Trojan.Reder.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
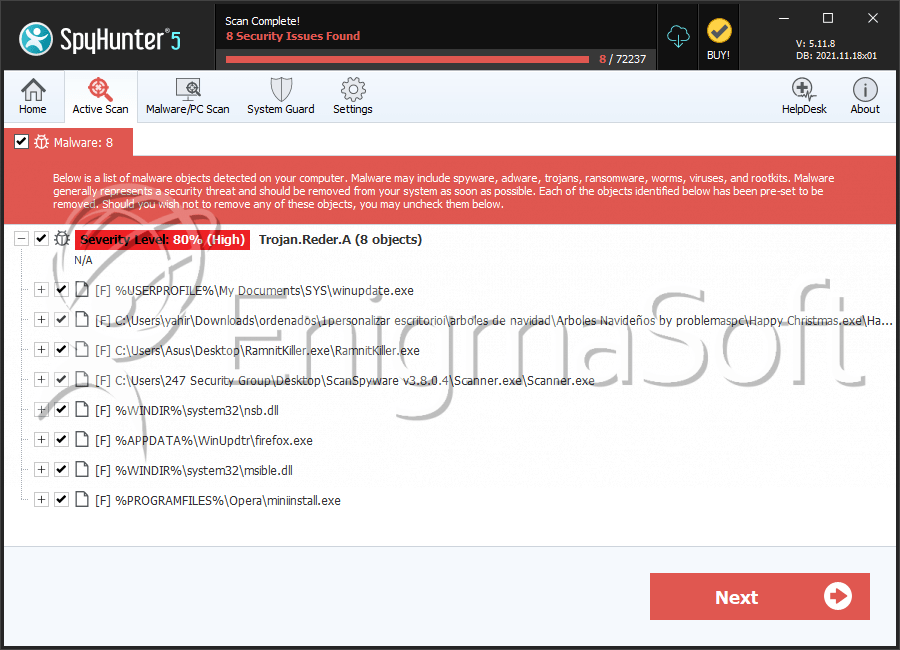
| Threat Level: | 80 % (High) |
| Infected Computers: | 222 |
| First Seen: | March 1, 2012 |
| Last Seen: | May 6, 2023 |
| OS(es) Affected: | Windows |
Trojan.Reder.A is a surreptitious Trojan that can drop other harmful software programs to the infected PC. Trojan.Reder.A can steal your confidential information. Trojan.Reder.A uses a rootkit technique which disguises infected files of a Trojan and make it hard to find and eliminate it. Trojan.Reder.A adds malevolent files and modifies the Windows registry so that it can launch automatically every time you turn your PC on. Trojan.Reder.A enables remote communication between the targeted PC and other computer systems and permits outbound communication to IM chat rooms. Trojan.Reder.A can also read your emails address and Outlook address book information, which permits Trojan.Reder.A send spam emails to multiple Windows users. Trojan.Reder.A has a capability of logging your keyboard input, screen content or mouse activity. Trojan.Reder.A can add additional menu selections to the right-click menu. Trojan.Reder.A can modify your browser settings by changing ActiveX component. To secure your computer, remove Trojan.Reder.A as soon as possible.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| AVG | Agent3.YKL |
| Fortinet | W32/Agent.OEDY!tr |
| AntiVir | TR/Kazy.29693.5 |
| Kaspersky | Trojan.Win32.Agent.oedy |
| Avast | Win32:Agent-ANCG [Trj] |
| McAfee | Artemis!B9BADBF603E4 |
| AVG | Generic21.BROV |
| Sophos | Christmas Countdown |
| NOD32 | a variant of Win32/XmasAds.A |
| AntiVir | TR/Offend.6265065.1 |
| Sophos | Mal/Behav-058 |
| BitDefender | Trojan.Generic.6265065 |
| McAfee | Artemis!04124F08C384 |
| Panda | Application/ScanSpyware |
| Ikarus | Trojan.Fake |
SpyHunter Detects & Remove Trojan.Reder.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | winupdate.exe | 51ae11ab3d4a3bc961152fd33d769b09 | 59 |
| 2. | Happy Christmas.exe | d219af7da99ecf12dcb2123fb76f41a6 | 53 |
| 3. | RamnitKiller.exe | 04124f08c384053d8976cf27aa521d2b | 29 |
| 4. | Scanner.exe | 95ba5e8ea16f43508b3f2aaeb54db017 | 8 |
| 5. | nsb.dll | b9badbf603e435877ef4385a982758dd | 7 |
| 6. | firefox.exe | 5b4d1240b0a0036e12514070d9ab14ff | 3 |
| 7. | msible.dll | 0f6d22e33f06083f76f5de4aee6b74f1 | 2 |
| 8. | miniinstall.exe | f1fed01999291f6ea4d4446583ff90c9 | 1 |
| 9. | msvcrr100.dll | ||
| 10. | RamnitKiller.exe | ||
| 11. | Adobeup.DLL |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.