Trojan.Rannoh
Trojan.Rannoh Image
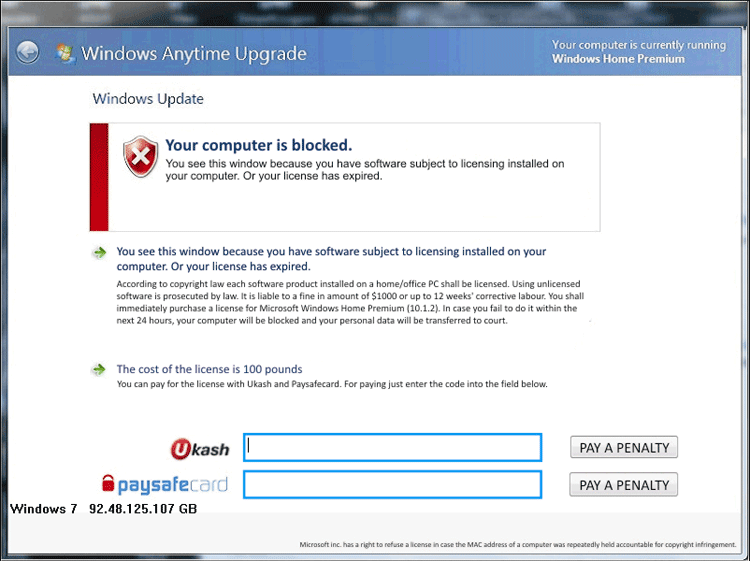
There's a Trojan infection that encrypts files on the victim's computer system called Trojan.Rannoh. Trojan.Rannoh will extort the victim by forcing them to pay for a decryption code if they want to gain back control of their files. Fortunately, PC security analysts work constantly to distribute tools that can help computer users that have become victims of ransomware Trojans such as Trojan.Rannoh. Usually, in order to deal with a Trojan.Rannoh infection it is necessary first to remove the Trojan itself from the infected computer system and then to proceed with a decryption tool.
Table of Contents
Understanding Trojan.Rannoh Attack
In 2012 various ransomware Trojans like Trojan.Rannoh have surfaced, carrying out the same basic scam. While some will simply function as Winlockers, blocking access to the infected computer system and pretending that its files have been encrypted, others use a simple encryption algorithm to actually encrypt various types of files. Trojan.Rannoh also contains components that block applications or Windows components that could be helpful in its removal. For example, Trojan.Rannoh can block various anti-virus programs as well as prevent access to Windows Restore or to the Windows Task Manager. Usually, it will be necessary to bypass Trojan.Rannoh's defenses before one is able to use an anti-malware program to eliminate the infection. To do this it is advisable to start up Windows from a removable drive, a network-based operating system or in Safe Mode (in most versions of Windows, this can be accessed by pressing F8 during start-up).
Getting Rid of a Trojan.Rannoh Trojan Infection
Unfortunately, removing Trojan.Rannoh itself will not decrypt any affected files. However, ESG security analysts indicate that this encryption does not cause any permanent damage to your files and that it can be reversed. At the time of this writing, no free tools for removing Trojan.Rannoh's encryption have been released. However, paying Trojan.Rannoh's ransom does not guarantee that it will remove the encryption, and in fact will place your credit card information in the hands of criminals. Trojan.Rannoh was first detected in early May – usually, PC security analysts will release a decryption utility within three or four weeks after the ransomware responsible for the attack is first detected. ESG malware researchers recommend removing Trojan.Rannoh and waiting for a decryption utility to be released in order to gain access to any encrypted files on your computer system.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %UserProfile%\Local Settings\Temp\ | |
| 2. | %WinDir%\System32 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.