Trojan.Pondfull
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
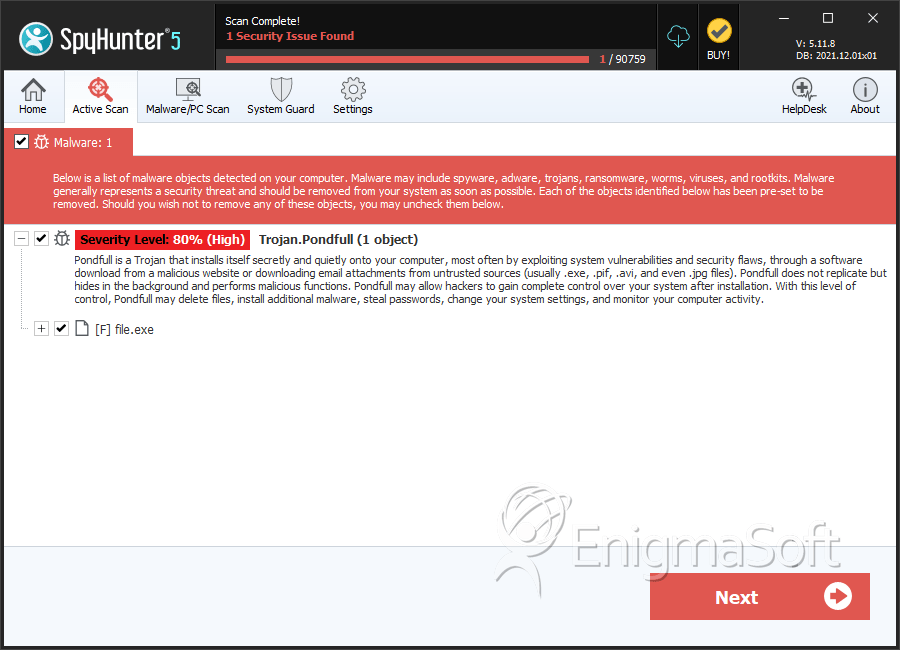
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 11 |
| First Seen: | March 24, 2016 |
| Last Seen: | June 1, 2023 |
| OS(es) Affected: | Windows |
Trojan.Pondfull (also seen as Worm:Win32/Pondfull.A) is a generic cyber threat that was identified back in September 2013 and appears to receive updates each year. Programs that are classified as Trojan.Pondfull are distributed to users via seemingly lost USB drives, cracked electronic games, and pirated shareware. Trojan.Pondfull is known to be installed to the Temp folder under a random name like '4Mk6BYfhCH.exe' (MD5: f389700236a67533f78caf92a9eb7f6df38). Trojan.Pondfull is observed to run on 32-bit and 64-bit systems, as well as run commands through CMD.exe (the command line tool on Windows) to facilitate its operations.
Programs that are classified as Trojan.Pondfull may be used for Remote Desktop Access and keylogging by threat actors. There have been cases where Trojan.Pondfull was used as a first-step Trojan and allowed threat actors to drop several other unsafe programs. The Trojan.Pondfull malware may maintain a hidden folder in the Temp directory and inject code into legitimate DLL resources like 'KERNEL32.dll' and 'msvcrt.dll.' The Trojan.Pondfull cyber-threat might make changes to the Registry and remove programs without your knowledge. Trojan.Pondfull may be used to download files from a remote host in the background and attempt to circumvent firewall protection. Computer security experts recommend users disable autorun functionality on Windows by following the guide at hxxps://support.microsoft[.]com/en-us/help/967715/how-to-disable-the-autorun-functionality-in-windows and always scan connected USB drives. AV companies use the following detection names for Trojan.Pondfull:
Backdoor.Win32.Xtreme.32768[h]
Gen:Variant.Zusy.107719
Packed-DW!F389700236A6
Rootkit.TDSS
Troj/TDSS-IW
TrojWare.Win32.Injector.KWA
Trojan ( 004a54ec1 )
Trojan.Inject1.14023
Trojan[Packed]/Win32.Tdss
W32/A-5f58ee87!Eldorado
W32/Autorun.C!tr
WORM_STASER.SM
Win32.Worm.Autorun.Ecjx
Win32/Trojan.97a
Worm.AutoRun.Win32.102264
Worm.Win32.Pondfull.b (v)
Worm:Win32/Pondfull.B
Table of Contents
SpyHunter Detects & Remove Trojan.Pondfull
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | f389700236a67533f78caf92a9eb7f6d | 0 |

