Trojan.Triosir
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 22,577 |
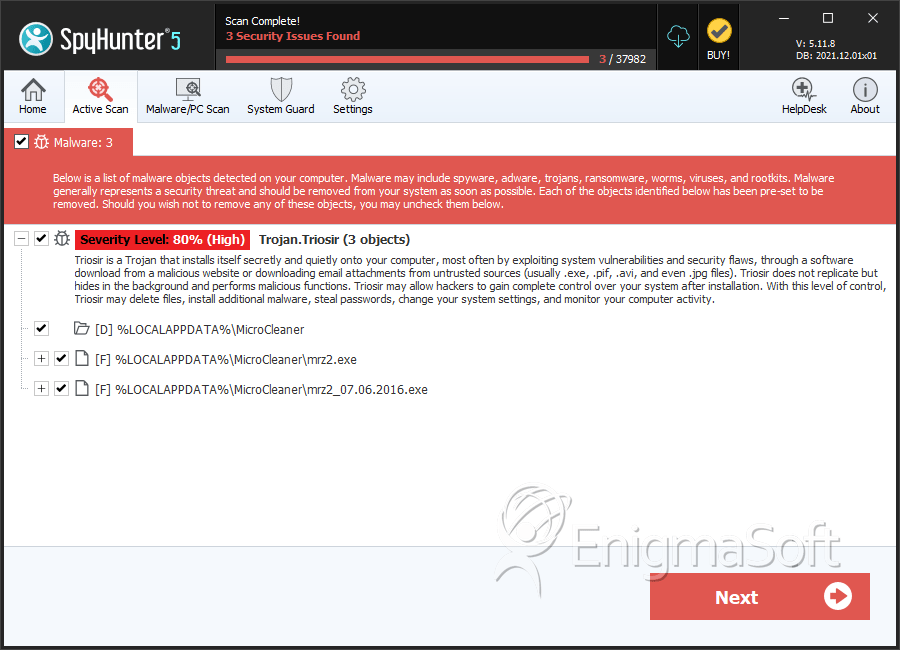
| Threat Level: | 80 % (High) |
| Infected Computers: | 707 |
| First Seen: | July 9, 2016 |
| Last Seen: | November 25, 2025 |
| OS(es) Affected: | Windows |
Table of Contents
SpyHunter Detects & Remove Trojan.Triosir
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | mrz2.exe | ae9c628238ccbb34a4be2f32880a1217 | 81 |
| 2. | mrz2_07.06.2016.exe | 6f01fa359a0b6c5e424e8e46ccba53f3 | 27 |
Directories
Trojan.Triosir may create the following directory or directories:
| %LOCALAPPDATA%\MicroCleaner |
Analysis Report
General information
| Family Name: | Trojan.Triosir |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
7fec4596271a0bb8138d44e3a6c660f3
SHA1:
dcc75956bc54024acd751a8ac123dde6a82a206e
SHA256:
EF116E103173B17D00BD04C854E8C71B97B77EABC198D33907426232B3A69E6C
File Size:
255.94 KB, 255944 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| File Description | Installer |
| File Version | 2.0.0.1 |
| Internal Name | Installer.exe |
| Legal Copyright | Copyright (C) 2014 |
| Original Filename | Installer.exe |
| Product Name | Installer |
| Product Version | 2.0.0.1 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| TRIORIS LLC | UTN-USERFirst-Object | Root Not Trusted |