Trojan.Tapaoux
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 9 |
| First Seen: | November 24, 2011 |
| Last Seen: | August 22, 2018 |
| OS(es) Affected: | Windows |
Trojan.Tapaoux is a damaging Trojan that downloads and installs other malware infections on to the corrupted PC system. Trojan.Tapaoux tries to exploit the Adobe Reader 'CoolType.dll' TTF Font Remote Code Execution Vulnerability (BID 43057). When Trojan.Tapaoux infiltrates into the targeted computer system, it will firstly disguise itself from the detection of your anti-virus software. Before Trojan.Tapaoux is executed, it is difficult to detect it. Once Trojan.Tapaoux is executed, it adds a DLL file, an executable file and a system driver. Trojan.Tapaoux will run automatically each time you start your PC. When Trojan.Tapaoux downloads malicious files, your anti-virus software may display a fake security alert. Trojan.Tapaoux will slow down your computer and make your Internet speed unstable. Trojan.Tapaoux will also change your homepage and redirect your browser to malicious websites. Trojan.Tapaoux will also gather your personal information and forward it to remote attackers. Uninstall Trojan.Tapaoux immediately after detection.
Table of Contents
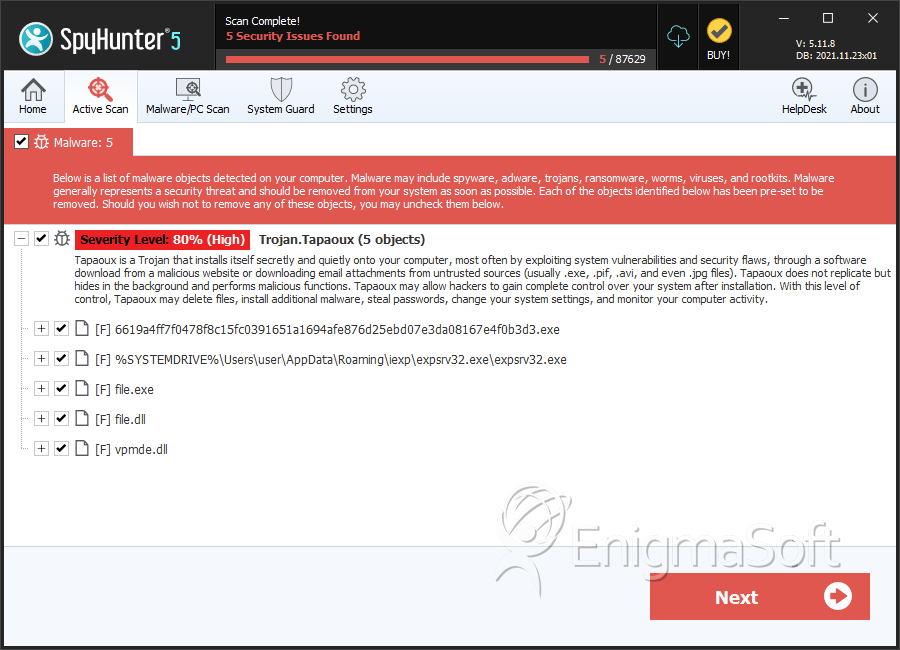
SpyHunter Detects & Remove Trojan.Tapaoux
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 6619a4ff7f0478f8c15fc0391651a1694afe876d25ebd07e3da08167e4f0b3d3.exe | 60af79fb0bd2c9f33375035609c931cb | 3 |
| 2. | expsrv32.exe | 653ffc574a13c4bc8337c688124fd0bf | 2 |
| 3. | file.exe | c2915bece3269b7a8dac1e2745063b49 | 1 |
| 4. | vpmde.dll | 566e92f79497a3c6136b815c9960b898 | 1 |
| 5. | %System%\schechk.exe | ||
| 6. | %System%\sisraid3.sys | ||
| 7. | %System%\securx86.sys | ||
| 8. | %System%\hwpolicy.dll | ||
| 9. | %System%\ql5200.sys | ||
| 10. | %System%\sscore1.sys | ||
| 11. | %System%\npidsz4.sys | ||
| 12. | %System%\schechk.sys | ||
| 13. | %System%\expsrv32.sys | ||
| 14. | %System%\hwpolicy.sys | ||
| 15. | %System%\imagepk.sys | ||
| 16. | %System%\schechk.bin | ||
| 17. | file.dll | 387128c489a66a70c7ed76b27f1dd4e2 | 0 |
Registry Details
URLs
Trojan.Tapaoux may call the following URLs:
| ebizcentres.com/system32/list4/yahoo/banne[DELETED] |
| re.policy-forums.org/ol/yahoo/banne[DELETED] |
