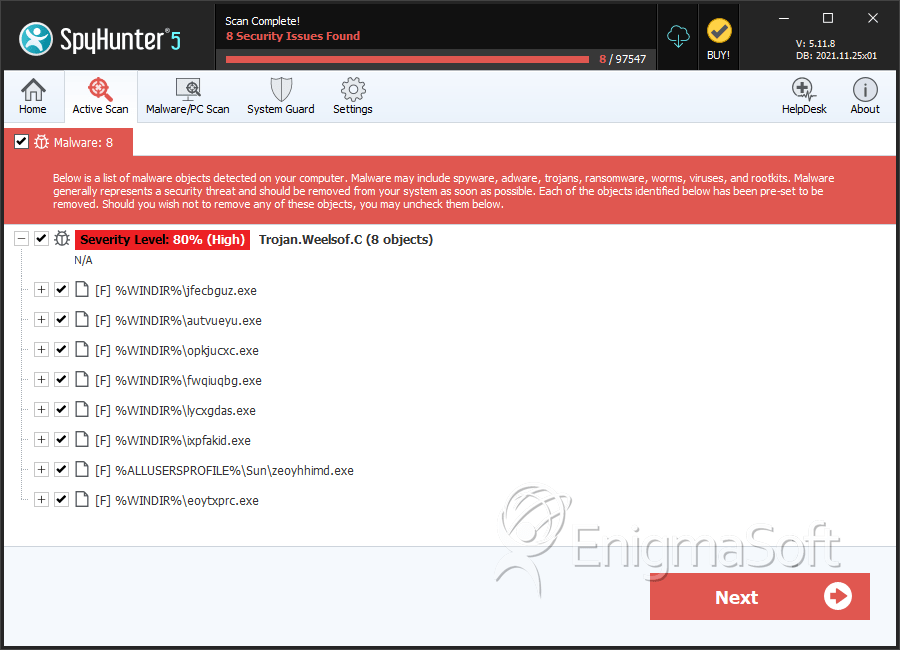
SpyHunter Detects & Remove Trojan.Weelsof.C
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | jfecbguz.exe | a648b7e3a735d06996ac7a5ff9024f50 | 29 |
| 2. | autvueyu.exe | eb52bc9542f9a07fb0010b56fc170db9 | 9 |
| 3. | opkjucxc.exe | 9458b473b402e90cedc0a72bbc62b5fd | 8 |
| 4. | fwqiuqbg.exe | dee9361773b6b8d87d21dc5e2ecfd6e6 | 8 |
| 5. | lycxgdas.exe | 0334ff5700d419d92b351caea22c7c84 | 8 |
| 6. | ixpfakid.exe | b711ba1cd1f7d9a4597285154bbd75f8 | 6 |
| 7. | zeoyhhimd.exe | fc83d75fd55f9ce49802188a2e37c1a7 | 6 |
| 8. | eoytxprc.exe | e5bb7da7795462275eb14635117c3df2 | 4 |
| 9. | ankitomnh.exe | 31cd61043694885680cc64b790270c2f | 4 |
| 10. | thvdolwtq.exe | 3c351ea8d3159b3c599c8e997515e9ab | 4 |
| 11. | catodhuv.exe | f70809ca9664ad2ac82159ea03e475ad | 3 |
| 12. | lpdvdbyr.exe | f69783ed12b8dc7e0911e93113f84ce4 | 3 |
| 13. | engmimmv.exe | 19c33c3e0abcafcdb3c5a6a7b87d0df9 | 3 |
| 14. | jnurjipg.exe | 4e13adf6b0ff75df5949f7835c3d6c84 | 2 |
| 15. | txdiauwj.exe | 36ae780cfc36dce174fed87ae70baf70 | 2 |
| 16. | lkzqzugo.exe | 8fcc3b27a72d1248b2710923c8d01ace | 2 |
| 17. | ccasrhii.exe | 103a634db73acfb56c3b7a983d2f8f5a | 2 |
| 18. | zwhswghw.exe | f24584dc77fa341ef65bf6a508fc6eeb | 2 |
| 19. | cxinpnkm.exe | 42ecb9e0fdc47b373bfd6ef751e0758b | 2 |
| 20. | mkomnhsw.exe | fd42340666554e43a4dacea8622224ee | 2 |
| 21. | yncfthon.exe | f05bb88058fe8f32b68cb8fb39ca9642 | 2 |
| 22. | ktijakes.exe | 5c4ecb974a08f961788127aaef51b247 | 2 |
| 23. | qgcbqhhf.exe | c586217ec0ee21272bd8a398304eb60e | 2 |
| 24. | ukonvvrde.exe | 9a76a0d0cd0e478eeadf1a83c5439d62 | 2 |
| 25. | dwuycpxu.exe | 906943411613a3056e5df8e5b7d93041 | 1 |
| 26. | uzfqzrcs.exe | e7fcf9a6a7aa1965148e352103af0899 | 1 |
| 27. | gkbtbudes.exe | 5accf7353b949e992cf5f5f0df396717 | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.