Trojan.Proxy-Bunitu
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
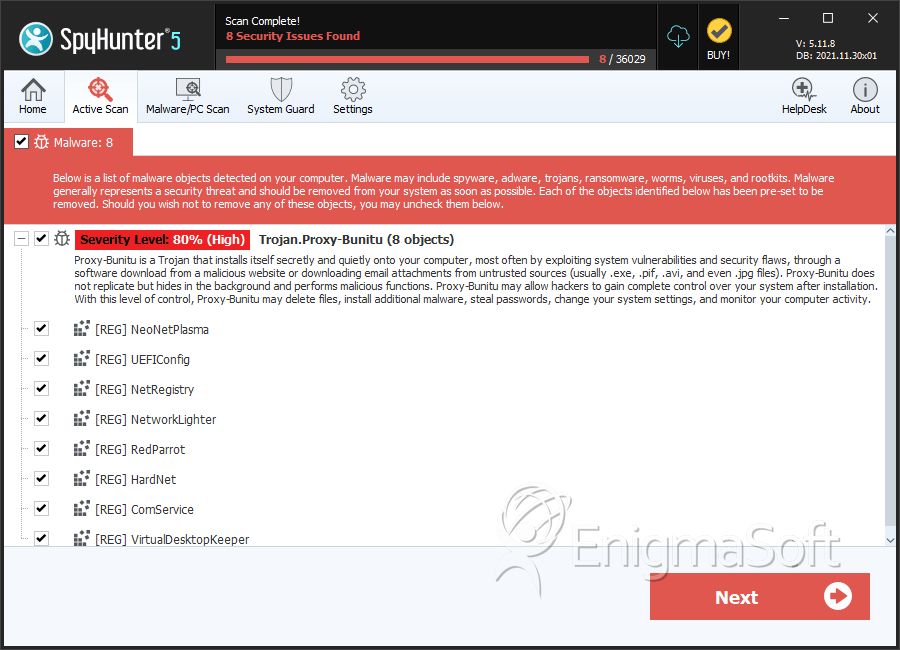
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,650 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 4,568 |
| First Seen: | February 6, 2014 |
| Last Seen: | June 27, 2023 |
| OS(es) Affected: | Windows |
Trojan.Proxy-Bunitu is the name of a vicious threat that may put some hackers in control of your PC. Trojan.Proxy-Bunitu is a member of the notorious family Win32/Bunitu. When it comes to such high-level cyber threats, your intentions should be aimed towards preventing their access to your system. Otherwise, by the time you delete them, your information may already be collected and used for harmful goals. To keep Trojan.Proxy-Bunitu away, you first need to know how it may infect your PC. This cyber threat may be hidden into some seemingly innocent email attachment. It is not necessarily the payload of this threat an executable file (.exe) or a dynamic link library (.dll). Any file, regardless of its extension, may possess harmful codes, including Office documents, images and music. For this reason, you should never download or open files sent from someone you don't know.
The operators of Trojan.Proxy-Bunitu also may conceal it in some fake Java or FlashPlayer updates. When the harmful application gets access to your machine, it may make a few changes. Trojan.Proxy-Bunitu may create some Registry keys that allow it to launch when you start your PC and also trouble its removal process. Trojan.Proxy-Bunitu may interfere with other programs you have, especially those that can reveal its presence. The people behind this attack may eventually use your PC as a proxy server. This means that they will control your Internet traffic. As a result, your browsers may be forced to load threatening sites to download additional threats. Trojan.Proxy-Bunitu also may access some of your files and transfer them to the Command and Control (C&C) servers of con artists. If you have opened unverified email attachments or installed questionable software recently, you may be in trouble. You should scan your system immediately to make sure Trojan.Proxy-Bunitu isn't working.
Table of Contents
SpyHunter Detects & Remove Trojan.Proxy-Bunitu
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svchostx64.exe | 76fc0466dae89a48a592fd3060ac8303 | 11 |
| 2. | svchostx64.exe | a0ebfb2654e7cd1a2a5f3f321ad858b8 | 6 |
| 3. | svchostx64.exe | ff23030732987a5b57a9209a9c976b76 | 4 |
| 4. | rundll3.exe | 4cef794e71b50772e9840a9700a2405f | 3 |
| 5. | svchostx64.exe | 8621ef97e6097e05d4a9ca5fbba3baae | 2 |
| 6. | svchostx64.exe | 4ba3d0cdd5919453b9667430a2d97444 | 1 |
| 7. | file.exe | c5cc7ec50e8512cf36b5e7e3886cf493 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.